mirror of
https://github.com/alibaba/higress.git
synced 2026-02-25 21:21:01 +08:00
Compare commits
143 Commits
v1.3.3
...
plugins/wa
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
6a40d83ec0 | ||
|
|
2807ddfbb7 | ||
|
|
6e4ade05a8 | ||
|
|
bdd050b926 | ||
|
|
38ddc49360 | ||
|
|
26ec0d3d55 | ||
|
|
909f8bc719 | ||
|
|
863d0e5872 | ||
|
|
3e7a63bd9b | ||
|
|
206152daa0 | ||
|
|
812edf1490 | ||
|
|
b00f79f3af | ||
|
|
ed05da13f4 | ||
|
|
53bccf89f4 | ||
|
|
51b9d9ec4b | ||
|
|
50f79c9099 | ||
|
|
93966bf14b | ||
|
|
ffa690994b | ||
|
|
ca1ad1dc73 | ||
|
|
e09edff827 | ||
|
|
2fee28d4e8 | ||
|
|
78418b50ff | ||
|
|
7fcb608fce | ||
|
|
10f1adc730 | ||
|
|
e4d535ea65 | ||
|
|
76b5f2af79 | ||
|
|
fc6a6aad89 | ||
|
|
af8eff2bd6 | ||
|
|
d91b22f8c2 | ||
|
|
f4a73b986c | ||
|
|
bff21b2307 | ||
|
|
33013d07f4 | ||
|
|
22a3e7018b | ||
|
|
2ff56c82f8 | ||
|
|
9b50343618 | ||
|
|
f9994237d1 | ||
|
|
ae54318557 | ||
|
|
0ec6719751 | ||
|
|
dfa1be3b47 | ||
|
|
95aa69cb95 | ||
|
|
5333031f31 | ||
|
|
31242c36ba | ||
|
|
3119ec8e24 | ||
|
|
42c9c3d824 | ||
|
|
8736188e6a | ||
|
|
559a109ae5 | ||
|
|
8043780de0 | ||
|
|
333f9b48f3 | ||
|
|
5c7736980c | ||
|
|
2031c659c2 | ||
|
|
03d2f01274 | ||
|
|
6577ae8822 | ||
|
|
a8c74c8302 | ||
|
|
a787088c0e | ||
|
|
e68b5c86c4 | ||
|
|
5fec6e9ab7 | ||
|
|
3b2196d0f8 | ||
|
|
a592b2b103 | ||
|
|
37fb2a52c0 | ||
|
|
41491166e3 | ||
|
|
29baf8576e | ||
|
|
f1cadcbd73 | ||
|
|
8c817cf80a | ||
|
|
a67ce1d223 | ||
|
|
fb18782a80 | ||
|
|
026840b59b | ||
|
|
75599ef804 | ||
|
|
fe039d46f2 | ||
|
|
6c7b1757b6 | ||
|
|
dfc9ae412e | ||
|
|
b4f72d3584 | ||
|
|
cba2890e14 | ||
|
|
e844daea66 | ||
|
|
717e3bf51f | ||
|
|
ba0df237da | ||
|
|
08e56780f0 | ||
|
|
a45748bb0b | ||
|
|
97cf58e973 | ||
|
|
4d6aa25b19 | ||
|
|
25c2f6e42e | ||
|
|
ed55b65443 | ||
|
|
d64c266ee4 | ||
|
|
32b602704e | ||
|
|
3128df9abd | ||
|
|
cc6043de15 | ||
|
|
c9f1f94130 | ||
|
|
5554189851 | ||
|
|
eb1f99391a | ||
|
|
7d4ab04030 | ||
|
|
9c112a03db | ||
|
|
9be4f7d587 | ||
|
|
50a219ed01 | ||
|
|
e55a3c0f5b | ||
|
|
e0e4fc3507 | ||
|
|
3967eec852 | ||
|
|
f537a1c3ea | ||
|
|
b652f3e666 | ||
|
|
5140372159 | ||
|
|
f277d4f6ae | ||
|
|
ae20420179 | ||
|
|
a138a037ad | ||
|
|
021387c9d3 | ||
|
|
ea0a694d81 | ||
|
|
8028fe03ca | ||
|
|
a68dde0b91 | ||
|
|
48c3db85c4 | ||
|
|
7e85065832 | ||
|
|
7967f5db70 | ||
|
|
5026973d59 | ||
|
|
7097eef6ba | ||
|
|
fae222806b | ||
|
|
c63cdb62ea | ||
|
|
e43f5d106f | ||
|
|
29c95ea557 | ||
|
|
73d5cc3f1d | ||
|
|
c1ddbcef7c | ||
|
|
dd39c87311 | ||
|
|
612c94dd8a | ||
|
|
e67ed481cf | ||
|
|
ccea33655f | ||
|
|
ad4cfdbd40 | ||
|
|
3598c21da0 | ||
|
|
a624351f84 | ||
|
|
c41264816e | ||
|
|
acd80d2528 | ||
|
|
073c10df77 | ||
|
|
90f89cf588 | ||
|
|
879192cf99 | ||
|
|
d3d000753d | ||
|
|
b8a01113e3 | ||
|
|
0bb9e6dd89 | ||
|
|
ecdd077c72 | ||
|
|
e971faeb0b | ||
|
|
77013e28b6 | ||
|
|
9faa5f37d1 | ||
|
|
665d9fa943 | ||
|
|
a71ecf41d1 | ||
|
|
b825f9176f | ||
|
|
d35d23e2d5 | ||
|
|
6d1e09c146 | ||
|
|
87c39d393f | ||
|
|
c97260c4a9 | ||
|
|
5e509e7032 |
84
.github/workflows/build-and-test-plugin.yaml
vendored
84
.github/workflows/build-and-test-plugin.yaml
vendored
@@ -7,19 +7,20 @@ on:
|
||||
- 'plugins/**'
|
||||
- 'test/**'
|
||||
pull_request:
|
||||
branches: ["*"]
|
||||
branches: [ "*" ]
|
||||
paths:
|
||||
- 'plugins/**'
|
||||
- 'test/**'
|
||||
workflow_dispatch: ~
|
||||
|
||||
jobs:
|
||||
lint:
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- uses: actions/checkout@v3
|
||||
- uses: actions/setup-go@v3
|
||||
with:
|
||||
go-version: 1.19
|
||||
- uses: actions/checkout@v3
|
||||
- uses: actions/setup-go@v3
|
||||
with:
|
||||
go-version: 1.19
|
||||
# There are too many lint errors in current code bases
|
||||
# uncomment when we decide what lint should be addressed or ignored.
|
||||
# - run: make lint
|
||||
@@ -31,40 +32,53 @@ jobs:
|
||||
# TODO(Xunzhuo): Enable C WASM Filters in CI
|
||||
wasmPluginType: [ GO ]
|
||||
steps:
|
||||
- uses: actions/checkout@v3
|
||||
|
||||
- name: "Setup Go"
|
||||
uses: actions/setup-go@v3
|
||||
with:
|
||||
go-version: 1.19
|
||||
- uses: actions/checkout@v3
|
||||
|
||||
- name: Setup Golang Caches
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
~/.cache/go-build
|
||||
~/go/pkg/mod
|
||||
key: ${{ runner.os }}-go-${{ github.run_id }}
|
||||
restore-keys: |
|
||||
${{ runner.os }}-go
|
||||
|
||||
- name: Setup Submodule Caches
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
envoy
|
||||
istio
|
||||
- name: Free Up GitHub Actions Ubuntu Runner Disk Space 🔧
|
||||
uses: jlumbroso/free-disk-space@main
|
||||
with:
|
||||
tool-cache: false
|
||||
android: true
|
||||
dotnet: true
|
||||
haskell: true
|
||||
large-packages: true
|
||||
swap-storage: true
|
||||
|
||||
- name: "Setup Go"
|
||||
uses: actions/setup-go@v3
|
||||
with:
|
||||
go-version: 1.19
|
||||
|
||||
- name: Setup Golang Caches
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
~/.cache/go-build
|
||||
~/go/pkg/mod
|
||||
key: ${{ runner.os }}-go-${{ github.run_id }}
|
||||
restore-keys: |
|
||||
${{ runner.os }}-go
|
||||
|
||||
- name: Setup Submodule Caches
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
.git/modules
|
||||
key: ${{ runner.os }}-submodules-new-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-new
|
||||
|
||||
- run: git stash # restore patch
|
||||
key: ${{ runner.os }}-submodules-cache-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-cache
|
||||
|
||||
- name: "Run Ingress WasmPlugins Tests"
|
||||
run: GOPROXY="https://proxy.golang.org,direct" PLUGIN_TYPE=${{ matrix.wasmPluginType }} make higress-wasmplugin-test
|
||||
- run: git stash # restore patch
|
||||
|
||||
- name: "Run Ingress WasmPlugins Tests"
|
||||
uses: nick-fields/retry@v3
|
||||
with:
|
||||
timeout_minutes: 25
|
||||
max_attempts: 3
|
||||
retry_on: error
|
||||
command: GOPROXY="https://proxy.golang.org,direct" PLUGIN_TYPE=${{ matrix.wasmPluginType }} make higress-wasmplugin-test
|
||||
|
||||
publish:
|
||||
runs-on: ubuntu-latest
|
||||
needs: [higress-wasmplugin-test]
|
||||
needs: [ higress-wasmplugin-test ]
|
||||
steps:
|
||||
- uses: actions/checkout@v3
|
||||
- uses: actions/checkout@v3
|
||||
|
||||
20
.github/workflows/build-and-test.yaml
vendored
20
.github/workflows/build-and-test.yaml
vendored
@@ -36,11 +36,9 @@ jobs:
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
envoy
|
||||
istio
|
||||
.git/modules
|
||||
key: ${{ runner.os }}-submodules-new-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-new
|
||||
key: ${{ runner.os }}-submodules-cache-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-cache
|
||||
|
||||
- run: git stash # restore patch
|
||||
|
||||
@@ -50,7 +48,7 @@ jobs:
|
||||
- name: Upload coverage to Codecov
|
||||
uses: codecov/codecov-action@v3
|
||||
with:
|
||||
fail_ci_if_error: true
|
||||
fail_ci_if_error: false
|
||||
files: ./coverage.xml
|
||||
verbose: true
|
||||
|
||||
@@ -82,11 +80,9 @@ jobs:
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
envoy
|
||||
istio
|
||||
.git/modules
|
||||
key: ${{ runner.os }}-submodules-new-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-new
|
||||
key: ${{ runner.os }}-submodules-cache-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-cache
|
||||
|
||||
- run: git stash # restore patch
|
||||
|
||||
@@ -130,11 +126,9 @@ jobs:
|
||||
uses: actions/cache@v3
|
||||
with:
|
||||
path: |-
|
||||
envoy
|
||||
istio
|
||||
.git/modules
|
||||
key: ${{ runner.os }}-submodules-new-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-new
|
||||
key: ${{ runner.os }}-submodules-cache-${{ github.run_id }}
|
||||
restore-keys: ${{ runner.os }}-submodules-cache
|
||||
|
||||
- run: git stash # restore patch
|
||||
|
||||
|
||||
30
.github/workflows/build-image-and-push.yaml
vendored
30
.github/workflows/build-image-and-push.yaml
vendored
@@ -20,6 +20,16 @@ jobs:
|
||||
with:
|
||||
fetch-depth: 1
|
||||
|
||||
- name: Free Up GitHub Actions Ubuntu Runner Disk Space 🔧
|
||||
uses: jlumbroso/free-disk-space@main
|
||||
with:
|
||||
tool-cache: false
|
||||
android: true
|
||||
dotnet: true
|
||||
haskell: true
|
||||
large-packages: true
|
||||
swap-storage: true
|
||||
|
||||
- name: "Setup Go"
|
||||
uses: actions/setup-go@v3
|
||||
with:
|
||||
@@ -86,6 +96,16 @@ jobs:
|
||||
with:
|
||||
fetch-depth: 1
|
||||
|
||||
- name: Free Up GitHub Actions Ubuntu Runner Disk Space 🔧
|
||||
uses: jlumbroso/free-disk-space@main
|
||||
with:
|
||||
tool-cache: false
|
||||
android: true
|
||||
dotnet: true
|
||||
haskell: true
|
||||
large-packages: true
|
||||
swap-storage: true
|
||||
|
||||
- name: "Setup Go"
|
||||
uses: actions/setup-go@v3
|
||||
with:
|
||||
@@ -153,6 +173,16 @@ jobs:
|
||||
with:
|
||||
fetch-depth: 1
|
||||
|
||||
- name: Free Up GitHub Actions Ubuntu Runner Disk Space 🔧
|
||||
uses: jlumbroso/free-disk-space@main
|
||||
with:
|
||||
tool-cache: false
|
||||
android: true
|
||||
dotnet: true
|
||||
haskell: true
|
||||
large-packages: true
|
||||
swap-storage: true
|
||||
|
||||
- name: "Setup Go"
|
||||
uses: actions/setup-go@v3
|
||||
with:
|
||||
|
||||
37
.github/workflows/release-hgctl.yaml
vendored
Normal file
37
.github/workflows/release-hgctl.yaml
vendored
Normal file
@@ -0,0 +1,37 @@
|
||||
name: Release hgctl to GitHub
|
||||
|
||||
on:
|
||||
push:
|
||||
tags:
|
||||
- "v*.*.*"
|
||||
workflow_dispatch: ~
|
||||
|
||||
jobs:
|
||||
release-hgctl:
|
||||
runs-on: ubuntu-latest
|
||||
env:
|
||||
HGCTL_VERSION: ${{github.ref_name}}
|
||||
steps:
|
||||
- uses: actions/checkout@v3
|
||||
|
||||
- name: Build hgctl latest multiarch binaries
|
||||
run: |
|
||||
GOPROXY="https://proxy.golang.org,direct" make build-hgctl-multiarch
|
||||
tar -zcvf hgctl_${{ env.HGCTL_VERSION }}_linux_amd64.tar.gz out/linux_amd64/
|
||||
tar -zcvf hgctl_${{ env.HGCTL_VERSION }}_linux_arm64.tar.gz out/linux_arm64/
|
||||
tar -zcvf hgctl_${{ env.HGCTL_VERSION }}_darwin_amd64.tar.gz out/darwin_amd64/
|
||||
tar -zcvf hgctl_${{ env.HGCTL_VERSION }}_darwin_arm64.tar.gz out/darwin_arm64/
|
||||
zip -q -r hgctl_${{ env.HGCTL_VERSION }}_windows_amd64.zip out/windows_amd64/
|
||||
zip -q -r hgctl_${{ env.HGCTL_VERSION }}_windows_arm64.zip out/windows_arm64/
|
||||
|
||||
- name: Upload hgctl packages to the GitHub release
|
||||
uses: softprops/action-gh-release@v1
|
||||
if: startsWith(github.ref, 'refs/tags/')
|
||||
with:
|
||||
files: |
|
||||
hgctl_${{ env.HGCTL_VERSION }}_linux_amd64.tar.gz
|
||||
hgctl_${{ env.HGCTL_VERSION }}_linux_arm64.tar.gz
|
||||
hgctl_${{ env.HGCTL_VERSION }}_darwin_amd64.tar.gz
|
||||
hgctl_${{ env.HGCTL_VERSION }}_darwin_arm64.tar.gz
|
||||
hgctl_${{ env.HGCTL_VERSION }}_windows_amd64.zip
|
||||
hgctl_${{ env.HGCTL_VERSION }}_windows_arm64.zip
|
||||
@@ -26,6 +26,7 @@ header:
|
||||
- 'VERSION'
|
||||
- 'tools/'
|
||||
- 'test/README.md'
|
||||
- 'test/README_CN.md'
|
||||
- 'cmd/hgctl/config/testdata/config'
|
||||
- 'pkg/cmd/hgctl/manifests'
|
||||
|
||||
|
||||
@@ -1,8 +1,8 @@
|
||||
/api @johnlanni @CH3CHO
|
||||
/envoy @gengleilei @johnlanni
|
||||
/istio @SpecialYang @johnlanni
|
||||
/pkg @SpecialYang @johnlanni @CH3CHO @Xunzhuo
|
||||
/plugins @johnlanni @WeixinX
|
||||
/pkg @SpecialYang @johnlanni @CH3CHO
|
||||
/plugins @johnlanni @WeixinX @CH3CHO
|
||||
/registry @NameHaibinZhang @2456868764 @johnlanni
|
||||
/test @Xunzhuo @2456868764 @CH3CHO
|
||||
/tools @johnlanni @Xunzhuo @2456868764
|
||||
|
||||
@@ -73,6 +73,7 @@
|
||||
* [分支定义](#分支定义)
|
||||
* [提交规则](#提交规则)
|
||||
* [PR说明](#PR说明)
|
||||
* [开发前准备](#开发前准备)
|
||||
|
||||
### 工作区准备
|
||||
|
||||
@@ -168,6 +169,12 @@ git config --get user.email
|
||||
|
||||
PR 是更改 Higress 项目文件的唯一方法。为了帮助审查人更好地理解你的目的,PR 描述不能太详细。我们鼓励贡献者遵循 [PR 模板](./.github/PULL_REQUEST_TEMPLATE.md) 来完成拉取请求。
|
||||
|
||||
### 开发前准备
|
||||
|
||||
```shell
|
||||
make prebuild && go mod tidy
|
||||
```
|
||||
|
||||
## 测试用例贡献
|
||||
|
||||
任何测试用例都会受到欢迎。目前,Higress 功能测试用例是高优先级的。
|
||||
|
||||
@@ -169,6 +169,12 @@ No matter commit message, or commit content, we do take more emphasis on code re
|
||||
|
||||
PR is the only way to make change to Higress project files. To help reviewers better get your purpose, PR description could not be too detailed. We encourage contributors to follow the [PR template](./.github/PULL_REQUEST_TEMPLATE.md) to finish the pull request.
|
||||
|
||||
### Pre-development preparation
|
||||
|
||||
```shell
|
||||
make prebuild && go mod tidy
|
||||
```
|
||||
|
||||
## Test case contribution
|
||||
|
||||
Any test case would be welcomed. Currently, Higress function test cases are high priority.
|
||||
|
||||
@@ -15,7 +15,7 @@ GO_LDFLAGS += -X $(VERSION_PACKAGE).higressVersion=$(shell cat VERSION) \
|
||||
|
||||
GO ?= go
|
||||
|
||||
export GOPROXY ?= https://proxy.golang.com.cn,direct
|
||||
export GOPROXY ?= https://proxy.golang.org,direct
|
||||
|
||||
TARGET_ARCH ?= amd64
|
||||
|
||||
@@ -138,11 +138,11 @@ export ENVOY_TAR_PATH:=/home/package/envoy.tar.gz
|
||||
|
||||
external/package/envoy-amd64.tar.gz:
|
||||
# cd external/proxy; BUILD_WITH_CONTAINER=1 make test_release
|
||||
cd external/package; wget "https://github.com/alibaba/higress/releases/download/v1.3.2/envoy-amd64.tar.gz"
|
||||
cd external/package; wget -O envoy-amd64.tar.gz "https://github.com/alibaba/higress/releases/download/v1.4.0-rc.1/envoy-symbol-amd64.tar.gz"
|
||||
|
||||
external/package/envoy-arm64.tar.gz:
|
||||
# cd external/proxy; BUILD_WITH_CONTAINER=1 make test_release
|
||||
cd external/package; wget "https://github.com/alibaba/higress/releases/download/v1.3.2/envoy-arm64.tar.gz"
|
||||
cd external/package; wget -O envoy-arm64.tar.gz "https://github.com/alibaba/higress/releases/download/v1.4.0-rc.1/envoy-symbol-arm64.tar.gz"
|
||||
|
||||
build-pilot:
|
||||
cd external/istio; rm -rf out/linux_amd64; GOOS_LOCAL=linux TARGET_OS=linux TARGET_ARCH=amd64 BUILD_WITH_CONTAINER=1 make build-linux
|
||||
@@ -154,13 +154,13 @@ build-pilot-local:
|
||||
build-gateway: prebuild external/package/envoy-amd64.tar.gz external/package/envoy-arm64.tar.gz build-pilot
|
||||
cd external/istio; BUILD_WITH_CONTAINER=1 BUILDX_PLATFORM=true DOCKER_BUILD_VARIANTS=default DOCKER_TARGETS="docker.proxyv2" make docker
|
||||
|
||||
build-gateway-local: prebuild external/package/envoy-amd64.tar.gz external/package/envoy-arm64.tar.gz build-pilot
|
||||
build-gateway-local: prebuild external/package/envoy-amd64.tar.gz external/package/envoy-arm64.tar.gz
|
||||
cd external/istio; rm -rf out/linux_${GOARCH_LOCAL}; GOOS_LOCAL=linux TARGET_OS=linux BUILD_WITH_CONTAINER=1 BUILDX_PLATFORM=false DOCKER_BUILD_VARIANTS=default DOCKER_TARGETS="docker.proxyv2" make docker
|
||||
|
||||
build-istio: prebuild build-pilot
|
||||
cd external/istio; BUILD_WITH_CONTAINER=1 BUILDX_PLATFORM=true DOCKER_BUILD_VARIANTS=default DOCKER_TARGETS="docker.pilot" make docker
|
||||
|
||||
build-istio-local: prebuild build-pilot-local
|
||||
build-istio-local: prebuild
|
||||
cd external/istio; rm -rf out/linux_${GOARCH_LOCAL}; GOOS_LOCAL=linux TARGET_OS=linux BUILD_WITH_CONTAINER=1 BUILDX_PLATFORM=false DOCKER_BUILD_VARIANTS=default DOCKER_TARGETS="docker.pilot" make docker
|
||||
|
||||
build-wasmplugins:
|
||||
@@ -177,13 +177,13 @@ install: pre-install
|
||||
cd helm/higress; helm dependency build
|
||||
helm install higress helm/higress -n higress-system --create-namespace --set 'global.local=true'
|
||||
|
||||
ENVOY_LATEST_IMAGE_TAG ?= sha-53ff28c
|
||||
ISTIO_LATEST_IMAGE_TAG ?= sha-53ff28c
|
||||
ENVOY_LATEST_IMAGE_TAG ?= sha-93966bf
|
||||
ISTIO_LATEST_IMAGE_TAG ?= sha-b00f79f
|
||||
|
||||
install-dev: pre-install
|
||||
helm install higress helm/core -n higress-system --create-namespace --set 'controller.tag=$(TAG)' --set 'gateway.replicas=1' --set 'pilot.tag=$(ISTIO_LATEST_IMAGE_TAG)' --set 'gateway.tag=$(ENVOY_LATEST_IMAGE_TAG)' --set 'global.local=true'
|
||||
install-dev-wasmplugin: build-wasmplugins pre-install
|
||||
helm install higress helm/core -n higress-system --create-namespace --set 'controller.tag=$(TAG)' --set 'gateway.replicas=1' --set 'pilot.tag=$(ISTIO_LATEST_IMAGE_TAG)' --set 'gateway.tag=$(ENVOY_LATEST_IMAGE_TAG)' --set 'global.local=true' --set 'global.volumeWasmPlugins=true'
|
||||
helm install higress helm/core -n higress-system --create-namespace --set 'controller.tag=$(TAG)' --set 'gateway.replicas=1' --set 'pilot.tag=$(ISTIO_LATEST_IMAGE_TAG)' --set 'gateway.tag=$(ENVOY_LATEST_IMAGE_TAG)' --set 'global.local=true' --set 'global.volumeWasmPlugins=true' --set 'global.onlyPushRouteCluster=false'
|
||||
|
||||
uninstall:
|
||||
helm uninstall higress -n higress-system
|
||||
@@ -233,14 +233,30 @@ include tools/lint.mk
|
||||
.PHONY: gateway-conformance-test
|
||||
gateway-conformance-test:
|
||||
|
||||
# higress-conformance-test-prepare prepares the environment for higress conformance tests.
|
||||
.PHONY: higress-conformance-test-prepare
|
||||
higress-conformance-test-prepare: $(tools/kind) delete-cluster create-cluster docker-build kube-load-image install-dev
|
||||
|
||||
# higress-conformance-test runs ingress api conformance tests.
|
||||
.PHONY: higress-conformance-test
|
||||
higress-conformance-test: $(tools/kind) delete-cluster create-cluster docker-build kube-load-image install-dev run-higress-e2e-test delete-cluster
|
||||
|
||||
# higress-conformance-test-clean cleans the environment for higress conformance tests.
|
||||
.PHONY: higress-conformance-test-clean
|
||||
higress-conformance-test-clean: $(tools/kind) delete-cluster
|
||||
|
||||
# higress-wasmplugin-test-prepare prepares the environment for higress wasmplugin tests.
|
||||
.PHONY: higress-wasmplugin-test-prepare
|
||||
higress-wasmplugin-test-prepare: $(tools/kind) delete-cluster create-cluster docker-build kube-load-image install-dev-wasmplugin
|
||||
|
||||
# higress-wasmplugin-test runs ingress wasmplugin tests.
|
||||
.PHONY: higress-wasmplugin-test
|
||||
higress-wasmplugin-test: $(tools/kind) delete-cluster create-cluster docker-build kube-load-image install-dev-wasmplugin run-higress-e2e-test-wasmplugin delete-cluster
|
||||
|
||||
# higress-wasmplugin-test-clean cleans the environment for higress wasmplugin tests.
|
||||
.PHONY: higress-wasmplugin-test-clean
|
||||
higress-wasmplugin-test-clean: $(tools/kind) delete-cluster
|
||||
|
||||
# create-cluster creates a kube cluster with kind.
|
||||
.PHONY: create-cluster
|
||||
create-cluster: $(tools/kind)
|
||||
@@ -270,6 +286,17 @@ kube-load-image: $(tools/kind) ## Install the Higress image to a kind cluster us
|
||||
tools/hack/kind-load-image.sh docker.io/alihigress/httpbin 1.0.2
|
||||
tools/hack/kind-load-image.sh docker.io/charlie1380/eureka-registry-provider v0.3.0
|
||||
tools/hack/kind-load-image.sh docker.io/bitinit/eureka latest
|
||||
|
||||
# run-higress-e2e-test-setup starts to setup ingress e2e tests.
|
||||
.PHONT: run-higress-e2e-test-setup
|
||||
run-higress-e2e-test-setup:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@echo -e "\n\033[36mWaiting higress-controller to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go --ingress-class=higress --debug=true --test-area=setup
|
||||
|
||||
# run-higress-e2e-test starts to run ingress e2e tests.
|
||||
.PHONY: run-higress-e2e-test
|
||||
run-higress-e2e-test:
|
||||
@@ -278,9 +305,39 @@ run-higress-e2e-test:
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go --ingress-class=higress --debug=true
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go --ingress-class=higress --debug=true --test-area=all --execute-tests=$(TEST_SHORTNAME)
|
||||
|
||||
# run-higress-e2e-test starts to run ingress e2e tests.
|
||||
# run-higress-e2e-test-run starts to run ingress e2e conformance tests.
|
||||
.PHONY: run-higress-e2e-test-run
|
||||
run-higress-e2e-test-run:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@echo -e "\n\033[36mWaiting higress-controller to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go --ingress-class=higress --debug=true --test-area=run --execute-tests=$(TEST_SHORTNAME)
|
||||
|
||||
# run-higress-e2e-test-clean starts to clean ingress e2e tests.
|
||||
.PHONY: run-higress-e2e-test-clean
|
||||
run-higress-e2e-test-clean:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@echo -e "\n\033[36mWaiting higress-controller to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go --ingress-class=higress --debug=true --test-area=clean
|
||||
|
||||
# run-higress-e2e-test-wasmplugin-setup starts to prepare ingress e2e tests.
|
||||
.PHONY: run-higress-e2e-test-wasmplugin-setup
|
||||
run-higress-e2e-test-wasmplugin-setup:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@echo -e "\n\033[36mWaiting higress-controller to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go -isWasmPluginTest=true -wasmPluginType=$(PLUGIN_TYPE) -wasmPluginName=$(PLUGIN_NAME) --ingress-class=higress --debug=true --test-area=setup
|
||||
|
||||
# run-higress-e2e-test-wasmplugin starts to run ingress e2e tests.
|
||||
.PHONY: run-higress-e2e-test-wasmplugin
|
||||
run-higress-e2e-test-wasmplugin:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@@ -288,4 +345,24 @@ run-higress-e2e-test-wasmplugin:
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go -isWasmPluginTest=true -wasmPluginType=$(PLUGIN_TYPE) -wasmPluginName=$(PLUGIN_NAME) --ingress-class=higress --debug=true
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go -isWasmPluginTest=true -wasmPluginType=$(PLUGIN_TYPE) -wasmPluginName=$(PLUGIN_NAME) --ingress-class=higress --debug=true --test-area=all --execute-tests=$(TEST_SHORTNAME)
|
||||
|
||||
# run-higress-e2e-test-wasmplugin-run starts to run ingress e2e conformance tests.
|
||||
.PHONY: run-higress-e2e-test-wasmplugin-run
|
||||
run-higress-e2e-test-wasmplugin-run:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@echo -e "\n\033[36mWaiting higress-controller to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go -isWasmPluginTest=true -wasmPluginType=$(PLUGIN_TYPE) -wasmPluginName=$(PLUGIN_NAME) --ingress-class=higress --debug=true --test-area=run --execute-tests=$(TEST_SHORTNAME)
|
||||
|
||||
# run-higress-e2e-test-wasmplugin-clean starts to clean ingress e2e tests.
|
||||
.PHONY: run-higress-e2e-test-wasmplugin-clean
|
||||
run-higress-e2e-test-wasmplugin-clean:
|
||||
@echo -e "\n\033[36mRunning higress conformance tests...\033[0m"
|
||||
@echo -e "\n\033[36mWaiting higress-controller to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-controller --for=condition=Available
|
||||
@echo -e "\n\033[36mWaiting higress-gateway to be ready...\033[0m\n"
|
||||
kubectl wait --timeout=10m -n higress-system deployment/higress-gateway --for=condition=Available
|
||||
go test -v -tags conformance ./test/e2e/e2e_test.go -isWasmPluginTest=true -wasmPluginType=$(PLUGIN_TYPE) -wasmPluginName=$(PLUGIN_NAME) --ingress-class=higress --debug=true --test-area=clean
|
||||
|
||||
16
README.md
16
README.md
@@ -1,10 +1,10 @@
|
||||
<h1 align="center">
|
||||
<img src="https://img.alicdn.com/imgextra/i2/O1CN01NwxLDd20nxfGBjxmZ_!!6000000006895-2-tps-960-290.png" alt="Higress" width="240" height="72.5">
|
||||
<br>
|
||||
Next-generation Cloud Native Gateway
|
||||
Cloud Native API Gateway
|
||||
</h1>
|
||||
|
||||
[](https://github.com/alibaba/higress/actions)
|
||||
[](https://github.com/alibaba/higress/actions)
|
||||
[](https://www.apache.org/licenses/LICENSE-2.0.html)
|
||||
|
||||
[**官网**](https://higress.io/) |
|
||||
@@ -19,7 +19,7 @@
|
||||
</p>
|
||||
|
||||
|
||||
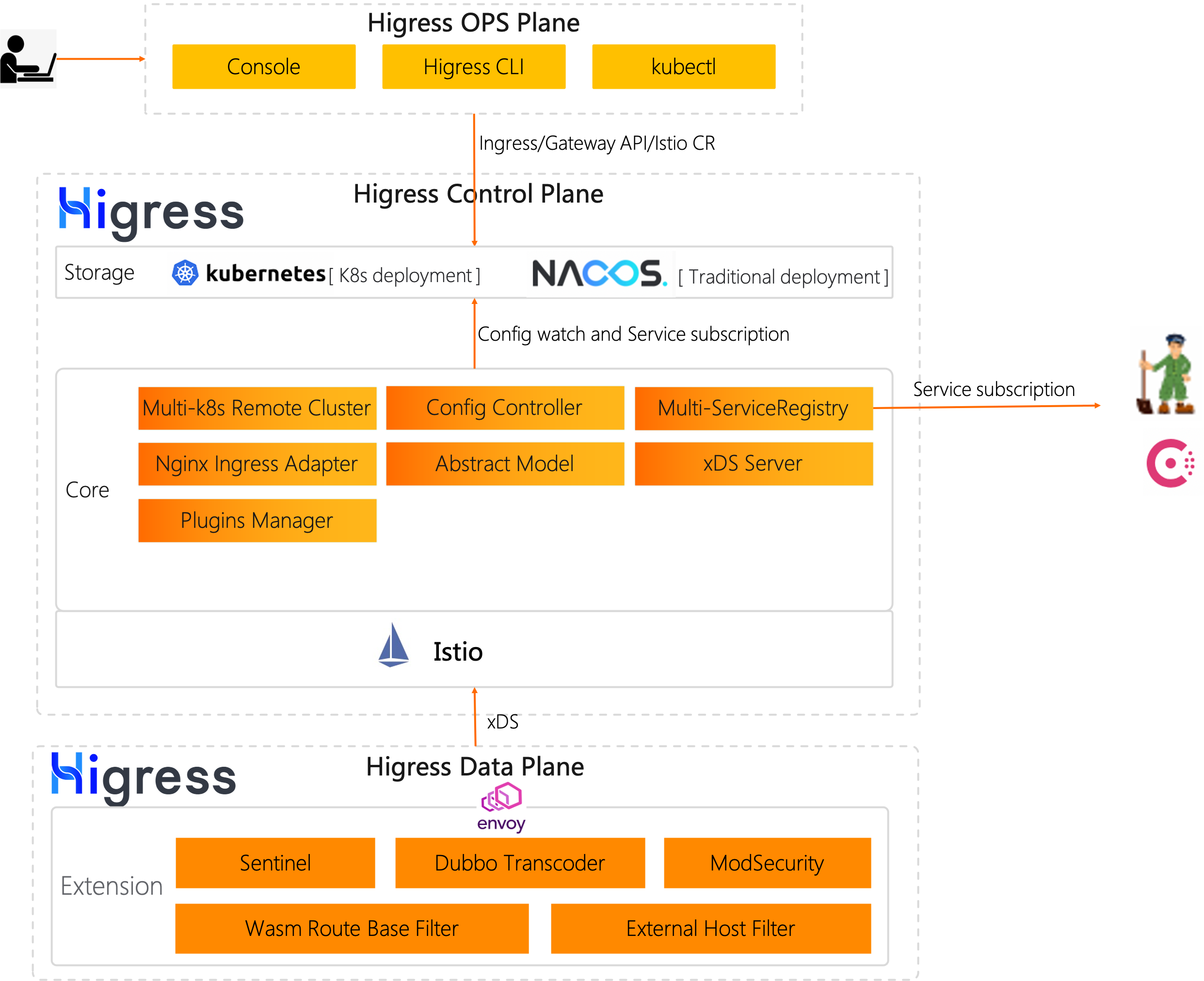
Higress 是基于阿里内部两年多的 Envoy Gateway 实践沉淀,以开源 [Istio](https://github.com/istio/istio) 与 [Envoy](https://github.com/envoyproxy/envoy) 为核心构建的下一代云原生网关。Higress 实现了安全防护网关、流量网关、微服务网关三层网关合一,可以显著降低网关的部署和运维成本。
|
||||
Higress 是基于阿里内部两年多的 Envoy Gateway 实践沉淀,以开源 [Istio](https://github.com/istio/istio) 与 [Envoy](https://github.com/envoyproxy/envoy) 为核心构建的云原生 API 网关。Higress 实现了安全防护网关、流量网关、微服务网关三层网关合一,可以显著降低网关的部署和运维成本。
|
||||
|
||||
|
||||
|
||||
@@ -119,9 +119,13 @@ Higress 是基于阿里内部两年多的 Envoy Gateway 实践沉淀,以开源
|
||||
|
||||
如果没有 Envoy 和 Istio 的开源工作,Higress 就不可能实现,在这里向这两个项目献上最诚挚的敬意。
|
||||
|
||||
### 联系我们
|
||||
|
||||
社区交流群:
|
||||
### 交流群
|
||||
|
||||

|
||||
|
||||
### 技术分享
|
||||
|
||||
微信公众号:
|
||||
|
||||

|
||||
|
||||
|
||||
@@ -1,10 +1,10 @@
|
||||
<h1 align="center">
|
||||
<img src="https://img.alicdn.com/imgextra/i2/O1CN01NwxLDd20nxfGBjxmZ_!!6000000006895-2-tps-960-290.png" alt="Higress" width="240" height="72.5">
|
||||
<br>
|
||||
Next-generation Cloud Native Gateway
|
||||
Cloud Native API Gateway
|
||||
</h1>
|
||||
|
||||
[](https://github.com/alibaba/higress/actions)
|
||||
[](https://github.com/alibaba/higress/actions)
|
||||
[](https://www.apache.org/licenses/LICENSE-2.0.html)
|
||||
|
||||
[**Official Site**](https://higress.io/en-us/) |
|
||||
@@ -18,7 +18,7 @@
|
||||
English | <a href="README.md">中文<a/>
|
||||
</p>
|
||||
|
||||
Higress is a next-generation cloud-native gateway based on Alibaba's internal gateway practices.
|
||||
Higress is a cloud-native api gateway based on Alibaba's internal gateway practices.
|
||||
|
||||
Powered by [Istio](https://github.com/istio/istio) and [Envoy](https://github.com/envoyproxy/envoy), Higress realizes the integration of the triple gateway architecture of traffic gateway, microservice gateway and security gateway, thereby greatly reducing the costs of deployment, operation and maintenance.
|
||||
|
||||
|
||||
@@ -166,7 +166,7 @@ type WasmPlugin struct {
|
||||
// If `priority` is not set, or two `WasmPlugins` exist with the same
|
||||
// value, the ordering will be deterministically derived from name and
|
||||
// namespace of the `WasmPlugins`. Defaults to `0`.
|
||||
Priority *types.Int64Value `protobuf:"bytes,10,opt,name=priority,proto3" json:"priority,omitempty"`
|
||||
Priority *types.Int32Value `protobuf:"bytes,10,opt,name=priority,proto3" json:"priority,omitempty"`
|
||||
// Extended by Higress, the default configuration takes effect globally
|
||||
DefaultConfig *types.Struct `protobuf:"bytes,101,opt,name=default_config,json=defaultConfig,proto3" json:"default_config,omitempty"`
|
||||
// Extended by Higress, matching rules take effect
|
||||
@@ -267,7 +267,7 @@ func (m *WasmPlugin) GetPhase() PluginPhase {
|
||||
return PluginPhase_UNSPECIFIED_PHASE
|
||||
}
|
||||
|
||||
func (m *WasmPlugin) GetPriority() *types.Int64Value {
|
||||
func (m *WasmPlugin) GetPriority() *types.Int32Value {
|
||||
if m != nil {
|
||||
return m.Priority
|
||||
}
|
||||
@@ -377,46 +377,46 @@ func init() {
|
||||
func init() { proto.RegisterFile("extensions/v1alpha1/wasm.proto", fileDescriptor_4d60b240916c4e18) }
|
||||
|
||||
var fileDescriptor_4d60b240916c4e18 = []byte{
|
||||
// 617 bytes of a gzipped FileDescriptorProto
|
||||
0x1f, 0x8b, 0x08, 0x00, 0x00, 0x00, 0x00, 0x00, 0x02, 0xff, 0x7c, 0x94, 0xdf, 0x4e, 0x13, 0x41,
|
||||
0x14, 0xc6, 0xd9, 0x16, 0x0a, 0x3d, 0x05, 0x5c, 0x26, 0x8a, 0x13, 0x30, 0xb5, 0x21, 0x51, 0x57,
|
||||
0x2e, 0x76, 0x43, 0x45, 0xbc, 0x31, 0xc4, 0x02, 0x55, 0x1a, 0xb5, 0x6e, 0x76, 0x41, 0x23, 0x37,
|
||||
0x9b, 0xe9, 0x32, 0xdd, 0x4e, 0x9c, 0xfd, 0x93, 0x9d, 0x59, 0xb0, 0x0f, 0xe2, 0x3b, 0x79, 0xe9,
|
||||
0x23, 0x18, 0xde, 0xc2, 0x3b, 0xd3, 0xd9, 0x2d, 0x6d, 0xd1, 0xf4, 0x6e, 0xe6, 0x9c, 0xdf, 0x39,
|
||||
0xe7, 0xfb, 0xce, 0x4e, 0x16, 0xea, 0xf4, 0xbb, 0xa4, 0x91, 0x60, 0x71, 0x24, 0xac, 0xab, 0x3d,
|
||||
0xc2, 0x93, 0x01, 0xd9, 0xb3, 0xae, 0x89, 0x08, 0xcd, 0x24, 0x8d, 0x65, 0x8c, 0xb6, 0x07, 0x2c,
|
||||
0x48, 0xa9, 0x10, 0xe6, 0x84, 0x33, 0xc7, 0xdc, 0x56, 0x3d, 0x88, 0xe3, 0x80, 0x53, 0x4b, 0xa1,
|
||||
0xbd, 0xac, 0x6f, 0x5d, 0xa7, 0x24, 0x49, 0x68, 0x2a, 0xf2, 0xe2, 0xad, 0x47, 0x77, 0xf3, 0x42,
|
||||
0xa6, 0x99, 0x2f, 0xf3, 0xec, 0xce, 0x9f, 0x45, 0x80, 0x2f, 0x44, 0x84, 0x36, 0xcf, 0x02, 0x16,
|
||||
0x21, 0x1d, 0xca, 0x59, 0xca, 0x71, 0xa9, 0xa1, 0x19, 0x55, 0x67, 0x74, 0x44, 0x9b, 0x50, 0x11,
|
||||
0x03, 0xd2, 0x7c, 0x79, 0x80, 0xcb, 0x2a, 0x58, 0xdc, 0x90, 0x0b, 0x1b, 0x2c, 0x24, 0x01, 0xf5,
|
||||
0x92, 0x8c, 0x73, 0x2f, 0x89, 0x39, 0xf3, 0x87, 0x78, 0xb1, 0xa1, 0x19, 0xeb, 0xcd, 0x67, 0xe6,
|
||||
0x1c, 0xbd, 0xa6, 0x9d, 0x71, 0x6e, 0x2b, 0xdc, 0xb9, 0xa7, 0x3a, 0x4c, 0x02, 0x68, 0x77, 0xa6,
|
||||
0xa9, 0xa0, 0x7e, 0x4a, 0x25, 0x5e, 0x52, 0x73, 0x27, 0xac, 0xab, 0xc2, 0xe8, 0x39, 0xe8, 0x57,
|
||||
0x34, 0x65, 0x7d, 0xe6, 0x13, 0xc9, 0xe2, 0xc8, 0xfb, 0x46, 0x87, 0xb8, 0x92, 0xa3, 0xd3, 0xf1,
|
||||
0xf7, 0x74, 0x88, 0x5e, 0xc3, 0x5a, 0xa2, 0xfc, 0x79, 0x7e, 0x1c, 0xf5, 0x59, 0x80, 0x97, 0x1b,
|
||||
0x9a, 0x51, 0x6b, 0x3e, 0x34, 0xf3, 0xd5, 0x98, 0xe3, 0xd5, 0x98, 0xae, 0x5a, 0x8d, 0xb3, 0x9a,
|
||||
0xd3, 0xc7, 0x0a, 0x46, 0x8f, 0xa1, 0x56, 0x54, 0x47, 0x24, 0xa4, 0x78, 0x45, 0xcd, 0x80, 0x3c,
|
||||
0xd4, 0x25, 0x21, 0x45, 0x87, 0xb0, 0x94, 0x0c, 0x88, 0xa0, 0xb8, 0xaa, 0xec, 0x1b, 0xf3, 0xed,
|
||||
0xab, 0x3a, 0x7b, 0xc4, 0x3b, 0x79, 0x19, 0x7a, 0x05, 0x2b, 0x49, 0xca, 0xe2, 0x94, 0xc9, 0x21,
|
||||
0x06, 0xa5, 0x6c, 0xfb, 0x1f, 0x65, 0x9d, 0x48, 0x1e, 0xec, 0x7f, 0x26, 0x3c, 0xa3, 0xce, 0x2d,
|
||||
0x8c, 0x0e, 0x61, 0xfd, 0x92, 0xf6, 0x49, 0xc6, 0xe5, 0xd8, 0x18, 0x9d, 0x6f, 0x6c, 0xad, 0xc0,
|
||||
0x0b, 0x67, 0xef, 0xa0, 0x16, 0x12, 0xe9, 0x0f, 0xbc, 0x34, 0xe3, 0x54, 0xe0, 0x7e, 0xa3, 0x6c,
|
||||
0xd4, 0x9a, 0x4f, 0xe7, 0xca, 0xff, 0x38, 0xe2, 0x9d, 0x8c, 0x53, 0x07, 0xc2, 0xf1, 0x51, 0xa0,
|
||||
0x7d, 0xd8, 0x9c, 0x15, 0xe2, 0x5d, 0x32, 0x41, 0x7a, 0x9c, 0xe2, 0xa0, 0xa1, 0x19, 0x2b, 0xce,
|
||||
0xfd, 0x99, 0xb9, 0x27, 0x79, 0x6e, 0xe7, 0x87, 0x06, 0xd5, 0xdb, 0x7e, 0x08, 0xc3, 0x32, 0x8b,
|
||||
0xd4, 0x60, 0xac, 0x35, 0xca, 0x46, 0xd5, 0x19, 0x5f, 0x47, 0x4f, 0xf0, 0x32, 0x0e, 0x09, 0x8b,
|
||||
0x70, 0x49, 0x25, 0x8a, 0x1b, 0xb2, 0xa0, 0x52, 0xd8, 0x2e, 0xcf, 0xb7, 0x5d, 0x60, 0xe8, 0x09,
|
||||
0xac, 0xdf, 0x91, 0xb7, 0xa8, 0xe4, 0xad, 0xf9, 0xd3, 0xba, 0x76, 0xdb, 0x50, 0x9b, 0xfa, 0x4a,
|
||||
0xe8, 0x01, 0x6c, 0x9c, 0x77, 0x5d, 0xbb, 0x7d, 0xdc, 0x79, 0xdb, 0x69, 0x9f, 0x78, 0xf6, 0x69,
|
||||
0xcb, 0x6d, 0xeb, 0x0b, 0xa8, 0x0a, 0x4b, 0xad, 0xf3, 0xb3, 0xd3, 0xae, 0xae, 0x8d, 0x8f, 0x17,
|
||||
0x7a, 0x69, 0x74, 0x74, 0xcf, 0x5a, 0x67, 0xae, 0x5e, 0xde, 0x3d, 0x02, 0x98, 0x7a, 0xda, 0x9b,
|
||||
0x80, 0x66, 0xba, 0x7c, 0xfa, 0xd0, 0x39, 0xfe, 0xaa, 0x2f, 0x20, 0x1d, 0x56, 0x3b, 0xfd, 0x6e,
|
||||
0x2c, 0xed, 0x94, 0x0a, 0x1a, 0x49, 0x5d, 0x43, 0x00, 0x95, 0x16, 0xbf, 0x26, 0x43, 0xa1, 0x97,
|
||||
0x8e, 0xde, 0xfc, 0xbc, 0xa9, 0x6b, 0xbf, 0x6e, 0xea, 0xda, 0xef, 0x9b, 0xba, 0x76, 0xd1, 0x0c,
|
||||
0x98, 0x1c, 0x64, 0x3d, 0xd3, 0x8f, 0x43, 0x8b, 0x70, 0xd6, 0x23, 0x3d, 0x62, 0x15, 0x1f, 0xcb,
|
||||
0x22, 0x09, 0xb3, 0xfe, 0xf3, 0x1b, 0xe9, 0x55, 0xd4, 0x32, 0x5e, 0xfc, 0x0d, 0x00, 0x00, 0xff,
|
||||
0xff, 0x48, 0x74, 0xbe, 0xc1, 0x64, 0x04, 0x00, 0x00,
|
||||
// 619 bytes of a gzipped FileDescriptorProto
|
||||
0x1f, 0x8b, 0x08, 0x00, 0x00, 0x00, 0x00, 0x00, 0x02, 0xff, 0x7c, 0x94, 0xdd, 0x4e, 0xdb, 0x4c,
|
||||
0x10, 0x86, 0x71, 0x02, 0x81, 0x4c, 0x80, 0xcf, 0xac, 0xbe, 0xd2, 0x15, 0x54, 0x69, 0x84, 0xd4,
|
||||
0xd6, 0xe5, 0xc0, 0x16, 0xa1, 0x3f, 0x27, 0x15, 0x6a, 0x80, 0xb4, 0x44, 0x6d, 0x53, 0xcb, 0x86,
|
||||
0x56, 0xe5, 0xc4, 0xda, 0x98, 0x8d, 0xb3, 0xea, 0xfa, 0x47, 0xde, 0x35, 0x34, 0x17, 0xd2, 0x7b,
|
||||
0xea, 0x61, 0x2f, 0xa1, 0xe2, 0x2e, 0x7a, 0x56, 0x65, 0x6d, 0x43, 0x42, 0xab, 0x9c, 0xed, 0xce,
|
||||
0x3c, 0x33, 0xf3, 0xbe, 0xe3, 0x95, 0xa1, 0x49, 0xbf, 0x49, 0x1a, 0x09, 0x16, 0x47, 0xc2, 0xba,
|
||||
0xdc, 0x23, 0x3c, 0x19, 0x91, 0x3d, 0xeb, 0x8a, 0x88, 0xd0, 0x4c, 0xd2, 0x58, 0xc6, 0x68, 0x7b,
|
||||
0xc4, 0x82, 0x94, 0x0a, 0x61, 0xde, 0x72, 0x66, 0xc9, 0x6d, 0x35, 0x83, 0x38, 0x0e, 0x38, 0xb5,
|
||||
0x14, 0x3a, 0xc8, 0x86, 0xd6, 0x55, 0x4a, 0x92, 0x84, 0xa6, 0x22, 0x2f, 0xde, 0x7a, 0x70, 0x37,
|
||||
0x2f, 0x64, 0x9a, 0xf9, 0x32, 0xcf, 0xee, 0xfc, 0x5e, 0x04, 0xf8, 0x4c, 0x44, 0x68, 0xf3, 0x2c,
|
||||
0x60, 0x11, 0xd2, 0xa1, 0x9a, 0xa5, 0x1c, 0x57, 0x5a, 0x9a, 0x51, 0x77, 0x26, 0x47, 0xb4, 0x09,
|
||||
0x35, 0x31, 0x22, 0xed, 0xe7, 0x2f, 0x70, 0x55, 0x05, 0x8b, 0x1b, 0x72, 0x61, 0x83, 0x85, 0x24,
|
||||
0xa0, 0x5e, 0x92, 0x71, 0xee, 0x25, 0x31, 0x67, 0xfe, 0x18, 0x2f, 0xb6, 0x34, 0x63, 0xbd, 0xfd,
|
||||
0xc4, 0x9c, 0xa3, 0xd7, 0xb4, 0x33, 0xce, 0x6d, 0x85, 0x3b, 0xff, 0xa9, 0x0e, 0xb7, 0x01, 0xb4,
|
||||
0x3b, 0xd3, 0x54, 0x50, 0x3f, 0xa5, 0x12, 0x2f, 0xa9, 0xb9, 0xb7, 0xac, 0xab, 0xc2, 0xe8, 0x29,
|
||||
0xe8, 0x97, 0x34, 0x65, 0x43, 0xe6, 0x13, 0xc9, 0xe2, 0xc8, 0xfb, 0x4a, 0xc7, 0xb8, 0x96, 0xa3,
|
||||
0xd3, 0xf1, 0x77, 0x74, 0x8c, 0x5e, 0xc1, 0x5a, 0xa2, 0xfc, 0x79, 0x7e, 0x1c, 0x0d, 0x59, 0x80,
|
||||
0x97, 0x5b, 0x9a, 0xd1, 0x68, 0xdf, 0x37, 0xf3, 0xd5, 0x98, 0xe5, 0x6a, 0x4c, 0x57, 0xad, 0xc6,
|
||||
0x59, 0xcd, 0xe9, 0x23, 0x05, 0xa3, 0x87, 0xd0, 0x28, 0xaa, 0x23, 0x12, 0x52, 0xbc, 0xa2, 0x66,
|
||||
0x40, 0x1e, 0xea, 0x93, 0x90, 0xa2, 0x03, 0x58, 0x4a, 0x46, 0x44, 0x50, 0x5c, 0x57, 0xf6, 0x8d,
|
||||
0xf9, 0xf6, 0x55, 0x9d, 0x3d, 0xe1, 0x9d, 0xbc, 0x0c, 0xbd, 0x84, 0x95, 0x24, 0x65, 0x71, 0xca,
|
||||
0xe4, 0x18, 0x83, 0x52, 0xb6, 0xfd, 0x97, 0xb2, 0x5e, 0x24, 0xf7, 0xdb, 0x9f, 0x08, 0xcf, 0xa8,
|
||||
0x73, 0x03, 0xa3, 0x03, 0x58, 0xbf, 0xa0, 0x43, 0x92, 0x71, 0x59, 0x1a, 0xa3, 0xf3, 0x8d, 0xad,
|
||||
0x15, 0x78, 0xe1, 0xec, 0x2d, 0x34, 0x42, 0x22, 0xfd, 0x91, 0x97, 0x66, 0x9c, 0x0a, 0x3c, 0x6c,
|
||||
0x55, 0x8d, 0x46, 0xfb, 0xf1, 0x5c, 0xf9, 0x1f, 0x26, 0xbc, 0x93, 0x71, 0xea, 0x40, 0x58, 0x1e,
|
||||
0x05, 0x7a, 0x06, 0x9b, 0xb3, 0x42, 0xbc, 0x0b, 0x26, 0xc8, 0x80, 0x53, 0x1c, 0xb4, 0x34, 0x63,
|
||||
0xc5, 0xf9, 0x7f, 0x66, 0xee, 0x71, 0x9e, 0xdb, 0xf9, 0xae, 0x41, 0xfd, 0xa6, 0x1f, 0xc2, 0xb0,
|
||||
0xcc, 0x22, 0x35, 0x18, 0x6b, 0xad, 0xaa, 0x51, 0x77, 0xca, 0xeb, 0xe4, 0x09, 0x5e, 0xc4, 0x21,
|
||||
0x61, 0x11, 0xae, 0xa8, 0x44, 0x71, 0x43, 0x16, 0xd4, 0x0a, 0xdb, 0xd5, 0xf9, 0xb6, 0x0b, 0x0c,
|
||||
0x3d, 0x82, 0xf5, 0x3b, 0xf2, 0x16, 0x95, 0xbc, 0x35, 0x7f, 0x5a, 0xd7, 0x6e, 0x17, 0x1a, 0x53,
|
||||
0x5f, 0x09, 0xdd, 0x83, 0x8d, 0xb3, 0xbe, 0x6b, 0x77, 0x8f, 0x7a, 0x6f, 0x7a, 0xdd, 0x63, 0xcf,
|
||||
0x3e, 0xe9, 0xb8, 0x5d, 0x7d, 0x01, 0xd5, 0x61, 0xa9, 0x73, 0x76, 0x7a, 0xd2, 0xd7, 0xb5, 0xf2,
|
||||
0x78, 0xae, 0x57, 0x26, 0x47, 0xf7, 0xb4, 0x73, 0xea, 0xea, 0xd5, 0xdd, 0x43, 0x80, 0xa9, 0xa7,
|
||||
0xbd, 0x09, 0x68, 0xa6, 0xcb, 0xc7, 0xf7, 0xbd, 0xa3, 0x2f, 0xfa, 0x02, 0xd2, 0x61, 0xb5, 0x37,
|
||||
0xec, 0xc7, 0xd2, 0x4e, 0xa9, 0xa0, 0x91, 0xd4, 0x35, 0x04, 0x50, 0xeb, 0xf0, 0x2b, 0x32, 0x16,
|
||||
0x7a, 0xe5, 0xf0, 0xf5, 0x8f, 0xeb, 0xa6, 0xf6, 0xf3, 0xba, 0xa9, 0xfd, 0xba, 0x6e, 0x6a, 0xe7,
|
||||
0xed, 0x80, 0xc9, 0x51, 0x36, 0x30, 0xfd, 0x38, 0xb4, 0x08, 0x67, 0x03, 0x32, 0x20, 0x56, 0xf1,
|
||||
0xb1, 0x2c, 0x92, 0x30, 0xeb, 0x1f, 0xbf, 0x91, 0x41, 0x4d, 0x2d, 0x63, 0xff, 0x4f, 0x00, 0x00,
|
||||
0x00, 0xff, 0xff, 0xb9, 0xf2, 0x67, 0xbe, 0x64, 0x04, 0x00, 0x00,
|
||||
}
|
||||
|
||||
func (m *WasmPlugin) Marshal() (dAtA []byte, err error) {
|
||||
@@ -1024,7 +1024,7 @@ func (m *WasmPlugin) Unmarshal(dAtA []byte) error {
|
||||
return io.ErrUnexpectedEOF
|
||||
}
|
||||
if m.Priority == nil {
|
||||
m.Priority = &types.Int64Value{}
|
||||
m.Priority = &types.Int32Value{}
|
||||
}
|
||||
if err := m.Priority.Unmarshal(dAtA[iNdEx:postIndex]); err != nil {
|
||||
return err
|
||||
|
||||
@@ -98,7 +98,7 @@ message WasmPlugin {
|
||||
// If `priority` is not set, or two `WasmPlugins` exist with the same
|
||||
// value, the ordering will be deterministically derived from name and
|
||||
// namespace of the `WasmPlugins`. Defaults to `0`.
|
||||
google.protobuf.Int64Value priority = 10;
|
||||
google.protobuf.Int32Value priority = 10;
|
||||
|
||||
// Extended by Higress, the default configuration takes effect globally
|
||||
google.protobuf.Struct default_config = 101;
|
||||
|
||||
@@ -18,10 +18,13 @@ import (
|
||||
"fmt"
|
||||
"os"
|
||||
|
||||
"istio.io/pkg/log"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cmd"
|
||||
)
|
||||
|
||||
func main() {
|
||||
log.EnableKlogWithCobra()
|
||||
if err := cmd.GetRootCommand().Execute(); err != nil {
|
||||
_, _ = fmt.Fprintln(os.Stderr, err)
|
||||
os.Exit(1)
|
||||
|
||||
@@ -2,7 +2,11 @@ codecov:
|
||||
require_ci_to_pass: yes
|
||||
coverage:
|
||||
status:
|
||||
patch: no
|
||||
patch:
|
||||
default:
|
||||
target: 50%
|
||||
threshold: 0%
|
||||
if_ci_failed: error # success, failure, error, ignore
|
||||
project:
|
||||
default:
|
||||
target: auto
|
||||
@@ -17,4 +21,4 @@ ignore:
|
||||
comment:
|
||||
layout: "reach,diff,flags,tree"
|
||||
behavior: default
|
||||
require_changes: no
|
||||
require_changes: no
|
||||
49
envoy/1.20/patches/envoy/20240110-fix-srds.patch
Normal file
49
envoy/1.20/patches/envoy/20240110-fix-srds.patch
Normal file
@@ -0,0 +1,49 @@
|
||||
diff -Naur envoy/source/common/router/BUILD envoy-new/source/common/router/BUILD
|
||||
--- envoy/source/common/router/BUILD 2024-01-10 20:10:14.505600746 +0800
|
||||
+++ envoy-new/source/common/router/BUILD 2024-01-10 20:07:25.960379955 +0800
|
||||
@@ -212,6 +212,7 @@
|
||||
"//envoy/router:rds_interface",
|
||||
"//envoy/router:scopes_interface",
|
||||
"//envoy/thread_local:thread_local_interface",
|
||||
+ "//source/common/http:header_utility_lib",
|
||||
"@envoy_api//envoy/config/route/v3:pkg_cc_proto",
|
||||
"@envoy_api//envoy/extensions/filters/network/http_connection_manager/v3:pkg_cc_proto",
|
||||
],
|
||||
diff -Naur envoy/source/common/router/scoped_config_impl.cc envoy-new/source/common/router/scoped_config_impl.cc
|
||||
--- envoy/source/common/router/scoped_config_impl.cc 2024-01-10 20:10:14.529600924 +0800
|
||||
+++ envoy-new/source/common/router/scoped_config_impl.cc 2024-01-10 20:09:50.161422411 +0800
|
||||
@@ -3,6 +3,8 @@
|
||||
#include "envoy/config/route/v3/scoped_route.pb.h"
|
||||
#include "envoy/extensions/filters/network/http_connection_manager/v3/http_connection_manager.pb.h"
|
||||
|
||||
+#include "source/common/http/header_utility.h"
|
||||
+
|
||||
namespace Envoy {
|
||||
namespace Router {
|
||||
|
||||
@@ -74,18 +76,20 @@
|
||||
HostValueExtractorImpl::computeFragment(const Http::HeaderMap& headers,
|
||||
const StreamInfo::StreamInfo&,
|
||||
ReComputeCbPtr& recompute) const {
|
||||
- auto fragment = computeFragment(headers);
|
||||
auto host = static_cast<const Http::RequestHeaderMap&>(headers).getHostValue();
|
||||
+ auto port_start = Http::HeaderUtility::getPortStart(host);
|
||||
+ if (port_start != absl::string_view::npos) {
|
||||
+ host = host.substr(0, port_start);
|
||||
+ }
|
||||
*recompute = [this, host, recompute]() mutable -> std::unique_ptr<ScopeKeyFragmentBase> {
|
||||
return reComputeHelper(std::string(host), recompute, 0);
|
||||
};
|
||||
- return fragment;
|
||||
+ return std::make_unique<StringKeyFragment>(host);
|
||||
}
|
||||
|
||||
std::unique_ptr<ScopeKeyFragmentBase>
|
||||
-HostValueExtractorImpl::computeFragment(const Http::HeaderMap& headers) const {
|
||||
- return std::make_unique<StringKeyFragment>(
|
||||
- static_cast<const Http::RequestHeaderMap&>(headers).getHostValue());
|
||||
+HostValueExtractorImpl::computeFragment(const Http::HeaderMap&) const {
|
||||
+ return nullptr;
|
||||
}
|
||||
|
||||
std::unique_ptr<ScopeKeyFragmentBase>
|
||||
65
envoy/1.20/patches/envoy/20240111-fix-srds-compute.patch
Normal file
65
envoy/1.20/patches/envoy/20240111-fix-srds-compute.patch
Normal file
@@ -0,0 +1,65 @@
|
||||
diff -Naur envoy/source/common/router/scoped_config_impl.cc envoy-new/source/common/router/scoped_config_impl.cc
|
||||
--- envoy/source/common/router/scoped_config_impl.cc 2024-01-11 16:23:55.407881263 +0800
|
||||
+++ envoy-new/source/common/router/scoped_config_impl.cc 2024-01-11 16:23:42.311786814 +0800
|
||||
@@ -53,21 +53,26 @@
|
||||
}
|
||||
|
||||
std::unique_ptr<ScopeKeyFragmentBase>
|
||||
-HostValueExtractorImpl::reComputeHelper(const std::string& host, ReComputeCbPtr& next_recompute,
|
||||
+HostValueExtractorImpl::reComputeHelper(const std::string& host,
|
||||
+ ReComputeCbWeakPtr& weak_next_recompute,
|
||||
uint32_t recompute_seq) const {
|
||||
if (recompute_seq == max_recompute_num_) {
|
||||
ENVOY_LOG_MISC(warn,
|
||||
"recompute host fragment failed, maximum number of recalculations exceeded");
|
||||
return nullptr;
|
||||
}
|
||||
+ auto next_recompute = weak_next_recompute.lock();
|
||||
+ if (!next_recompute) {
|
||||
+ return nullptr;
|
||||
+ }
|
||||
if (host == "*") {
|
||||
*next_recompute = nullptr;
|
||||
return nullptr;
|
||||
}
|
||||
auto masked_host = maskFirstDNSLabel(host);
|
||||
*next_recompute = [this, masked_host, recompute_seq,
|
||||
- next_recompute]() mutable -> std::unique_ptr<ScopeKeyFragmentBase> {
|
||||
- return reComputeHelper(masked_host, next_recompute, recompute_seq + 1);
|
||||
+ weak_next_recompute]() mutable -> std::unique_ptr<ScopeKeyFragmentBase> {
|
||||
+ return reComputeHelper(masked_host, weak_next_recompute, recompute_seq + 1);
|
||||
};
|
||||
return std::make_unique<StringKeyFragment>(masked_host);
|
||||
}
|
||||
@@ -81,8 +86,9 @@
|
||||
if (port_start != absl::string_view::npos) {
|
||||
host = host.substr(0, port_start);
|
||||
}
|
||||
- *recompute = [this, host, recompute]() mutable -> std::unique_ptr<ScopeKeyFragmentBase> {
|
||||
- return reComputeHelper(std::string(host), recompute, 0);
|
||||
+ *recompute = [this, host, weak_recompute = ReComputeCbWeakPtr(recompute)]() mutable
|
||||
+ -> std::unique_ptr<ScopeKeyFragmentBase> {
|
||||
+ return reComputeHelper(std::string(host), weak_recompute, 0);
|
||||
};
|
||||
return std::make_unique<StringKeyFragment>(host);
|
||||
}
|
||||
diff -Naur envoy/source/common/router/scoped_config_impl.h envoy-new/source/common/router/scoped_config_impl.h
|
||||
--- envoy/source/common/router/scoped_config_impl.h 2024-01-11 16:23:55.407881263 +0800
|
||||
+++ envoy-new/source/common/router/scoped_config_impl.h 2024-01-11 16:23:42.311786814 +0800
|
||||
@@ -25,6 +25,7 @@
|
||||
#if defined(ALIMESH)
|
||||
using ReComputeCb = std::function<std::unique_ptr<ScopeKeyFragmentBase>()>;
|
||||
using ReComputeCbPtr = std::shared_ptr<ReComputeCb>;
|
||||
+using ReComputeCbWeakPtr = std::weak_ptr<ReComputeCb>;
|
||||
#endif
|
||||
|
||||
/**
|
||||
@@ -83,7 +84,7 @@
|
||||
|
||||
private:
|
||||
std::unique_ptr<ScopeKeyFragmentBase> reComputeHelper(const std::string& host,
|
||||
- ReComputeCbPtr& next_recompute,
|
||||
+ ReComputeCbWeakPtr& weak_next_recompute,
|
||||
uint32_t recompute_seq) const;
|
||||
|
||||
static constexpr uint32_t DefaultMaxRecomputeNum = 100;
|
||||
1445
envoy/1.20/patches/envoy/20240116-fix-cve.patch
Normal file
1445
envoy/1.20/patches/envoy/20240116-fix-cve.patch
Normal file
File diff suppressed because it is too large
Load Diff
File diff suppressed because it is too large
Load Diff
5505
envoy/1.20/patches/envoy/20240519-wasm-upgrade.patch
Normal file
5505
envoy/1.20/patches/envoy/20240519-wasm-upgrade.patch
Normal file
File diff suppressed because it is too large
Load Diff
14
envoy/1.20/patches/envoy/20240521-fix-wasm-host.patch
Normal file
14
envoy/1.20/patches/envoy/20240521-fix-wasm-host.patch
Normal file
@@ -0,0 +1,14 @@
|
||||
diff -Naur envoy/bazel/repository_locations.bzl envoy-new/bazel/repository_locations.bzl
|
||||
--- envoy/bazel/repository_locations.bzl 2024-05-21 22:49:46.686598518 +0800
|
||||
+++ envoy-new/bazel/repository_locations.bzl 2024-05-21 22:49:02.554597652 +0800
|
||||
@@ -1031,8 +1031,8 @@
|
||||
project_name = "WebAssembly for Proxies (C++ host implementation)",
|
||||
project_desc = "WebAssembly for Proxies (C++ host implementation)",
|
||||
project_url = "https://github.com/higress-group/proxy-wasm-cpp-host",
|
||||
- version = "f8b624dc6c37d4e0a3c1b332652746793e2031ad",
|
||||
- sha256 = "ba20328101c91d0ae6383947ced99620cd9b4ea22ab2fda6b26f343b38c3be83",
|
||||
+ version = "cad2eb04d402dbf559101f3cb4f44da0d9c5b0b0",
|
||||
+ sha256 = "4efbcc97c58994fab92c9dc50c051ad16463647d4c0c6df36a7204d2984c1e63",
|
||||
strip_prefix = "proxy-wasm-cpp-host-{version}",
|
||||
urls = ["https://github.com/higress-group/proxy-wasm-cpp-host/archive/{version}.tar.gz"],
|
||||
use_category = ["dataplane_ext"],
|
||||
25
envoy/1.20/patches/envoy/20240527-fix-wasm-recover.patch
Normal file
25
envoy/1.20/patches/envoy/20240527-fix-wasm-recover.patch
Normal file
@@ -0,0 +1,25 @@
|
||||
diff -Naur envoy/bazel/repository_locations.bzl envoy-new/bazel/repository_locations.bzl
|
||||
--- envoy/bazel/repository_locations.bzl 2024-05-27 18:04:13.116443196 +0800
|
||||
+++ envoy-new/bazel/repository_locations.bzl 2024-05-27 18:02:24.812441069 +0800
|
||||
@@ -1031,8 +1031,8 @@
|
||||
project_name = "WebAssembly for Proxies (C++ host implementation)",
|
||||
project_desc = "WebAssembly for Proxies (C++ host implementation)",
|
||||
project_url = "https://github.com/higress-group/proxy-wasm-cpp-host",
|
||||
- version = "cad2eb04d402dbf559101f3cb4f44da0d9c5b0b0",
|
||||
- sha256 = "4efbcc97c58994fab92c9dc50c051ad16463647d4c0c6df36a7204d2984c1e63",
|
||||
+ version = "28a33a5a3e6c1ff8f53128a74e89aeca47850f68",
|
||||
+ sha256 = "1aaa5898c169aeff115eff2fedf58095b3509d2e59861ad498e661a990d78b3d",
|
||||
strip_prefix = "proxy-wasm-cpp-host-{version}",
|
||||
urls = ["https://github.com/higress-group/proxy-wasm-cpp-host/archive/{version}.tar.gz"],
|
||||
use_category = ["dataplane_ext"],
|
||||
diff -Naur envoy/source/extensions/filters/http/wasm/wasm_filter.h envoy-new/source/extensions/filters/http/wasm/wasm_filter.h
|
||||
--- envoy/source/extensions/filters/http/wasm/wasm_filter.h 2024-05-27 18:04:13.112443196 +0800
|
||||
+++ envoy-new/source/extensions/filters/http/wasm/wasm_filter.h 2024-05-27 18:03:25.360442258 +0800
|
||||
@@ -51,6 +51,7 @@
|
||||
if (opt_ref->recover()) {
|
||||
ENVOY_LOG(info, "wasm vm recover success");
|
||||
wasm = opt_ref->handle()->wasmHandle()->wasm().get();
|
||||
+ handle = opt_ref->handle();
|
||||
} else {
|
||||
ENVOY_LOG(info, "wasm vm recover failed");
|
||||
failed = true;
|
||||
File diff suppressed because it is too large
Load Diff
33
go.mod
33
go.mod
@@ -15,7 +15,7 @@ replace github.com/imdario/mergo => github.com/imdario/mergo v0.3.5
|
||||
|
||||
require (
|
||||
github.com/AlecAivazis/survey/v2 v2.3.6
|
||||
github.com/agiledragon/gomonkey/v2 v2.9.0
|
||||
github.com/agiledragon/gomonkey/v2 v2.11.0
|
||||
github.com/avast/retry-go/v4 v4.3.4
|
||||
github.com/compose-spec/compose-go v1.8.2
|
||||
github.com/docker/cli v20.10.20+incompatible
|
||||
@@ -44,13 +44,13 @@ require (
|
||||
github.com/spf13/pflag v1.0.5
|
||||
github.com/spf13/viper v1.8.1
|
||||
github.com/stretchr/testify v1.8.3
|
||||
go.uber.org/atomic v1.9.0
|
||||
go.uber.org/atomic v1.11.0
|
||||
google.golang.org/grpc v1.48.0
|
||||
google.golang.org/protobuf v1.28.1
|
||||
gopkg.in/yaml.v2 v2.4.0
|
||||
gopkg.in/yaml.v3 v3.0.1
|
||||
istio.io/api v0.0.0-20211122181927-8da52c66ff23
|
||||
istio.io/client-go v1.12.0-rc.1.0.20211118171212-b744b6f111e4
|
||||
istio.io/client-go v1.12.0-rc.1.0.20211118171212-b744b6f111e4 // indirect
|
||||
istio.io/gogo-genproto v0.0.0-20211115195057-0e34bdd2be67
|
||||
istio.io/istio v0.0.0
|
||||
istio.io/pkg v0.0.0-20211115195056-e379f31ee62a
|
||||
@@ -172,6 +172,7 @@ require (
|
||||
github.com/json-iterator/go v1.1.12 // indirect
|
||||
github.com/kballard/go-shellquote v0.0.0-20180428030007-95032a82bc51 // indirect
|
||||
github.com/klauspost/compress v1.15.9 // indirect
|
||||
github.com/klauspost/cpuid/v2 v2.2.5 // indirect
|
||||
github.com/kr/pretty v0.3.0 // indirect
|
||||
github.com/kr/text v0.2.0 // indirect
|
||||
github.com/lann/builder v0.0.0-20180802200727-47ae307949d0 // indirect
|
||||
@@ -185,6 +186,7 @@ require (
|
||||
github.com/lestrrat/go-file-rotatelogs v0.0.0-20180223000712-d3151e2a480f // indirect
|
||||
github.com/lestrrat/go-strftime v0.0.0-20180220042222-ba3bf9c1d042 // indirect
|
||||
github.com/lib/pq v1.10.0 // indirect
|
||||
github.com/libdns/libdns v0.2.1 // indirect
|
||||
github.com/liggitt/tabwriter v0.0.0-20181228230101-89fcab3d43de // indirect
|
||||
github.com/magiconair/properties v1.8.5 // indirect
|
||||
github.com/mailru/easyjson v0.7.7 // indirect
|
||||
@@ -194,7 +196,7 @@ require (
|
||||
github.com/mattn/go-shellwords v1.0.12 // indirect
|
||||
github.com/matttproud/golang_protobuf_extensions v1.0.4 // indirect
|
||||
github.com/mgutz/ansi v0.0.0-20170206155736-9520e82c474b // indirect
|
||||
github.com/miekg/dns v1.1.43 // indirect
|
||||
github.com/miekg/dns v1.1.55 // indirect
|
||||
github.com/miekg/pkcs11 v1.1.1 // indirect
|
||||
github.com/mitchellh/copystructure v1.2.0 // indirect
|
||||
github.com/mitchellh/go-wordwrap v1.0.0 // indirect
|
||||
@@ -248,20 +250,22 @@ require (
|
||||
github.com/xeipuuv/gojsonschema v1.2.0 // indirect
|
||||
github.com/xlab/treeprint v0.0.0-20181112141820-a009c3971eca // indirect
|
||||
github.com/yl2chen/cidranger v1.0.2 // indirect
|
||||
github.com/zeebo/blake3 v0.2.3 // indirect
|
||||
go.opencensus.io v0.23.0 // indirect
|
||||
go.opentelemetry.io/proto/otlp v0.12.0 // indirect
|
||||
go.starlark.net v0.0.0-20200306205701-8dd3e2ee1dd5 // indirect
|
||||
go.uber.org/multierr v1.7.0 // indirect
|
||||
go.uber.org/zap v1.21.0 // indirect
|
||||
golang.org/x/crypto v0.11.0 // indirect
|
||||
go.uber.org/multierr v1.11.0 // indirect
|
||||
go.uber.org/zap v1.24.0 // indirect
|
||||
golang.org/x/crypto v0.17.0 // indirect
|
||||
golang.org/x/exp v0.0.0-20230321023759-10a507213a29 // indirect
|
||||
golang.org/x/net v0.12.0 // indirect
|
||||
golang.org/x/mod v0.11.0 // indirect
|
||||
golang.org/x/oauth2 v0.6.0 // indirect
|
||||
golang.org/x/sync v0.2.0 // indirect
|
||||
golang.org/x/sys v0.10.0 // indirect
|
||||
golang.org/x/term v0.10.0 // indirect
|
||||
golang.org/x/text v0.11.0 // indirect
|
||||
golang.org/x/sync v0.3.0 // indirect
|
||||
golang.org/x/sys v0.15.0 // indirect
|
||||
golang.org/x/term v0.15.0 // indirect
|
||||
golang.org/x/text v0.14.0 // indirect
|
||||
golang.org/x/time v0.0.0-20220722155302-e5dcc9cfc0b9 // indirect
|
||||
golang.org/x/tools v0.10.0 // indirect
|
||||
gomodules.xyz/jsonpatch/v2 v2.2.0 // indirect
|
||||
gomodules.xyz/jsonpatch/v3 v3.0.1 // indirect
|
||||
gomodules.xyz/orderedmap v0.1.0 // indirect
|
||||
@@ -300,11 +304,16 @@ replace istio.io/client-go => ./external/client-go
|
||||
|
||||
replace istio.io/istio => ./external/istio
|
||||
|
||||
replace github.com/caddyserver/certmagic => github.com/2456868764/certmagic v1.0.1
|
||||
|
||||
require (
|
||||
github.com/caddyserver/certmagic v0.20.0
|
||||
github.com/evanphx/json-patch/v5 v5.6.0
|
||||
github.com/google/yamlfmt v0.10.0
|
||||
github.com/kylelemons/godebug v1.1.0
|
||||
github.com/mholt/acmez v1.2.0
|
||||
github.com/tidwall/gjson v1.17.0
|
||||
golang.org/x/net v0.17.0
|
||||
helm.sh/helm/v3 v3.7.1
|
||||
k8s.io/apiextensions-apiserver v0.25.4
|
||||
knative.dev/networking v0.0.0-20220302134042-e8b2eb995165
|
||||
|
||||
62
go.sum
62
go.sum
@@ -61,6 +61,8 @@ dmitri.shuralyov.com/html/belt v0.0.0-20180602232347-f7d459c86be0/go.mod h1:JLBr
|
||||
dmitri.shuralyov.com/service/change v0.0.0-20181023043359-a85b471d5412/go.mod h1:a1inKt/atXimZ4Mv927x+r7UpyzRUf4emIoiiSC2TN4=
|
||||
dmitri.shuralyov.com/state v0.0.0-20180228185332-28bcc343414c/go.mod h1:0PRwlb0D6DFvNNtx+9ybjezNCa8XF0xaYcETyp6rHWU=
|
||||
git.apache.org/thrift.git v0.0.0-20180902110319-2566ecd5d999/go.mod h1:fPE2ZNJGynbRyZ4dJvy6G277gSllfV2HJqblrnkyeyg=
|
||||
github.com/2456868764/certmagic v1.0.1 h1:dRzow2Npe9llFTBhNVl0fVe8Yi/Q14ygNonlaZUyDZQ=
|
||||
github.com/2456868764/certmagic v1.0.1/go.mod h1:LOn81EQYMPajdew6Ln6SVdHPxPqPv6jwsUg92kiNlcQ=
|
||||
github.com/AdaLogics/go-fuzz-headers v0.0.0-20210929163055-e81b3f25be97/go.mod h1:WpB7kf89yJUETZxQnP1kgYPNwlT2jjdDYUCoxVggM3g=
|
||||
github.com/AlecAivazis/survey/v2 v2.3.6 h1:NvTuVHISgTHEHeBFqt6BHOe4Ny/NwGZr7w+F8S9ziyw=
|
||||
github.com/AlecAivazis/survey/v2 v2.3.6/go.mod h1:4AuI9b7RjAR+G7v9+C4YSlX/YL3K3cWNXgWXOhllqvI=
|
||||
@@ -160,8 +162,8 @@ github.com/VividCortex/ewma v1.1.1/go.mod h1:2Tkkvm3sRDVXaiyucHiACn4cqf7DpdyLvmx
|
||||
github.com/VividCortex/gohistogram v1.0.0/go.mod h1:Pf5mBqqDxYaXu3hDrrU+w6nw50o/4+TcAqDqk/vUH7g=
|
||||
github.com/afex/hystrix-go v0.0.0-20180502004556-fa1af6a1f4f5/go.mod h1:SkGFH1ia65gfNATL8TAiHDNxPzPdmEL5uirI2Uyuz6c=
|
||||
github.com/agext/levenshtein v1.2.1/go.mod h1:JEDfjyjHDjOF/1e4FlBE/PkbqA9OfWu2ki2W0IB5558=
|
||||
github.com/agiledragon/gomonkey/v2 v2.9.0 h1:PDiKKybR596O6FHW+RVSG0Z7uGCBNbmbUXh3uCNQ7Hc=
|
||||
github.com/agiledragon/gomonkey/v2 v2.9.0/go.mod h1:ap1AmDzcVOAz1YpeJ3TCzIgstoaWLA6jbbgxfB4w2iY=
|
||||
github.com/agiledragon/gomonkey/v2 v2.11.0 h1:5oxSgA+tC1xuGsrIorR+sYiziYltmJyEZ9qA25b6l5U=
|
||||
github.com/agiledragon/gomonkey/v2 v2.11.0/go.mod h1:ap1AmDzcVOAz1YpeJ3TCzIgstoaWLA6jbbgxfB4w2iY=
|
||||
github.com/agl/ed25519 v0.0.0-20170116200512-5312a6153412/go.mod h1:WPjqKcmVOxf0XSf3YxCJs6N6AOSrOx3obionmG7T0y0=
|
||||
github.com/ahmetb/gen-crd-api-reference-docs v0.3.0/go.mod h1:TdjdkYhlOifCQWPs1UdTma97kQQMozf5h26hTuG70u8=
|
||||
github.com/alecthomas/jsonschema v0.0.0-20180308105923-f2c93856175a/go.mod h1:qpebaTNSsyUn5rPSJMsfqEtDw71TTggXM6stUDI16HA=
|
||||
@@ -1006,6 +1008,9 @@ github.com/klauspost/compress v1.13.0/go.mod h1:8dP1Hq4DHOhN9w426knH3Rhby4rFm6D8
|
||||
github.com/klauspost/compress v1.13.6/go.mod h1:/3/Vjq9QcHkK5uEr5lBEmyoZ1iFhe47etQ6QUkpK6sk=
|
||||
github.com/klauspost/compress v1.15.9 h1:wKRjX6JRtDdrE9qwa4b/Cip7ACOshUI4smpCQanqjSY=
|
||||
github.com/klauspost/compress v1.15.9/go.mod h1:PhcZ0MbTNciWF3rruxRgKxI5NkcHHrHUDtV4Yw2GlzU=
|
||||
github.com/klauspost/cpuid/v2 v2.0.12/go.mod h1:g2LTdtYhdyuGPqyWyv7qRAmj1WBqxuObKfj5c0PQa7c=
|
||||
github.com/klauspost/cpuid/v2 v2.2.5 h1:0E5MSMDEoAulmXNFquVs//DdoomxaoTY1kUhbc/qbZg=
|
||||
github.com/klauspost/cpuid/v2 v2.2.5/go.mod h1:Lcz8mBdAVJIBVzewtcLocK12l3Y+JytZYpaMropDUws=
|
||||
github.com/konsorten/go-windows-terminal-sequences v1.0.1/go.mod h1:T0+1ngSBFLxvqU3pZ+m/2kptfBszLMUkC4ZK/EgS/cQ=
|
||||
github.com/konsorten/go-windows-terminal-sequences v1.0.2/go.mod h1:T0+1ngSBFLxvqU3pZ+m/2kptfBszLMUkC4ZK/EgS/cQ=
|
||||
github.com/konsorten/go-windows-terminal-sequences v1.0.3/go.mod h1:T0+1ngSBFLxvqU3pZ+m/2kptfBszLMUkC4ZK/EgS/cQ=
|
||||
@@ -1055,6 +1060,8 @@ github.com/lib/pq v0.0.0-20150723085316-0dad96c0b94f/go.mod h1:5WUZQaWbwv1U+lTRe
|
||||
github.com/lib/pq v1.2.0/go.mod h1:5WUZQaWbwv1U+lTReE5YruASi9Al49XbQIvNi/34Woo=
|
||||
github.com/lib/pq v1.10.0 h1:Zx5DJFEYQXio93kgXnQ09fXNiUKsqv4OUEu2UtGcB1E=
|
||||
github.com/lib/pq v1.10.0/go.mod h1:AlVN5x4E4T544tWzH6hKfbfQvm3HdbOxrmggDNAPY9o=
|
||||
github.com/libdns/libdns v0.2.1 h1:Wu59T7wSHRgtA0cfxC+n1c/e+O3upJGWytknkmFEDis=
|
||||
github.com/libdns/libdns v0.2.1/go.mod h1:yQCXzk1lEZmmCPa857bnk4TsOiqYasqpyOEeSObbb40=
|
||||
github.com/liggitt/tabwriter v0.0.0-20181228230101-89fcab3d43de h1:9TO3cAIGXtEhnIaL+V+BEER86oLrvS+kWobKpbJuye0=
|
||||
github.com/liggitt/tabwriter v0.0.0-20181228230101-89fcab3d43de/go.mod h1:zAbeS9B/r2mtpb6U+EI2rYA5OAXxsYw6wTamcNW+zcE=
|
||||
github.com/lightstep/lightstep-tracer-common/golang/gogo v0.0.0-20190605223551-bc2310a04743/go.mod h1:qklhhLq1aX+mtWk9cPHPzaBjWImj5ULL6C7HFJtXQMM=
|
||||
@@ -1145,13 +1152,16 @@ github.com/mdlayher/netlink v1.4.1/go.mod h1:e4/KuJ+s8UhfUpO9z00/fDZZmhSrs+oxyqA
|
||||
github.com/mdlayher/socket v0.0.0-20210307095302-262dc9984e00/go.mod h1:GAFlyu4/XV68LkQKYzKhIo/WW7j3Zi0YRAz/BOoanUc=
|
||||
github.com/mgutz/ansi v0.0.0-20170206155736-9520e82c474b h1:j7+1HpAFS1zy5+Q4qx1fWh90gTKwiN4QCGoY9TWyyO4=
|
||||
github.com/mgutz/ansi v0.0.0-20170206155736-9520e82c474b/go.mod h1:01TrycV0kFyexm33Z7vhZRXopbI8J3TDReVlkTgMUxE=
|
||||
github.com/mholt/acmez v1.2.0 h1:1hhLxSgY5FvH5HCnGUuwbKY2VQVo8IU7rxXKSnZ7F30=
|
||||
github.com/mholt/acmez v1.2.0/go.mod h1:VT9YwH1xgNX1kmYY89gY8xPJC84BFAisjo8Egigt4kE=
|
||||
github.com/microcosm-cc/bluemonday v1.0.1/go.mod h1:hsXNsILzKxV+sX77C5b8FSuKF00vh2OMYv+xgHpAMF4=
|
||||
github.com/miekg/dns v1.0.14/go.mod h1:W1PPwlIAgtquWBMBEV9nkV9Cazfe8ScdGz/Lj7v3Nrg=
|
||||
github.com/miekg/dns v1.1.17/go.mod h1:WgzbA6oji13JREwiNsRDNfl7jYdPnmz+VEuLrA+/48M=
|
||||
github.com/miekg/dns v1.1.26/go.mod h1:bPDLeHnStXmXAq1m/Ch/hvfNHr14JKNPMBo3VZKjuso=
|
||||
github.com/miekg/dns v1.1.41/go.mod h1:p6aan82bvRIyn+zDIv9xYNUpwa73JcSh9BKwknJysuI=
|
||||
github.com/miekg/dns v1.1.43 h1:JKfpVSCB84vrAmHzyrsxB5NAr5kLoMXZArPSw7Qlgyg=
|
||||
github.com/miekg/dns v1.1.43/go.mod h1:+evo5L0630/F6ca/Z9+GAqzhjGyn8/c+TBaOyfEl0V4=
|
||||
github.com/miekg/dns v1.1.55 h1:GoQ4hpsj0nFLYe+bWiCToyrBEJXkQfOOIvFGFy0lEgo=
|
||||
github.com/miekg/dns v1.1.55/go.mod h1:uInx36IzPl7FYnDcMeVWxj9byh7DutNykX4G9Sj60FY=
|
||||
github.com/miekg/pkcs11 v1.0.2/go.mod h1:XsNlhZGX73bx86s2hdc/FuaLm2CPZJemRLMA+WTFxgs=
|
||||
github.com/miekg/pkcs11 v1.0.3/go.mod h1:XsNlhZGX73bx86s2hdc/FuaLm2CPZJemRLMA+WTFxgs=
|
||||
github.com/miekg/pkcs11 v1.1.1 h1:Ugu9pdy6vAYku5DEpVWVFPYnzV+bxB+iRdbuFSu7TvU=
|
||||
@@ -1658,6 +1668,12 @@ github.com/yvasiyarov/newrelic_platform_go v0.0.0-20140908184405-b21fdbd4370f/go
|
||||
github.com/zclconf/go-cty v1.2.0/go.mod h1:hOPWgoHbaTUnI5k4D2ld+GRpFJSCe6bCM7m1q/N4PQ8=
|
||||
github.com/zclconf/go-cty v1.4.0/go.mod h1:nHzOclRkoj++EU9ZjSrZvRG0BXIWt8c7loYc0qXAFGQ=
|
||||
github.com/zclconf/go-cty v1.7.1/go.mod h1:VDR4+I79ubFBGm1uJac1226K5yANQFHeauxPBoP54+o=
|
||||
github.com/zeebo/assert v1.1.0 h1:hU1L1vLTHsnO8x8c9KAR5GmM5QscxHg5RNU5z5qbUWY=
|
||||
github.com/zeebo/assert v1.1.0/go.mod h1:Pq9JiuJQpG8JLJdtkwrJESF0Foym2/D9XMU5ciN/wJ0=
|
||||
github.com/zeebo/blake3 v0.2.3 h1:TFoLXsjeXqRNFxSbk35Dk4YtszE/MQQGK10BH4ptoTg=
|
||||
github.com/zeebo/blake3 v0.2.3/go.mod h1:mjJjZpnsyIVtVgTOSpJ9vmRE4wgDeyt2HU3qXvvKCaQ=
|
||||
github.com/zeebo/pcg v1.0.1 h1:lyqfGeWiv4ahac6ttHs+I5hwtH/+1mrhlCtVNQM2kHo=
|
||||
github.com/zeebo/pcg v1.0.1/go.mod h1:09F0S9iiKrwn9rlI5yjLkmrug154/YRW6KnnXVDM/l4=
|
||||
github.com/ziutek/mymysql v1.5.4 h1:GB0qdRGsTwQSBVYuVShFBKaXSnSnYYC2d9knnE1LHFs=
|
||||
github.com/ziutek/mymysql v1.5.4/go.mod h1:LMSpPZ6DbqWFxNCHW77HeMg9I646SAhApZ/wKdgO/C0=
|
||||
go.etcd.io/bbolt v1.3.3/go.mod h1:IbVyRI1SCnLcuJnV2u8VeU0CEYM7e686BmAb1XKL+uU=
|
||||
@@ -1711,8 +1727,9 @@ go.uber.org/atomic v1.4.0/go.mod h1:gD2HeocX3+yG+ygLZcrzQJaqmWj9AIm7n08wl/qW/PE=
|
||||
go.uber.org/atomic v1.5.0/go.mod h1:sABNBOSYdrvTF6hTgEIbc7YasKWGhgEQZyfxyTvoXHQ=
|
||||
go.uber.org/atomic v1.6.0/go.mod h1:sABNBOSYdrvTF6hTgEIbc7YasKWGhgEQZyfxyTvoXHQ=
|
||||
go.uber.org/atomic v1.7.0/go.mod h1:fEN4uk6kAWBTFdckzkM89CLk9XfWZrxpCo0nPH17wJc=
|
||||
go.uber.org/atomic v1.9.0 h1:ECmE8Bn/WFTYwEW/bpKD3M8VtR/zQVbavAoalC1PYyE=
|
||||
go.uber.org/atomic v1.9.0/go.mod h1:fEN4uk6kAWBTFdckzkM89CLk9XfWZrxpCo0nPH17wJc=
|
||||
go.uber.org/atomic v1.11.0 h1:ZvwS0R+56ePWxUNi+Atn9dWONBPp/AUETXlHW0DxSjE=
|
||||
go.uber.org/atomic v1.11.0/go.mod h1:LUxbIzbOniOlMKjJjyPfpl4v+PKK2cNJn91OQbhoJI0=
|
||||
go.uber.org/automaxprocs v1.4.0/go.mod h1:/mTEdr7LvHhs0v7mjdxDreTz1OG5zdZGqgOnhWiR/+Q=
|
||||
go.uber.org/goleak v1.1.10/go.mod h1:8a7PlsEVH3e/a/GLqe5IIrQx6GzcnRmZEufDUTk4A7A=
|
||||
go.uber.org/goleak v1.1.11-0.20210813005559-691160354723/go.mod h1:cwTWslyiVhfpKIDGSZEM2HlOvcqm+tG4zioyIeLoqMQ=
|
||||
@@ -1722,8 +1739,9 @@ go.uber.org/multierr v1.1.0/go.mod h1:wR5kodmAFQ0UK8QlbwjlSNy0Z68gJhDJUG5sjR94q/
|
||||
go.uber.org/multierr v1.3.0/go.mod h1:VgVr7evmIr6uPjLBxg28wmKNXyqE9akIJ5XnfpiKl+4=
|
||||
go.uber.org/multierr v1.5.0/go.mod h1:FeouvMocqHpRaaGuG9EjoKcStLC43Zu/fmqdUMPcKYU=
|
||||
go.uber.org/multierr v1.6.0/go.mod h1:cdWPpRnG4AhwMwsgIHip0KRBQjJy5kYEpYjJxpXp9iU=
|
||||
go.uber.org/multierr v1.7.0 h1:zaiO/rmgFjbmCXdSYJWQcdvOCsthmdaHfr3Gm2Kx4Ec=
|
||||
go.uber.org/multierr v1.7.0/go.mod h1:7EAYxJLBy9rStEaz58O2t4Uvip6FSURkq8/ppBp95ak=
|
||||
go.uber.org/multierr v1.11.0 h1:blXXJkSxSSfBVBlC76pxqeO+LN3aDfLQo+309xJstO0=
|
||||
go.uber.org/multierr v1.11.0/go.mod h1:20+QtiLqy0Nd6FdQB9TLXag12DsQkrbs3htMFfDN80Y=
|
||||
go.uber.org/tools v0.0.0-20190618225709-2cfd321de3ee/go.mod h1:vJERXedbb3MVM5f9Ejo0C68/HhF8uaILCdgjnY+goOA=
|
||||
go.uber.org/zap v1.10.0/go.mod h1:vwi/ZaCAaUcBkycHslxD9B2zi4UTXhF60s6SWpuDF0Q=
|
||||
go.uber.org/zap v1.13.0/go.mod h1:zwrFLgMcdUuIBviXEYEH1YKNaOBnKXsx2IPda5bBwHM=
|
||||
@@ -1733,8 +1751,9 @@ go.uber.org/zap v1.17.0/go.mod h1:MXVU+bhUf/A7Xi2HNOnopQOrmycQ5Ih87HtOu4q5SSo=
|
||||
go.uber.org/zap v1.18.1/go.mod h1:xg/QME4nWcxGxrpdeYfq7UvYrLh66cuVKdrbD1XF/NI=
|
||||
go.uber.org/zap v1.19.0/go.mod h1:xg/QME4nWcxGxrpdeYfq7UvYrLh66cuVKdrbD1XF/NI=
|
||||
go.uber.org/zap v1.19.1/go.mod h1:j3DNczoxDZroyBnOT1L/Q79cfUMGZxlv/9dzN7SM1rI=
|
||||
go.uber.org/zap v1.21.0 h1:WefMeulhovoZ2sYXz7st6K0sLj7bBhpiFaud4r4zST8=
|
||||
go.uber.org/zap v1.21.0/go.mod h1:wjWOCqI0f2ZZrJF/UufIOkiC8ii6tm1iqIsLo76RfJw=
|
||||
go.uber.org/zap v1.24.0 h1:FiJd5l1UOLj0wCgbSE0rwwXHzEdAZS6hiiSnxJN/D60=
|
||||
go.uber.org/zap v1.24.0/go.mod h1:2kMP+WWQ8aoFoedH3T2sq6iJ2yDWpHbP0f6MQbS9Gkg=
|
||||
go4.org v0.0.0-20180809161055-417644f6feb5/go.mod h1:MkTOUMDaeVYJUOUsaDXIhWPZYa1yOyC1qaOBpL57BhE=
|
||||
golang.org/x/build v0.0.0-20190111050920-041ab4dc3f9d/go.mod h1:OWs+y06UdEOHN4y+MfF/py+xQ/tYqIWW03b70/CG9Rw=
|
||||
golang.org/x/crypto v0.0.0-20171113213409-9f005a07e0d3/go.mod h1:6SG95UA2DQfeDnfUPMdvaQW0Q7yPrPDi9nlGo2tz2b4=
|
||||
@@ -1775,8 +1794,8 @@ golang.org/x/crypto v0.0.0-20210920023735-84f357641f63/go.mod h1:GvvjBRRGRdwPK5y
|
||||
golang.org/x/crypto v0.0.0-20210921155107-089bfa567519/go.mod h1:GvvjBRRGRdwPK5ydBHafDWAxML/pGHZbMvKqRZ5+Abc=
|
||||
golang.org/x/crypto v0.0.0-20211215153901-e495a2d5b3d3/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4=
|
||||
golang.org/x/crypto v0.0.0-20220214200702-86341886e292/go.mod h1:IxCIyHEi3zRg3s0A5j5BB6A9Jmi73HwBIUl50j+osU4=
|
||||
golang.org/x/crypto v0.11.0 h1:6Ewdq3tDic1mg5xRO4milcWCfMVQhI4NkqWWvqejpuA=
|
||||
golang.org/x/crypto v0.11.0/go.mod h1:xgJhtzW8F9jGdVFWZESrid1U1bjeNy4zgy5cRr/CIio=
|
||||
golang.org/x/crypto v0.17.0 h1:r8bRNjWL3GshPW3gkd+RpvzWrZAwPS49OmTGZ/uhM4k=
|
||||
golang.org/x/crypto v0.17.0/go.mod h1:gCAAfMLgwOJRpTjQ2zCCt2OcSfYMTeZVSRtQlPC7Nq4=
|
||||
golang.org/x/exp v0.0.0-20190121172915-509febef88a4/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA=
|
||||
golang.org/x/exp v0.0.0-20190306152737-a1d7652674e8/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA=
|
||||
golang.org/x/exp v0.0.0-20190510132918-efd6b22b2522/go.mod h1:ZjyILWgesfNpC6sMxTJOJm9Kp84zZh5NQWvqDGG3Qr8=
|
||||
@@ -1817,7 +1836,8 @@ golang.org/x/mod v0.4.0/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA=
|
||||
golang.org/x/mod v0.4.1/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA=
|
||||
golang.org/x/mod v0.4.2/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA=
|
||||
golang.org/x/mod v0.5.1/go.mod h1:5OXOZSfqPIIbmVBIIKWRFfZjPR0E5r58TLhUjH0a2Ro=
|
||||
golang.org/x/mod v0.8.0 h1:LUYupSeNrTNCGzR/hVBk2NHZO4hXcVaW1k4Qx7rjPx8=
|
||||
golang.org/x/mod v0.11.0 h1:bUO06HqtnRcc/7l71XBe4WcqTZ+3AH1J59zWDDwLKgU=
|
||||
golang.org/x/mod v0.11.0/go.mod h1:iBbtSCu2XBx23ZKBPSOrRkjjQPZFPuis4dIYUhu/chs=
|
||||
golang.org/x/net v0.0.0-20180724234803-3673e40ba225/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4=
|
||||
golang.org/x/net v0.0.0-20180811021610-c39426892332/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4=
|
||||
golang.org/x/net v0.0.0-20180826012351-8a410e7b638d/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4=
|
||||
@@ -1894,8 +1914,8 @@ golang.org/x/net v0.0.0-20211112202133-69e39bad7dc2/go.mod h1:9nx3DQGgdP8bBQD5qx
|
||||
golang.org/x/net v0.0.0-20211209124913-491a49abca63/go.mod h1:9nx3DQGgdP8bBQD5qxJ1jj9UTztislL4KSBs9R2vV5Y=
|
||||
golang.org/x/net v0.0.0-20220127200216-cd36cc0744dd/go.mod h1:CfG3xpIq0wQ8r1q4Su4UZFWDARRcnwPjda9FqA0JpMk=
|
||||
golang.org/x/net v0.0.0-20220225172249-27dd8689420f/go.mod h1:CfG3xpIq0wQ8r1q4Su4UZFWDARRcnwPjda9FqA0JpMk=
|
||||
golang.org/x/net v0.12.0 h1:cfawfvKITfUsFCeJIHJrbSxpeu/E81khclypR0GVT50=
|
||||
golang.org/x/net v0.12.0/go.mod h1:zEVYFnQC7m/vmpQFELhcD1EWkZlX69l4oqgmer6hfKA=
|
||||
golang.org/x/net v0.17.0 h1:pVaXccu2ozPjCXewfr1S7xza/zcXTity9cCdXQYSjIM=
|
||||
golang.org/x/net v0.17.0/go.mod h1:NxSsAGuq816PNPmqtQdLE42eU2Fs7NoRIZrHJAlaCOE=
|
||||
golang.org/x/oauth2 v0.0.0-20180821212333-d2e6202438be/go.mod h1:N/0e6XlmueqKjAGxoOufVs8QHGRruUQn6yWY3a++T0U=
|
||||
golang.org/x/oauth2 v0.0.0-20181017192945-9dcd33a902f4/go.mod h1:N/0e6XlmueqKjAGxoOufVs8QHGRruUQn6yWY3a++T0U=
|
||||
golang.org/x/oauth2 v0.0.0-20181203162652-d668ce993890/go.mod h1:N/0e6XlmueqKjAGxoOufVs8QHGRruUQn6yWY3a++T0U=
|
||||
@@ -1932,8 +1952,8 @@ golang.org/x/sync v0.0.0-20201020160332-67f06af15bc9/go.mod h1:RxMgew5VJxzue5/jJ
|
||||
golang.org/x/sync v0.0.0-20201207232520-09787c993a3a/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sync v0.0.0-20210220032951-036812b2e83c/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sync v0.0.0-20220722155255-886fb9371eb4/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sync v0.2.0 h1:PUR+T4wwASmuSTYdKjYHI5TD22Wy5ogLU5qZCOLxBrI=
|
||||
golang.org/x/sync v0.2.0/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sync v0.3.0 h1:ftCYgMx6zT/asHUrPw8BLLscYtGznsLAnjq5RH9P66E=
|
||||
golang.org/x/sync v0.3.0/go.mod h1:FU7BRWz2tNW+3quACPkgCx/L+uEAv1htQ0V83Z9Rj+Y=
|
||||
golang.org/x/sys v0.0.0-20180823144017-11551d06cbcc/go.mod h1:STP8DvDyc/dI5b8T5hshtkjS+E42TnysNCUPdjciGhY=
|
||||
golang.org/x/sys v0.0.0-20180830151530-49385e6e1522/go.mod h1:STP8DvDyc/dI5b8T5hshtkjS+E42TnysNCUPdjciGhY=
|
||||
golang.org/x/sys v0.0.0-20180905080454-ebe1bf3edb33/go.mod h1:STP8DvDyc/dI5b8T5hshtkjS+E42TnysNCUPdjciGhY=
|
||||
@@ -2074,15 +2094,16 @@ golang.org/x/sys v0.0.0-20220503163025-988cb79eb6c6/go.mod h1:oPkhp1MJrh7nUepCBc
|
||||
golang.org/x/sys v0.0.0-20220715151400-c0bba94af5f8/go.mod h1:oPkhp1MJrh7nUepCBck5+mAzfO9JrbApNNgaTdGDITg=
|
||||
golang.org/x/sys v0.0.0-20220728004956-3c1f35247d10/go.mod h1:oPkhp1MJrh7nUepCBck5+mAzfO9JrbApNNgaTdGDITg=
|
||||
golang.org/x/sys v0.0.0-20220811171246-fbc7d0a398ab/go.mod h1:oPkhp1MJrh7nUepCBck5+mAzfO9JrbApNNgaTdGDITg=
|
||||
golang.org/x/sys v0.10.0 h1:SqMFp9UcQJZa+pmYuAKjd9xq1f0j5rLcDIk0mj4qAsA=
|
||||
golang.org/x/sys v0.10.0/go.mod h1:oPkhp1MJrh7nUepCBck5+mAzfO9JrbApNNgaTdGDITg=
|
||||
golang.org/x/sys v0.5.0/go.mod h1:oPkhp1MJrh7nUepCBck5+mAzfO9JrbApNNgaTdGDITg=
|
||||
golang.org/x/sys v0.15.0 h1:h48lPFYpsTvQJZF4EKyI4aLHaev3CxivZmv7yZig9pc=
|
||||
golang.org/x/sys v0.15.0/go.mod h1:/VUhepiaJMQUp4+oa/7Zr1D23ma6VTLIYjOOTFZPUcA=
|
||||
golang.org/x/term v0.0.0-20201117132131-f5c789dd3221/go.mod h1:Nr5EML6q2oocZ2LXRh80K7BxOlk5/8JxuGnuhpl+muw=
|
||||
golang.org/x/term v0.0.0-20201126162022-7de9c90e9dd1/go.mod h1:bj7SfCRtBDWHUb9snDiAeCFNEtKQo2Wmx5Cou7ajbmo=
|
||||
golang.org/x/term v0.0.0-20210220032956-6a3ed077a48d/go.mod h1:bj7SfCRtBDWHUb9snDiAeCFNEtKQo2Wmx5Cou7ajbmo=
|
||||
golang.org/x/term v0.0.0-20210503060354-a79de5458b56/go.mod h1:tfny5GFUkzUvx4ps4ajbZsCe5lw1metzhBm9T3x7oIY=
|
||||
golang.org/x/term v0.0.0-20210927222741-03fcf44c2211/go.mod h1:jbD1KX2456YbFQfuXm/mYQcufACuNUgVhRMnK/tPxf8=
|
||||
golang.org/x/term v0.10.0 h1:3R7pNqamzBraeqj/Tj8qt1aQ2HpmlC+Cx/qL/7hn4/c=
|
||||
golang.org/x/term v0.10.0/go.mod h1:lpqdcUyK/oCiQxvxVrppt5ggO2KCZ5QblwqPnfZ6d5o=
|
||||
golang.org/x/term v0.15.0 h1:y/Oo/a/q3IXu26lQgl04j/gjuBDOBlx7X6Om1j2CPW4=
|
||||
golang.org/x/term v0.15.0/go.mod h1:BDl952bC7+uMoWR75FIrCDx79TPU9oHkTZ9yRbYOrX0=
|
||||
golang.org/x/text v0.0.0-20170915032832-14c0d48ead0c/go.mod h1:NqM8EUOU14njkJ3fqMW+pc6Ldnwhi/IjpwHt7yyuwOQ=
|
||||
golang.org/x/text v0.3.0/go.mod h1:NqM8EUOU14njkJ3fqMW+pc6Ldnwhi/IjpwHt7yyuwOQ=
|
||||
golang.org/x/text v0.3.1-0.20180807135948-17ff2d5776d2/go.mod h1:NqM8EUOU14njkJ3fqMW+pc6Ldnwhi/IjpwHt7yyuwOQ=
|
||||
@@ -2092,8 +2113,8 @@ golang.org/x/text v0.3.4/go.mod h1:5Zoc/QRtKVWzQhOtBMvqHzDpF6irO9z98xDceosuGiQ=
|
||||
golang.org/x/text v0.3.5/go.mod h1:5Zoc/QRtKVWzQhOtBMvqHzDpF6irO9z98xDceosuGiQ=
|
||||
golang.org/x/text v0.3.6/go.mod h1:5Zoc/QRtKVWzQhOtBMvqHzDpF6irO9z98xDceosuGiQ=
|
||||
golang.org/x/text v0.3.7/go.mod h1:u+2+/6zg+i71rQMx5EYifcz6MCKuco9NR6JIITiCfzQ=
|
||||
golang.org/x/text v0.11.0 h1:LAntKIrcmeSKERyiOh0XMV39LXS8IE9UL2yP7+f5ij4=
|
||||
golang.org/x/text v0.11.0/go.mod h1:TvPlkZtksWOMsz7fbANvkp4WM8x/WCo/om8BMLbz+aE=
|
||||
golang.org/x/text v0.14.0 h1:ScX5w1eTa3QqT8oi6+ziP7dTV1S2+ALU0bI+0zXKWiQ=
|
||||
golang.org/x/text v0.14.0/go.mod h1:18ZOQIKpY8NJVqYksKHtTdi31H5itFRjB5/qKTNYzSU=
|
||||
golang.org/x/time v0.0.0-20180412165947-fbb02b2291d2/go.mod h1:tRJNPiyCQ0inRvYxbN9jk5I+vvW/OXSQhTDSoE431IQ=
|
||||
golang.org/x/time v0.0.0-20181108054448-85acf8d2951c/go.mod h1:tRJNPiyCQ0inRvYxbN9jk5I+vvW/OXSQhTDSoE431IQ=
|
||||
golang.org/x/time v0.0.0-20190308202827-9d24e82272b4/go.mod h1:tRJNPiyCQ0inRvYxbN9jk5I+vvW/OXSQhTDSoE431IQ=
|
||||
@@ -2182,7 +2203,8 @@ golang.org/x/tools v0.1.3/go.mod h1:o0xws9oXOQQZyjljx8fwUC0k7L1pTE6eaCbjGeHmOkk=
|
||||
golang.org/x/tools v0.1.4/go.mod h1:o0xws9oXOQQZyjljx8fwUC0k7L1pTE6eaCbjGeHmOkk=
|
||||
golang.org/x/tools v0.1.5/go.mod h1:o0xws9oXOQQZyjljx8fwUC0k7L1pTE6eaCbjGeHmOkk=
|
||||
golang.org/x/tools v0.1.8/go.mod h1:nABZi5QlRsZVlzPpHl034qft6wpY4eDcsTt5AaioBiU=
|
||||
golang.org/x/tools v0.6.0 h1:BOw41kyTf3PuCW1pVQf8+Cyg8pMlkYB1oo9iJ6D/lKM=
|
||||
golang.org/x/tools v0.10.0 h1:tvDr/iQoUqNdohiYm0LmmKcBk+q86lb9EprIUFhHHGg=
|
||||
golang.org/x/tools v0.10.0/go.mod h1:UJwyiVBsOA2uwvK/e5OY3GTpDUJriEd+/YlqAwLPmyM=
|
||||
golang.org/x/xerrors v0.0.0-20190717185122-a985d3407aa7/go.mod h1:I/5z698sn9Ka8TeJc9MKroUUfqBBauWjQqLJ2OPfmY0=
|
||||
golang.org/x/xerrors v0.0.0-20191011141410-1b5146add898/go.mod h1:I/5z698sn9Ka8TeJc9MKroUUfqBBauWjQqLJ2OPfmY0=
|
||||
golang.org/x/xerrors v0.0.0-20191204190536-9bdfabe68543/go.mod h1:I/5z698sn9Ka8TeJc9MKroUUfqBBauWjQqLJ2OPfmY0=
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
apiVersion: v2
|
||||
appVersion: 1.3.3
|
||||
appVersion: 1.4.0
|
||||
description: Helm chart for deploying higress gateways
|
||||
icon: https://higress.io/img/higress_logo_small.png
|
||||
home: http://higress.io/
|
||||
@@ -10,4 +10,4 @@ name: higress-core
|
||||
sources:
|
||||
- http://github.com/alibaba/higress
|
||||
type: application
|
||||
version: 1.3.3
|
||||
version: 1.4.0
|
||||
|
||||
@@ -154,6 +154,11 @@ spec:
|
||||
type: array
|
||||
httpPath:
|
||||
type: string
|
||||
paramFromEntireBody:
|
||||
properties:
|
||||
paramType:
|
||||
type: string
|
||||
type: object
|
||||
params:
|
||||
items:
|
||||
properties:
|
||||
|
||||
@@ -3,9 +3,13 @@
|
||||
# Refer to https://github.com/spiffe/spiffe/blob/master/standards/SPIFFE-ID.md#21-trust-domain
|
||||
trustDomain: "cluster.local"
|
||||
accessLogEncoding: TEXT
|
||||
{{- if .Values.global.o11y.enabled }}
|
||||
accessLogFile: "/var/log/proxy/access.log"
|
||||
{{- else }}
|
||||
accessLogFile: "/dev/stdout"
|
||||
{{- end }}
|
||||
ingressControllerMode: "OFF"
|
||||
accessLogFormat: '{"authority":"%REQ(:AUTHORITY)%","bytes_received":"%BYTES_RECEIVED%","bytes_sent":"%BYTES_SENT%","downstream_local_address":"%DOWNSTREAM_LOCAL_ADDRESS%","downstream_remote_address":"%DOWNSTREAM_REMOTE_ADDRESS%","duration":"%DURATION%","istio_policy_status":"%DYNAMIC_METADATA(istio.mixer:status)%","method":"%REQ(:METHOD)%","path":"%REQ(X-ENVOY-ORIGINAL-PATH?:PATH)%","protocol":"%PROTOCOL%","request_id":"%REQ(X-REQUEST-ID)%","requested_server_name":"%REQUESTED_SERVER_NAME%","response_code":"%RESPONSE_CODE%","response_flags":"%RESPONSE_FLAGS%","route_name":"%ROUTE_NAME%","start_time":"%START_TIME%","trace_id":"%REQ(X-B3-TRACEID)%","upstream_cluster":"%UPSTREAM_CLUSTER%","upstream_host":"%UPSTREAM_HOST%","upstream_local_address":"%UPSTREAM_LOCAL_ADDRESS%","upstream_service_time":"%RESP(X-ENVOY-UPSTREAM-SERVICE-TIME)%","upstream_transport_failure_reason":"%UPSTREAM_TRANSPORT_FAILURE_REASON%","user_agent":"%REQ(USER-AGENT)%","x_forwarded_for":"%REQ(X-FORWARDED-FOR)%"}
|
||||
accessLogFormat: '{"authority":"%REQ(X-ENVOY-ORIGINAL-HOST?:AUTHORITY)%","bytes_received":"%BYTES_RECEIVED%","bytes_sent":"%BYTES_SENT%","downstream_local_address":"%DOWNSTREAM_LOCAL_ADDRESS%","downstream_remote_address":"%DOWNSTREAM_REMOTE_ADDRESS%","duration":"%DURATION%","istio_policy_status":"%DYNAMIC_METADATA(istio.mixer:status)%","method":"%REQ(:METHOD)%","path":"%REQ(X-ENVOY-ORIGINAL-PATH?:PATH)%","protocol":"%PROTOCOL%","request_id":"%REQ(X-REQUEST-ID)%","requested_server_name":"%REQUESTED_SERVER_NAME%","response_code":"%RESPONSE_CODE%","response_flags":"%RESPONSE_FLAGS%","route_name":"%ROUTE_NAME%","start_time":"%START_TIME%","trace_id":"%REQ(X-B3-TRACEID)%","upstream_cluster":"%UPSTREAM_CLUSTER%","upstream_host":"%UPSTREAM_HOST%","upstream_local_address":"%UPSTREAM_LOCAL_ADDRESS%","upstream_service_time":"%RESP(X-ENVOY-UPSTREAM-SERVICE-TIME)%","upstream_transport_failure_reason":"%UPSTREAM_TRANSPORT_FAILURE_REASON%","user_agent":"%REQ(USER-AGENT)%","x_forwarded_for":"%REQ(X-FORWARDED-FOR)%"}
|
||||
|
||||
'
|
||||
dnsRefreshRate: 200s
|
||||
|
||||
@@ -70,6 +70,14 @@ spec:
|
||||
periodSeconds: 3
|
||||
timeoutSeconds: 5
|
||||
env:
|
||||
- name: PILOT_ENABLE_HEADLESS_SERVICE_POD_LISTENERS
|
||||
value: "false"
|
||||
- name: HIGRESS_SYSTEM_NS
|
||||
value: "{{ .Release.Namespace }}"
|
||||
- name: DEFAULT_UPSTREAM_CONCURRENCY_THRESHOLD
|
||||
value: "{{ .Values.global.defaultUpstreamConcurrencyThreshold }}"
|
||||
- name: ISTIO_GPRC_MAXRECVMSGSIZE
|
||||
value: "{{ .Values.global.xdsMaxRecvMsgSize }}"
|
||||
- name: ENBALE_SCOPED_RDS
|
||||
value: "{{ .Values.global.enableSRDS }}"
|
||||
- name: ON_DEMAND_RDS
|
||||
@@ -191,6 +199,8 @@ spec:
|
||||
- "serve"
|
||||
- --gatewaySelectorKey=higress
|
||||
- --gatewaySelectorValue={{ .Release.Namespace }}-{{ include "gateway.name" . }}
|
||||
- --gatewayHttpPort={{ .Values.gateway.httpPort }}
|
||||
- --gatewayHttpsPort={{ .Values.gateway.httpsPort }}
|
||||
{{- if not .Values.global.enableStatus }}
|
||||
- --enableStatus={{ .Values.global.enableStatus }}
|
||||
{{- end }}
|
||||
@@ -198,6 +208,8 @@ spec:
|
||||
{{- if .Values.global.watchNamespace }}
|
||||
- --watchNamespace={{ .Values.global.watchNamespace }}
|
||||
{{- end }}
|
||||
- --enableAutomaticHttps={{ .Values.controller.automaticHttps.enabled }}
|
||||
- --automaticHttpsEmail={{ .Values.controller.automaticHttps.email }}
|
||||
env:
|
||||
- name: POD_NAME
|
||||
valueFrom:
|
||||
|
||||
@@ -1,3 +1,4 @@
|
||||
{{- $o11y := .Values.global.o11y }}
|
||||
{{- $unprivilegedPortSupported := true }}
|
||||
{{- range $index, $node := (lookup "v1" "Node" "default" "").items }}
|
||||
{{- $kernelVersion := $node.status.nodeInfo.kernelVersion }}
|
||||
@@ -67,6 +68,40 @@ spec:
|
||||
value: "0"
|
||||
{{- end }}
|
||||
containers:
|
||||
{{- if $o11y.enabled }}
|
||||
{{- $config := $o11y.promtail }}
|
||||
- name: promtail
|
||||
image: {{ $config.image.repository }}:{{ $config.image.tag }}
|
||||
imagePullPolicy: IfNotPresent
|
||||
args:
|
||||
- -config.file=/etc/promtail/promtail.yaml
|
||||
env:
|
||||
- name: 'HOSTNAME'
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: 'spec.nodeName'
|
||||
ports:
|
||||
- containerPort: {{ $config.port }}
|
||||
name: http-metrics
|
||||
protocol: TCP
|
||||
readinessProbe:
|
||||
failureThreshold: 3
|
||||
httpGet:
|
||||
path: /ready
|
||||
port: {{ $config.port }}
|
||||
scheme: HTTP
|
||||
initialDelaySeconds: 10
|
||||
periodSeconds: 10
|
||||
successThreshold: 1
|
||||
timeoutSeconds: 1
|
||||
volumeMounts:
|
||||
- name: promtail-config
|
||||
mountPath: "/etc/promtail"
|
||||
- name: log
|
||||
mountPath: /var/log/proxy
|
||||
- name: tmp
|
||||
mountPath: /tmp
|
||||
{{- end }}
|
||||
- name: higress-gateway
|
||||
image: "{{ .Values.gateway.hub | default .Values.global.hub }}/{{ .Values.gateway.image | default "gateway" }}:{{ .Values.gateway.tag | default .Chart.AppVersion }}"
|
||||
args:
|
||||
@@ -88,7 +123,10 @@ spec:
|
||||
- ALL
|
||||
allowPrivilegeEscalation: false
|
||||
privileged: false
|
||||
# When enabling lite metrics, the configuration template files need to be replaced.
|
||||
{{- if not .Values.global.liteMetrics }}
|
||||
readOnlyRootFilesystem: true
|
||||
{{- end }}
|
||||
runAsUser: 1337
|
||||
runAsGroup: 1337
|
||||
runAsNonRoot: true
|
||||
@@ -102,7 +140,6 @@ spec:
|
||||
runAsGroup: 1337
|
||||
runAsNonRoot: false
|
||||
allowPrivilegeEscalation: true
|
||||
readOnlyRootFilesystem: true
|
||||
{{- end }}
|
||||
env:
|
||||
- name: NODE_NAME
|
||||
@@ -148,6 +185,10 @@ spec:
|
||||
value: "{{ $.Values.clusterName | default `Kubernetes` }}"
|
||||
- name: INSTANCE_NAME
|
||||
value: "higress-gateway"
|
||||
{{- if .Values.global.liteMetrics }}
|
||||
- name: LITE_METRICS
|
||||
value: "on"
|
||||
{{- end }}
|
||||
{{- if include "skywalking.enabled" . }}
|
||||
- name: ISTIO_BOOTSTRAP_OVERRIDE
|
||||
value: /etc/istio/custom-bootstrap/custom_bootstrap.json
|
||||
@@ -165,25 +206,25 @@ spec:
|
||||
protocol: TCP
|
||||
name: http-envoy-prom
|
||||
{{- if or .Values.global.local .Values.global.kind }}
|
||||
- containerPort: 80
|
||||
hostPort: 80
|
||||
- containerPort: {{ .Values.gateway.httpPort }}
|
||||
hostPort: {{ .Values.gateway.httpPort }}
|
||||
name: http
|
||||
protocol: TCP
|
||||
- containerPort: 443
|
||||
hostPort: 443
|
||||
- containerPort: {{ .Values.gateway.httpsPort }}
|
||||
hostPort: {{ .Values.gateway.httpsPort }}
|
||||
name: https
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
readinessProbe:
|
||||
failureThreshold: 30
|
||||
failureThreshold: {{ .Values.gateway.readinessFailureThreshold }}
|
||||
httpGet:
|
||||
path: /healthz/ready
|
||||
port: 15021
|
||||
scheme: HTTP
|
||||
initialDelaySeconds: 1
|
||||
periodSeconds: 2
|
||||
successThreshold: 1
|
||||
timeoutSeconds: 3
|
||||
initialDelaySeconds: {{ .Values.gateway.readinessInitialDelaySeconds }}
|
||||
periodSeconds: {{ .Values.gateway.readinessPeriodSeconds }}
|
||||
successThreshold: {{ .Values.gateway.readinessSuccessThreshold }}
|
||||
timeoutSeconds: {{ .Values.gateway.readinessTimeoutSeconds }}
|
||||
{{- if not (or .Values.global.local .Values.global.kind) }}
|
||||
resources:
|
||||
{{- toYaml .Values.gateway.resources | nindent 12 }}
|
||||
@@ -212,6 +253,10 @@ spec:
|
||||
- mountPath: /opt/plugins
|
||||
name: local-wasmplugins-volume
|
||||
{{- end }}
|
||||
{{- if $o11y.enabled }}
|
||||
- mountPath: /var/log/proxy
|
||||
name: log
|
||||
{{- end }}
|
||||
{{- if .Values.gateway.hostNetwork }}
|
||||
hostNetwork: {{ .Values.gateway.hostNetwork }}
|
||||
dnsPolicy: ClusterFirstWithHostNet
|
||||
@@ -258,6 +303,15 @@ spec:
|
||||
emptyDir: {}
|
||||
- name: proxy-socket
|
||||
emptyDir: {}
|
||||
{{- if $o11y.enabled }}
|
||||
- name: log
|
||||
emptyDir: {}
|
||||
- name: tmp
|
||||
emptyDir: {}
|
||||
- name: promtail-config
|
||||
configMap:
|
||||
name: higress-promtail
|
||||
{{- end }}
|
||||
- name: podinfo
|
||||
downwardAPI:
|
||||
defaultMode: 420
|
||||
|
||||
64
helm/core/templates/promtail.yaml
Normal file
64
helm/core/templates/promtail.yaml
Normal file
@@ -0,0 +1,64 @@
|
||||
{{- $o11y := .Values.global.o11y }}
|
||||
{{- if $o11y.enabled }}
|
||||
{{- $config := $o11y.promtail }}
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: higress-promtail
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
promtail.yaml: |
|
||||
server:
|
||||
log_level: info
|
||||
http_listen_port: {{ $config.port }}
|
||||
|
||||
clients:
|
||||
- url: http://higress-console-loki.{{ .Release.Namespace }}:3100/loki/api/v1/push
|
||||
|
||||
positions:
|
||||
filename: /tmp/promtail-positions.yaml
|
||||
target_config:
|
||||
sync_period: 10s
|
||||
scrape_configs:
|
||||
- job_name: access-logs
|
||||
static_configs:
|
||||
- targets:
|
||||
- localhost
|
||||
labels:
|
||||
__path__: /var/log/proxy/access.log
|
||||
pipeline_stages:
|
||||
- json:
|
||||
expressions:
|
||||
authority:
|
||||
method:
|
||||
path:
|
||||
protocol:
|
||||
request_id:
|
||||
response_code:
|
||||
response_flags:
|
||||
route_name:
|
||||
trace_id:
|
||||
upstream_cluster:
|
||||
upstream_host:
|
||||
upstream_transport_failure_reason:
|
||||
user_agent:
|
||||
x_forwarded_for:
|
||||
- labels:
|
||||
authority:
|
||||
method:
|
||||
path:
|
||||
protocol:
|
||||
request_id:
|
||||
response_code:
|
||||
response_flags:
|
||||
route_name:
|
||||
trace_id:
|
||||
upstream_cluster:
|
||||
upstream_host:
|
||||
upstream_transport_failure_reason:
|
||||
user_agent:
|
||||
x_forwarded_for:
|
||||
- timestamp:
|
||||
source: timestamp
|
||||
format: RFC3339Nano
|
||||
{{- end }}
|
||||
@@ -1,8 +1,11 @@
|
||||
revision: ""
|
||||
global:
|
||||
enableSRDS: false
|
||||
onDemandRDS: true
|
||||
hostRDSMergeSubset: true
|
||||
liteMetrics: false
|
||||
xdsMaxRecvMsgSize: "104857600"
|
||||
defaultUpstreamConcurrencyThreshold: 10000
|
||||
enableSRDS: true
|
||||
onDemandRDS: false
|
||||
hostRDSMergeSubset: false
|
||||
onlyPushRouteCluster: true
|
||||
# IngressClass filters which ingress resources the higress controller watches.
|
||||
# The default ingress class is higress.
|
||||
@@ -13,7 +16,7 @@ global:
|
||||
# resources in the k8s cluster.
|
||||
ingressClass: "higress"
|
||||
watchNamespace: ""
|
||||
disableAlpnH2: true
|
||||
disableAlpnH2: false
|
||||
enableStatus: true
|
||||
# whether to use autoscaling/v2 template for HPA settings
|
||||
# for internal usage only, not to be configured by users.
|
||||
@@ -151,12 +154,18 @@ global:
|
||||
# The number of successive failed probes before indicating readiness failure.
|
||||
readinessFailureThreshold: 30
|
||||
|
||||
# The number of successive successed probes before indicating readiness success.
|
||||
readinessSuccessThreshold: 30
|
||||
|
||||
# The initial delay for readiness probes in seconds.
|
||||
readinessInitialDelaySeconds: 1
|
||||
|
||||
# The period between readiness probes.
|
||||
readinessPeriodSeconds: 2
|
||||
|
||||
# The readiness timeout seconds
|
||||
readinessTimeoutSeconds: 3
|
||||
|
||||
# Resources for the sidecar.
|
||||
resources:
|
||||
requests:
|
||||
@@ -329,6 +338,20 @@ global:
|
||||
# Use the Mesh Control Protocol (MCP) for configuring Istiod. Requires an MCP source.
|
||||
useMCP: false
|
||||
|
||||
# Observability (o11y) configurations
|
||||
o11y:
|
||||
enabled: false
|
||||
promtail:
|
||||
image:
|
||||
repository: grafana/promtail
|
||||
tag: 2.9.4
|
||||
port: 3101
|
||||
resources:
|
||||
limits:
|
||||
cpu: 500m
|
||||
memory: 2Gi
|
||||
securityContext: {}
|
||||
|
||||
# The name of the CA for workload certificates.
|
||||
# For example, when caName=GkeWorkloadCertificate, GKE workload certificates
|
||||
# will be used as the certificates for workloads.
|
||||
@@ -373,6 +396,21 @@ gateway:
|
||||
replicas: 2
|
||||
image: gateway
|
||||
|
||||
# The number of successive failed probes before indicating readiness failure.
|
||||
readinessFailureThreshold: 30
|
||||
|
||||
# The number of successive successed probes before indicating readiness success.
|
||||
readinessSuccessThreshold: 1
|
||||
|
||||
# The initial delay for readiness probes in seconds.
|
||||
readinessInitialDelaySeconds: 1
|
||||
|
||||
# The period between readiness probes.
|
||||
readinessPeriodSeconds: 2
|
||||
|
||||
# The readiness timeout seconds
|
||||
readinessTimeoutSeconds: 3
|
||||
|
||||
hub: higress-registry.cn-hangzhou.cr.aliyuncs.com/higress
|
||||
tag: ""
|
||||
# revision declares which revision this gateway is a part of
|
||||
@@ -394,7 +432,8 @@ gateway:
|
||||
|
||||
# Pod environment variables
|
||||
env: {}
|
||||
|
||||
httpPort: 80
|
||||
httpsPort: 443
|
||||
hostNetwork: false
|
||||
|
||||
# Labels to apply to all resources
|
||||
@@ -505,6 +544,12 @@ controller:
|
||||
"port": 8888,
|
||||
"targetPort": 8888,
|
||||
},
|
||||
{
|
||||
"name": "http-solver",
|
||||
"protocol": "TCP",
|
||||
"port": 8889,
|
||||
"targetPort": 8889,
|
||||
},
|
||||
{
|
||||
"name": "grpc",
|
||||
"protocol": "TCP",
|
||||
@@ -543,6 +588,9 @@ controller:
|
||||
minReplicas: 1
|
||||
maxReplicas: 5
|
||||
targetCPUUtilizationPercentage: 80
|
||||
automaticHttps:
|
||||
enabled: true
|
||||
email: ""
|
||||
|
||||
## Discovery Settings
|
||||
pilot:
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
dependencies:
|
||||
- name: higress-core
|
||||
repository: file://../core
|
||||
version: 1.3.3
|
||||
version: 1.4.0
|
||||
- name: higress-console
|
||||
repository: https://higress.io/helm-charts/
|
||||
version: 1.3.1
|
||||
digest: sha256:585666df5da403450c5e586a71388bc0d029354b1100b20a50616f56711fa171
|
||||
generated: "2024-01-08T21:40:10.446936+08:00"
|
||||
version: 1.4.0
|
||||
digest: sha256:bf4c58ac28d4691907eab44a13eee398fc05ade95cdae07cb91d7e20ce4ba382
|
||||
generated: "2024-05-29T21:18:32.791995+08:00"
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
apiVersion: v2
|
||||
appVersion: 1.3.3
|
||||
appVersion: 1.4.0
|
||||
description: Helm chart for deploying Higress gateways
|
||||
icon: https://higress.io/img/higress_logo_small.png
|
||||
home: http://higress.io/
|
||||
@@ -12,9 +12,9 @@ sources:
|
||||
dependencies:
|
||||
- name: higress-core
|
||||
repository: "file://../core"
|
||||
version: 1.3.3
|
||||
version: 1.4.0
|
||||
- name: higress-console
|
||||
repository: "https://higress.io/helm-charts/"
|
||||
version: 1.3.1
|
||||
version: 1.4.0
|
||||
type: application
|
||||
version: 1.3.3
|
||||
version: 1.4.0
|
||||
|
||||
373
istio/1.12/patches/istio/20240115-optimize-rds-cache.patch
Normal file
373
istio/1.12/patches/istio/20240115-optimize-rds-cache.patch
Normal file
@@ -0,0 +1,373 @@
|
||||
diff -Naur istio/pilot/pkg/model/push_context.go istio-new/pilot/pkg/model/push_context.go
|
||||
--- istio/pilot/pkg/model/push_context.go 2024-01-15 20:46:45.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/model/push_context.go 2024-01-15 19:20:45.000000000 +0800
|
||||
@@ -96,6 +96,9 @@
|
||||
publicByGateway map[string][]config.Config
|
||||
// root vs namespace/name ->delegate vs virtualservice gvk/namespace/name
|
||||
delegates map[ConfigKey][]ConfigKey
|
||||
+ // Added by ingress
|
||||
+ byHost map[string][]config.Config
|
||||
+ // End added by ingress
|
||||
}
|
||||
|
||||
func newVirtualServiceIndex() virtualServiceIndex {
|
||||
@@ -104,6 +107,9 @@
|
||||
privateByNamespaceAndGateway: map[string]map[string][]config.Config{},
|
||||
exportedToNamespaceByGateway: map[string]map[string][]config.Config{},
|
||||
delegates: map[ConfigKey][]ConfigKey{},
|
||||
+ // Added by ingress
|
||||
+ byHost: map[string][]config.Config{},
|
||||
+ // End added by ingress
|
||||
}
|
||||
}
|
||||
|
||||
@@ -857,6 +863,13 @@
|
||||
return res
|
||||
}
|
||||
|
||||
+// Added by ingress
|
||||
+func (ps *PushContext) VirtualServicesForHost(proxy *Proxy, host string) []config.Config {
|
||||
+ return ps.virtualServiceIndex.byHost[host]
|
||||
+}
|
||||
+
|
||||
+// End added by ingress
|
||||
+
|
||||
// DelegateVirtualServicesConfigKey lists all the delegate virtual services configkeys associated with the provided virtual services
|
||||
func (ps *PushContext) DelegateVirtualServicesConfigKey(vses []config.Config) []ConfigKey {
|
||||
var out []ConfigKey
|
||||
@@ -1468,6 +1481,11 @@
|
||||
for _, virtualService := range vservices {
|
||||
ns := virtualService.Namespace
|
||||
rule := virtualService.Spec.(*networking.VirtualService)
|
||||
+ // Added by ingress
|
||||
+ for _, host := range rule.Hosts {
|
||||
+ ps.virtualServiceIndex.byHost[host] = append(ps.virtualServiceIndex.byHost[host], virtualService)
|
||||
+ }
|
||||
+ // End added by ingress
|
||||
gwNames := getGatewayNames(rule)
|
||||
if len(rule.ExportTo) == 0 {
|
||||
// No exportTo in virtualService. Use the global default
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/gateway.go istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-01-15 20:46:45.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-01-15 20:04:05.000000000 +0800
|
||||
@@ -28,6 +28,7 @@
|
||||
route "github.com/envoyproxy/go-control-plane/envoy/config/route/v3"
|
||||
hcm "github.com/envoyproxy/go-control-plane/envoy/extensions/filters/network/http_connection_manager/v3"
|
||||
tls "github.com/envoyproxy/go-control-plane/envoy/extensions/transport_sockets/tls/v3"
|
||||
+ discovery "github.com/envoyproxy/go-control-plane/envoy/service/discovery/v3"
|
||||
"github.com/hashicorp/go-multierror"
|
||||
|
||||
meshconfig "istio.io/api/mesh/v1alpha1"
|
||||
@@ -35,6 +36,7 @@
|
||||
"istio.io/istio/pilot/pkg/features"
|
||||
"istio.io/istio/pilot/pkg/model"
|
||||
istionetworking "istio.io/istio/pilot/pkg/networking"
|
||||
+ "istio.io/istio/pilot/pkg/networking/core/v1alpha3/envoyfilter"
|
||||
"istio.io/istio/pilot/pkg/networking/core/v1alpha3/extension"
|
||||
"istio.io/istio/pilot/pkg/networking/core/v1alpha3/mseingress"
|
||||
istio_route "istio.io/istio/pilot/pkg/networking/core/v1alpha3/route"
|
||||
@@ -423,8 +425,15 @@
|
||||
gatewayName string
|
||||
}
|
||||
|
||||
-func (configgen *ConfigGeneratorImpl) buildHostRDSConfig(node *model.Proxy, push *model.PushContext,
|
||||
- routeName string) *route.RouteConfiguration {
|
||||
+func (configgen *ConfigGeneratorImpl) buildHostRDSConfig(
|
||||
+ node *model.Proxy,
|
||||
+ req *model.PushRequest,
|
||||
+ routeName string,
|
||||
+ vsCache map[int][]virtualServiceContext,
|
||||
+ efw *model.EnvoyFilterWrapper,
|
||||
+ efKeys []string,
|
||||
+) (*discovery.Resource, bool) {
|
||||
+ push := req.Push
|
||||
var (
|
||||
hostRDSPort string
|
||||
hostRDSHost string
|
||||
@@ -432,7 +441,7 @@
|
||||
portAndHost := strings.SplitN(strings.TrimPrefix(routeName, constants.HigressHostRDSNamePrefix), ".", 2)
|
||||
if len(portAndHost) != 2 {
|
||||
log.Errorf("Invalid route %s when using Higress hostRDS", routeName)
|
||||
- return nil
|
||||
+ return nil, false
|
||||
}
|
||||
hostRDSPort = portAndHost[0]
|
||||
hostRDSHost = portAndHost[1]
|
||||
@@ -441,10 +450,24 @@
|
||||
rdsPort, err := strconv.Atoi(hostRDSPort)
|
||||
if err != nil {
|
||||
log.Errorf("Invalid port %s of route %s when using Higress hostRDS", hostRDSPort, routeName)
|
||||
- return nil
|
||||
+ return nil, false
|
||||
+ }
|
||||
+
|
||||
+ routeCache := &istio_route.Cache{
|
||||
+ RouteName: routeName,
|
||||
+ ProxyVersion: node.Metadata.IstioVersion,
|
||||
+ ListenerPort: rdsPort,
|
||||
+ // Use same host vs to cache, although the cache can be cleared when the port is different, this can be accepted
|
||||
+ VirtualServices: push.VirtualServicesForHost(node, hostRDSHost),
|
||||
+ EnvoyFilterKeys: efKeys,
|
||||
+ }
|
||||
+
|
||||
+ resource, exist := configgen.Cache.Get(routeCache)
|
||||
+ if exist {
|
||||
+ return resource, true
|
||||
}
|
||||
+
|
||||
listenerPort := uint32(rdsPort)
|
||||
- globalHTTPFilters := mseingress.ExtractGlobalHTTPFilters(node, push)
|
||||
|
||||
isH3DiscoveryNeeded := false
|
||||
|
||||
@@ -457,9 +480,9 @@
|
||||
break
|
||||
}
|
||||
}
|
||||
-
|
||||
gatewayRoutes := make(map[string]map[string][]*route.Route)
|
||||
gatewayVirtualServices := make(map[string][]config.Config)
|
||||
+ var listenerVirtualServices []virtualServiceContext
|
||||
var selectedVirtualServices []virtualServiceContext
|
||||
var vHost *route.VirtualHost
|
||||
serverIterator := func(mergedServers map[model.ServerPort]*model.MergedServers) {
|
||||
@@ -478,31 +501,8 @@
|
||||
gatewayVirtualServices[gatewayName] = virtualServices
|
||||
}
|
||||
for _, virtualService := range virtualServices {
|
||||
- hostMatch := false
|
||||
- var selectHost string
|
||||
- virtualServiceHosts := host.NewNames(virtualService.Spec.(*networking.VirtualService).Hosts)
|
||||
- for _, hostname := range virtualServiceHosts {
|
||||
- // exact match
|
||||
- if hostname == host.Name(hostRDSHost) {
|
||||
- hostMatch = true
|
||||
- selectHost = hostRDSHost
|
||||
- break
|
||||
- }
|
||||
- if features.HostRDSMergeSubset {
|
||||
- // subset match
|
||||
- if host.Name(hostRDSHost).SubsetOf(hostname) {
|
||||
- hostMatch = true
|
||||
- selectHost = string(hostname)
|
||||
- }
|
||||
- }
|
||||
- }
|
||||
- if !hostMatch {
|
||||
- continue
|
||||
- }
|
||||
- copiedVS := virtualService.DeepCopy()
|
||||
- copiedVS.Spec.(*networking.VirtualService).Hosts = []string{selectHost}
|
||||
- selectedVirtualServices = append(selectedVirtualServices, virtualServiceContext{
|
||||
- virtualService: copiedVS,
|
||||
+ listenerVirtualServices = append(listenerVirtualServices, virtualServiceContext{
|
||||
+ virtualService: virtualService,
|
||||
server: server,
|
||||
gatewayName: gatewayName,
|
||||
})
|
||||
@@ -510,15 +510,63 @@
|
||||
}
|
||||
}
|
||||
}
|
||||
- serverIterator(merged.MergedServers)
|
||||
- serverIterator(merged.MergedQUICTransportServers)
|
||||
- // Sort by subset
|
||||
- // before: ["*.abc.com", "*.com", "www.abc.com"]
|
||||
- // after: ["www.abc.com", "*.abc.com", "*.com"]
|
||||
- sort.SliceStable(selectedVirtualServices, func(i, j int) bool {
|
||||
- return host.Name(selectedVirtualServices[i].virtualService.Spec.(*networking.VirtualService).Hosts[0]).SubsetOf(
|
||||
- host.Name(selectedVirtualServices[j].virtualService.Spec.(*networking.VirtualService).Hosts[0]))
|
||||
- })
|
||||
+ var vsExists bool
|
||||
+ if listenerVirtualServices, vsExists = vsCache[rdsPort]; !vsExists {
|
||||
+ serverIterator(merged.MergedServers)
|
||||
+ serverIterator(merged.MergedQUICTransportServers)
|
||||
+ vsCache[rdsPort] = listenerVirtualServices
|
||||
+ }
|
||||
+ for _, vsCtx := range listenerVirtualServices {
|
||||
+ virtualService := vsCtx.virtualService
|
||||
+ hostMatch := false
|
||||
+ var selectHost string
|
||||
+ for _, hostname := range virtualService.Spec.(*networking.VirtualService).Hosts {
|
||||
+ // exact match
|
||||
+ if hostname == hostRDSHost {
|
||||
+ hostMatch = true
|
||||
+ selectHost = hostRDSHost
|
||||
+ break
|
||||
+ }
|
||||
+ if features.HostRDSMergeSubset {
|
||||
+ // subset match
|
||||
+ if host.Name(hostRDSHost).SubsetOf(host.Name(hostname)) {
|
||||
+ hostMatch = true
|
||||
+ selectHost = hostname
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ if !hostMatch {
|
||||
+ continue
|
||||
+ }
|
||||
+ if len(virtualService.Spec.(*networking.VirtualService).Hosts) > 1 {
|
||||
+ copiedVS := &networking.VirtualService{}
|
||||
+ copiedVS = virtualService.Spec.(*networking.VirtualService)
|
||||
+ copiedVS.Hosts = []string{selectHost}
|
||||
+ selectedVirtualServices = append(selectedVirtualServices, virtualServiceContext{
|
||||
+ virtualService: config.Config{
|
||||
+ Meta: virtualService.Meta,
|
||||
+ Spec: copiedVS,
|
||||
+ Status: virtualService.Status,
|
||||
+ },
|
||||
+ server: vsCtx.server,
|
||||
+ gatewayName: vsCtx.gatewayName,
|
||||
+ })
|
||||
+ } else {
|
||||
+ selectedVirtualServices = append(selectedVirtualServices, vsCtx)
|
||||
+ }
|
||||
+ }
|
||||
+ if features.HostRDSMergeSubset {
|
||||
+ // Sort by subset
|
||||
+ // before: ["*.abc.com", "*.com", "www.abc.com"]
|
||||
+ // after: ["www.abc.com", "*.abc.com", "*.com"]
|
||||
+ sort.SliceStable(selectedVirtualServices, func(i, j int) bool {
|
||||
+ return host.Name(selectedVirtualServices[i].virtualService.Spec.(*networking.VirtualService).Hosts[0]).SubsetOf(
|
||||
+ host.Name(selectedVirtualServices[j].virtualService.Spec.(*networking.VirtualService).Hosts[0]))
|
||||
+ })
|
||||
+ }
|
||||
+
|
||||
+ globalHTTPFilters := mseingress.ExtractGlobalHTTPFilters(node, push)
|
||||
+
|
||||
port := int(listenerPort)
|
||||
for _, ctx := range selectedVirtualServices {
|
||||
virtualService := ctx.virtualService
|
||||
@@ -605,25 +653,42 @@
|
||||
ValidateClusters: proto.BoolFalse,
|
||||
}
|
||||
|
||||
- return routeCfg
|
||||
+ routeCfg = envoyfilter.ApplyRouteConfigurationPatches(networking.EnvoyFilter_GATEWAY, node, efw, routeCfg)
|
||||
+ resource = &discovery.Resource{
|
||||
+ Name: routeName,
|
||||
+ Resource: util.MessageToAny(routeCfg),
|
||||
+ }
|
||||
+
|
||||
+ if features.EnableRDSCaching {
|
||||
+ configgen.Cache.Add(routeCache, req, resource)
|
||||
+ }
|
||||
+
|
||||
+ return resource, false
|
||||
}
|
||||
|
||||
// End added by ingress
|
||||
|
||||
-func (configgen *ConfigGeneratorImpl) buildGatewayHTTPRouteConfig(node *model.Proxy, push *model.PushContext,
|
||||
- routeName string) *route.RouteConfiguration {
|
||||
+// Modifed by ingress
|
||||
+func (configgen *ConfigGeneratorImpl) buildGatewayHTTPRouteConfig(
|
||||
+ node *model.Proxy,
|
||||
+ req *model.PushRequest,
|
||||
+ routeName string,
|
||||
+ vsCache map[int][]virtualServiceContext,
|
||||
+ efw *model.EnvoyFilterWrapper,
|
||||
+ efKeys []string,
|
||||
+) (*discovery.Resource, bool) {
|
||||
if node.MergedGateway == nil {
|
||||
log.Warnf("buildGatewayRoutes: no gateways for router %v", node.ID)
|
||||
- return &route.RouteConfiguration{
|
||||
- Name: routeName,
|
||||
- VirtualHosts: []*route.VirtualHost{},
|
||||
- ValidateClusters: proto.BoolFalse,
|
||||
- }
|
||||
+ return nil, false
|
||||
}
|
||||
-
|
||||
// Added by ingress
|
||||
+ push := req.Push
|
||||
if strings.HasPrefix(routeName, constants.HigressHostRDSNamePrefix) {
|
||||
- return configgen.buildHostRDSConfig(node, push, routeName)
|
||||
+ resource, cacheHit := configgen.buildHostRDSConfig(node, req, routeName, vsCache, efw, efKeys)
|
||||
+ if resource == nil {
|
||||
+ return nil, false
|
||||
+ }
|
||||
+ return resource, cacheHit
|
||||
}
|
||||
// End added by ingress
|
||||
|
||||
@@ -636,7 +701,7 @@
|
||||
|
||||
// This can happen when a gateway has recently been deleted. Envoy will still request route
|
||||
// information due to the draining of listeners, so we should not return an error.
|
||||
- return nil
|
||||
+ return nil, false
|
||||
}
|
||||
|
||||
servers := merged.ServersByRouteName[routeName]
|
||||
@@ -768,9 +833,16 @@
|
||||
ValidateClusters: proto.BoolFalse,
|
||||
}
|
||||
|
||||
- return routeCfg
|
||||
+ routeCfg = envoyfilter.ApplyRouteConfigurationPatches(networking.EnvoyFilter_GATEWAY, node, efw, routeCfg)
|
||||
+ resource := &discovery.Resource{
|
||||
+ Name: routeName,
|
||||
+ Resource: util.MessageToAny(routeCfg),
|
||||
+ }
|
||||
+ return resource, false
|
||||
}
|
||||
|
||||
+// End modified by ingress
|
||||
+
|
||||
// hashRouteList returns a hash of a list of pointers
|
||||
func hashRouteList(r []*route.Route) uint64 {
|
||||
hash := md5.New()
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/httproute.go istio-new/pilot/pkg/networking/core/v1alpha3/httproute.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/httproute.go 2024-01-15 20:46:41.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/httproute.go 2024-01-15 10:29:09.000000000 +0800
|
||||
@@ -78,17 +78,30 @@
|
||||
routeConfigurations = append(routeConfigurations, rc)
|
||||
}
|
||||
case model.Router:
|
||||
+ // Modified by ingress
|
||||
+ vsCache := make(map[int][]virtualServiceContext)
|
||||
+ envoyfilterKeys := efw.Keys()
|
||||
for _, routeName := range routeNames {
|
||||
- rc := configgen.buildGatewayHTTPRouteConfig(node, req.Push, routeName)
|
||||
- if rc != nil {
|
||||
- rc = envoyfilter.ApplyRouteConfigurationPatches(networking.EnvoyFilter_GATEWAY, node, efw, rc)
|
||||
- resource := &discovery.Resource{
|
||||
+ rc, cached := configgen.buildGatewayHTTPRouteConfig(node, req, routeName, vsCache, efw, envoyfilterKeys)
|
||||
+ if cached && !features.EnableUnsafeAssertions {
|
||||
+ hit++
|
||||
+ } else {
|
||||
+ miss++
|
||||
+ }
|
||||
+ if rc == nil {
|
||||
+ emptyRoute := &route.RouteConfiguration{
|
||||
+ Name: routeName,
|
||||
+ VirtualHosts: []*route.VirtualHost{},
|
||||
+ ValidateClusters: proto.BoolFalse,
|
||||
+ }
|
||||
+ rc = &discovery.Resource{
|
||||
Name: routeName,
|
||||
- Resource: util.MessageToAny(rc),
|
||||
+ Resource: util.MessageToAny(emptyRoute),
|
||||
}
|
||||
- routeConfigurations = append(routeConfigurations, resource)
|
||||
}
|
||||
+ routeConfigurations = append(routeConfigurations, rc)
|
||||
}
|
||||
+ // End modified by ingress
|
||||
}
|
||||
if !features.EnableRDSCaching {
|
||||
return routeConfigurations, model.DefaultXdsLogDetails
|
||||
diff -Naur istio/pilot/pkg/xds/discovery.go istio-new/pilot/pkg/xds/discovery.go
|
||||
--- istio/pilot/pkg/xds/discovery.go 2024-01-15 20:46:45.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/xds/discovery.go 2024-01-12 19:56:02.000000000 +0800
|
||||
@@ -392,6 +392,9 @@
|
||||
// ConfigUpdate implements ConfigUpdater interface, used to request pushes.
|
||||
// It replaces the 'clear cache' from v1.
|
||||
func (s *DiscoveryServer) ConfigUpdate(req *model.PushRequest) {
|
||||
+ if req.Full {
|
||||
+ log.Infof("full push happen, reason:%v", req.Reason)
|
||||
+ }
|
||||
inboundConfigUpdates.Increment()
|
||||
s.InboundUpdates.Inc()
|
||||
s.pushChannel <- req
|
||||
60
istio/1.12/patches/istio/20240201-optimize-default-arg.patch
Normal file
60
istio/1.12/patches/istio/20240201-optimize-default-arg.patch
Normal file
@@ -0,0 +1,60 @@
|
||||
diff -Naur istio/pilot/cmd/pilot-agent/status/util/stats.go istio-new/pilot/cmd/pilot-agent/status/util/stats.go
|
||||
--- istio/pilot/cmd/pilot-agent/status/util/stats.go 2024-02-01 10:20:13.000000000 +0800
|
||||
+++ istio-new/pilot/cmd/pilot-agent/status/util/stats.go 2024-01-31 22:44:53.000000000 +0800
|
||||
@@ -73,7 +73,7 @@
|
||||
localHostAddr = "localhost"
|
||||
}
|
||||
|
||||
- readinessURL := fmt.Sprintf("http://%s:%d/stats?usedonly&filter=%s", localHostAddr, adminPort, readyStatsRegex)
|
||||
+ readinessURL := fmt.Sprintf("http://%s:%d/stats?usedonly", localHostAddr, adminPort)
|
||||
stats, err := http.DoHTTPGetWithTimeout(readinessURL, readinessTimeout)
|
||||
if err != nil {
|
||||
return nil, false, err
|
||||
@@ -105,7 +105,7 @@
|
||||
localHostAddr = "localhost"
|
||||
}
|
||||
|
||||
- stats, err := http.DoHTTPGet(fmt.Sprintf("http://%s:%d/stats?usedonly&filter=%s", localHostAddr, adminPort, updateStatsRegex))
|
||||
+ stats, err := http.DoHTTPGet(fmt.Sprintf("http://%s:%d/stats?usedonly", localHostAddr, adminPort))
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
diff -Naur istio/pilot/pkg/features/pilot.go istio-new/pilot/pkg/features/pilot.go
|
||||
--- istio/pilot/pkg/features/pilot.go 2024-02-01 10:20:17.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/features/pilot.go 2024-02-01 10:16:18.000000000 +0800
|
||||
@@ -575,6 +575,8 @@
|
||||
"If enabled, each host in virtualservice will have an independent RDS, which is used with SRDS").Get()
|
||||
OnDemandRDS = env.RegisterBoolVar("ON_DEMAND_RDS", false,
|
||||
"If enabled, the on demand filter will be added to the HCM filters").Get()
|
||||
+ DefaultUpstreamConcurrencyThreshold = env.RegisterIntVar("DEFAULT_UPSTREAM_CONCURRENCY_THRESHOLD", 1000000,
|
||||
+ "The default threshold of max_requests/max_pending_requests/max_connections of circuit breaker").Get()
|
||||
// End added by ingress
|
||||
)
|
||||
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/cluster.go istio-new/pilot/pkg/networking/core/v1alpha3/cluster.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/cluster.go 2024-02-01 10:20:17.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/cluster.go 2024-02-01 10:16:05.000000000 +0800
|
||||
@@ -61,6 +61,7 @@
|
||||
|
||||
// getDefaultCircuitBreakerThresholds returns a copy of the default circuit breaker thresholds for the given traffic direction.
|
||||
func getDefaultCircuitBreakerThresholds() *cluster.CircuitBreakers_Thresholds {
|
||||
+ // Modified by ingress
|
||||
return &cluster.CircuitBreakers_Thresholds{
|
||||
// DefaultMaxRetries specifies the default for the Envoy circuit breaker parameter max_retries. This
|
||||
// defines the maximum number of parallel retries a given Envoy will allow to the upstream cluster. Envoy defaults
|
||||
@@ -68,11 +69,12 @@
|
||||
// where multiple endpoints in a cluster are terminated. In these scenarios the circuit breaker can kick
|
||||
// in before Pilot is able to deliver an updated endpoint list to Envoy, leading to client-facing 503s.
|
||||
MaxRetries: &wrappers.UInt32Value{Value: math.MaxUint32},
|
||||
- MaxRequests: &wrappers.UInt32Value{Value: math.MaxUint32},
|
||||
- MaxConnections: &wrappers.UInt32Value{Value: math.MaxUint32},
|
||||
- MaxPendingRequests: &wrappers.UInt32Value{Value: math.MaxUint32},
|
||||
+ MaxRequests: &wrappers.UInt32Value{Value: uint32(features.DefaultUpstreamConcurrencyThreshold)},
|
||||
+ MaxConnections: &wrappers.UInt32Value{Value: uint32(features.DefaultUpstreamConcurrencyThreshold)},
|
||||
+ MaxPendingRequests: &wrappers.UInt32Value{Value: uint32(features.DefaultUpstreamConcurrencyThreshold)},
|
||||
TrackRemaining: true,
|
||||
}
|
||||
+ // End modified by ingress
|
||||
}
|
||||
|
||||
// BuildClusters returns the list of clusters for the given proxy. This is the CDS output
|
||||
@@ -0,0 +1,88 @@
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/gateway.go istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-02-01 13:53:17.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-02-01 13:52:11.000000000 +0800
|
||||
@@ -501,6 +501,16 @@
|
||||
gatewayVirtualServices[gatewayName] = virtualServices
|
||||
}
|
||||
for _, virtualService := range virtualServices {
|
||||
+ virtualServiceHosts := host.NewNames(virtualService.Spec.(*networking.VirtualService).Hosts)
|
||||
+ serverHosts := host.NamesForNamespace(server.Hosts, virtualService.Namespace)
|
||||
+
|
||||
+ // We have two cases here:
|
||||
+ // 1. virtualService hosts are 1.foo.com, 2.foo.com, 3.foo.com and server hosts are ns/*.foo.com
|
||||
+ // 2. virtualService hosts are *.foo.com, and server hosts are ns/1.foo.com, ns/2.foo.com, ns/3.foo.com
|
||||
+ intersectingHosts := serverHosts.Intersection(virtualServiceHosts)
|
||||
+ if len(intersectingHosts) == 0 {
|
||||
+ continue
|
||||
+ }
|
||||
listenerVirtualServices = append(listenerVirtualServices, virtualServiceContext{
|
||||
virtualService: virtualService,
|
||||
server: server,
|
||||
@@ -615,22 +625,24 @@
|
||||
|
||||
// check all hostname if is not exist with HttpsRedirect set to true
|
||||
// create VirtualHost to redirect
|
||||
- for _, hostname := range server.Hosts {
|
||||
- if !server.GetTls().GetHttpsRedirect() {
|
||||
- continue
|
||||
- }
|
||||
- if vHost != nil && host.Name(hostname) == host.Name(hostRDSHost) {
|
||||
+ if server.GetTls().GetHttpsRedirect() {
|
||||
+ if vHost != nil {
|
||||
vHost.RequireTls = route.VirtualHost_ALL
|
||||
- continue
|
||||
+ } else {
|
||||
+ vHost = &route.VirtualHost{
|
||||
+ Name: util.DomainName(hostRDSHost, port),
|
||||
+ Domains: buildGatewayVirtualHostDomains(hostRDSHost, port),
|
||||
+ IncludeRequestAttemptCount: true,
|
||||
+ RequireTls: route.VirtualHost_ALL,
|
||||
+ }
|
||||
}
|
||||
- vHost = &route.VirtualHost{
|
||||
- Name: util.DomainName(hostname, port),
|
||||
- Domains: buildGatewayVirtualHostDomains(hostname, port),
|
||||
- IncludeRequestAttemptCount: true,
|
||||
- RequireTls: route.VirtualHost_ALL,
|
||||
+ } else if vHost != nil {
|
||||
+ mode := server.GetTls().GetMode()
|
||||
+ if mode == networking.ServerTLSSettings_MUTUAL ||
|
||||
+ mode == networking.ServerTLSSettings_ISTIO_MUTUAL {
|
||||
+ vHost.AllowServerNames = append(vHost.AllowServerNames, server.Hosts...)
|
||||
}
|
||||
}
|
||||
-
|
||||
}
|
||||
var virtualHosts []*route.VirtualHost
|
||||
if vHost == nil {
|
||||
@@ -642,6 +654,30 @@
|
||||
Routes: []*route.Route{},
|
||||
}}
|
||||
} else {
|
||||
+ sort.SliceStable(vHost.AllowServerNames, func(i, j int) bool {
|
||||
+ hostI := vHost.AllowServerNames[i]
|
||||
+ hostJ := vHost.AllowServerNames[j]
|
||||
+ if host.Name(hostI).SubsetOf(host.Name(hostJ)) {
|
||||
+ return true
|
||||
+ }
|
||||
+ return hostI < hostJ
|
||||
+ })
|
||||
+ var uniqueServerNames []string
|
||||
+ hasAllCatch := false
|
||||
+ for i, name := range vHost.AllowServerNames {
|
||||
+ if name == "*" {
|
||||
+ hasAllCatch = true
|
||||
+ break
|
||||
+ }
|
||||
+ if i == 0 || vHost.AllowServerNames[i-1] != name {
|
||||
+ uniqueServerNames = append(uniqueServerNames, name)
|
||||
+ }
|
||||
+ }
|
||||
+ if hasAllCatch {
|
||||
+ vHost.AllowServerNames = nil
|
||||
+ } else {
|
||||
+ vHost.AllowServerNames = uniqueServerNames
|
||||
+ }
|
||||
vHost.Routes = istio_route.CombineVHostRoutes(vHost.Routes)
|
||||
virtualHosts = append(virtualHosts, vHost)
|
||||
}
|
||||
41
istio/1.12/patches/istio/20240202-fix-rds-cache.patch
Normal file
41
istio/1.12/patches/istio/20240202-fix-rds-cache.patch
Normal file
@@ -0,0 +1,41 @@
|
||||
diff -Naur istio/pilot/pkg/xds/discovery.go istio-new/pilot/pkg/xds/discovery.go
|
||||
--- istio/pilot/pkg/xds/discovery.go 2024-02-02 16:26:49.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/xds/discovery.go 2024-02-02 15:38:53.000000000 +0800
|
||||
@@ -18,6 +18,7 @@
|
||||
"context"
|
||||
"fmt"
|
||||
"strconv"
|
||||
+ "strings"
|
||||
"sync"
|
||||
"time"
|
||||
|
||||
@@ -41,6 +42,7 @@
|
||||
"istio.io/istio/pilot/pkg/util/sets"
|
||||
v3 "istio.io/istio/pilot/pkg/xds/v3"
|
||||
"istio.io/istio/pkg/cluster"
|
||||
+ "istio.io/istio/pkg/config/constants"
|
||||
"istio.io/istio/pkg/security"
|
||||
)
|
||||
|
||||
@@ -332,6 +334,21 @@
|
||||
} else {
|
||||
// Otherwise, just clear the updated configs
|
||||
s.Cache.Clear(req.ConfigsUpdated)
|
||||
+ //Added by ingress
|
||||
+ trimKeyMap := make(map[model.ConfigKey]struct{})
|
||||
+ for configKey := range req.ConfigsUpdated {
|
||||
+ if strings.HasPrefix(configKey.Name, constants.IstioIngressGatewayName+"-") {
|
||||
+ trimKeyMap[model.ConfigKey{
|
||||
+ Kind: configKey.Kind,
|
||||
+ Name: strings.TrimPrefix(configKey.Name, constants.IstioIngressGatewayName+"-"),
|
||||
+ Namespace: configKey.Namespace,
|
||||
+ }] = struct{}{}
|
||||
+ }
|
||||
+ }
|
||||
+ if len(trimKeyMap) > 0 {
|
||||
+ s.Cache.Clear(trimKeyMap)
|
||||
+ }
|
||||
+ //End added by ingress
|
||||
}
|
||||
}
|
||||
|
||||
@@ -0,0 +1,21 @@
|
||||
diff -Naur istio/pilot/cmd/pilot-agent/status/util/stats.go istio-new/pilot/cmd/pilot-agent/status/util/stats.go
|
||||
--- istio/pilot/cmd/pilot-agent/status/util/stats.go 2024-02-04 18:48:18.000000000 +0800
|
||||
+++ istio-new/pilot/cmd/pilot-agent/status/util/stats.go 2024-02-04 09:35:42.000000000 +0800
|
||||
@@ -37,7 +37,7 @@
|
||||
updateStatsRegex = "^(cluster_manager\\.cds|listener_manager\\.lds)\\.(update_success|update_rejected)$"
|
||||
)
|
||||
|
||||
-var readinessTimeout = time.Second * 3 // Default Readiness timeout. It is set the same in helm charts.
|
||||
+var readinessTimeout = time.Second * 60 // Default Readiness timeout. It is set the same in helm charts.
|
||||
|
||||
type stat struct {
|
||||
name string
|
||||
@@ -105,7 +105,7 @@
|
||||
localHostAddr = "localhost"
|
||||
}
|
||||
|
||||
- stats, err := http.DoHTTPGet(fmt.Sprintf("http://%s:%d/stats?usedonly", localHostAddr, adminPort))
|
||||
+ stats, err := http.DoHTTPGetWithTimeout(fmt.Sprintf("http://%s:%d/stats?usedonly", localHostAddr, adminPort), readinessTimeout)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
132
istio/1.12/patches/istio/20240304-fix-gwapi-rds-cache.patch
Normal file
132
istio/1.12/patches/istio/20240304-fix-gwapi-rds-cache.patch
Normal file
@@ -0,0 +1,132 @@
|
||||
diff -Naur istio/pilot/pkg/config/kube/gateway/conversion.go istio-new/pilot/pkg/config/kube/gateway/conversion.go
|
||||
--- istio/pilot/pkg/config/kube/gateway/conversion.go 2024-03-04 17:35:34.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/config/kube/gateway/conversion.go 2024-03-04 16:58:26.000000000 +0800
|
||||
@@ -450,7 +450,7 @@
|
||||
name = fmt.Sprintf("%s/%s/%s.%s", obj.GroupVersionKind.Kind, obj.Name, *sectionName, obj.Namespace)
|
||||
}
|
||||
return map[string]string{
|
||||
- constants.InternalParentName: name,
|
||||
+ constants.InternalParentNames: name,
|
||||
}
|
||||
}
|
||||
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/gateway.go istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-03-04 17:35:34.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-03-04 17:23:10.000000000 +0800
|
||||
@@ -49,6 +49,7 @@
|
||||
"istio.io/istio/pkg/config/gateway"
|
||||
"istio.io/istio/pkg/config/host"
|
||||
"istio.io/istio/pkg/config/protocol"
|
||||
+ "istio.io/istio/pkg/config/schema/gvk"
|
||||
"istio.io/istio/pkg/config/security"
|
||||
"istio.io/istio/pkg/proto"
|
||||
"istio.io/istio/pkg/util/istiomultierror"
|
||||
@@ -453,12 +454,43 @@
|
||||
return nil, false
|
||||
}
|
||||
|
||||
+ hostVs := push.VirtualServicesForHost(node, hostRDSHost)
|
||||
+
|
||||
+ var httpRoutes []config.Config
|
||||
+
|
||||
+ for _, vs := range hostVs {
|
||||
+ if len(vs.Annotations) == 0 {
|
||||
+ continue
|
||||
+ }
|
||||
+ if parents, ok := vs.Annotations[constants.InternalParentNames]; ok {
|
||||
+ typeNames := strings.Split(parents, ",")
|
||||
+ for _, typeName := range typeNames {
|
||||
+ if !strings.HasPrefix(typeName, "HTTPRoute/") {
|
||||
+ continue
|
||||
+ }
|
||||
+ nsNameStr := strings.TrimPrefix(typeName, "HTTPRoute/")
|
||||
+ nsName := strings.SplitN(nsNameStr, ".", 2)
|
||||
+ if len(nsName) != 2 {
|
||||
+ continue
|
||||
+ }
|
||||
+ httpRoutes = append(httpRoutes, config.Config{
|
||||
+ Meta: config.Meta{
|
||||
+ GroupVersionKind: gvk.HTTPRoute,
|
||||
+ Name: nsName[0],
|
||||
+ Namespace: nsName[1],
|
||||
+ },
|
||||
+ })
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+
|
||||
routeCache := &istio_route.Cache{
|
||||
RouteName: routeName,
|
||||
ProxyVersion: node.Metadata.IstioVersion,
|
||||
ListenerPort: rdsPort,
|
||||
// Use same host vs to cache, although the cache can be cleared when the port is different, this can be accepted
|
||||
- VirtualServices: push.VirtualServicesForHost(node, hostRDSHost),
|
||||
+ VirtualServices: hostVs,
|
||||
+ HTTPRoutes: httpRoutes,
|
||||
EnvoyFilterKeys: efKeys,
|
||||
}
|
||||
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/route/route_cache.go istio-new/pilot/pkg/networking/core/v1alpha3/route/route_cache.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/route/route_cache.go 2024-03-04 17:35:30.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/route/route_cache.go 2024-03-04 17:24:19.000000000 +0800
|
||||
@@ -43,9 +43,12 @@
|
||||
// This depends on DNSCapture.
|
||||
DNSAutoAllocate bool
|
||||
|
||||
- ListenerPort int
|
||||
- Services []*model.Service
|
||||
- VirtualServices []config.Config
|
||||
+ ListenerPort int
|
||||
+ Services []*model.Service
|
||||
+ VirtualServices []config.Config
|
||||
+ // Added by ingress
|
||||
+ HTTPRoutes []config.Config
|
||||
+ // End added by ingress
|
||||
DestinationRules []*config.Config
|
||||
EnvoyFilterKeys []string
|
||||
}
|
||||
@@ -81,6 +84,11 @@
|
||||
for _, vs := range r.VirtualServices {
|
||||
configs = append(configs, model.ConfigKey{Kind: gvk.VirtualService, Name: vs.Name, Namespace: vs.Namespace})
|
||||
}
|
||||
+ // Added by ingress
|
||||
+ for _, route := range r.HTTPRoutes {
|
||||
+ configs = append(configs, model.ConfigKey{Kind: gvk.HTTPRoute, Name: route.Name, Namespace: route.Namespace})
|
||||
+ }
|
||||
+ // End added by ingress
|
||||
for _, dr := range r.DestinationRules {
|
||||
configs = append(configs, model.ConfigKey{Kind: gvk.DestinationRule, Name: dr.Name, Namespace: dr.Namespace})
|
||||
}
|
||||
@@ -107,6 +115,11 @@
|
||||
for _, vs := range r.VirtualServices {
|
||||
params = append(params, vs.Name+"/"+vs.Namespace)
|
||||
}
|
||||
+ // Added by ingress
|
||||
+ for _, route := range r.HTTPRoutes {
|
||||
+ params = append(params, route.Name+"/"+route.Namespace)
|
||||
+ }
|
||||
+ // End added by ingress
|
||||
for _, dr := range r.DestinationRules {
|
||||
params = append(params, dr.Name+"/"+dr.Namespace)
|
||||
}
|
||||
diff -Naur istio/pkg/config/constants/constants.go istio-new/pkg/config/constants/constants.go
|
||||
--- istio/pkg/config/constants/constants.go 2024-03-04 17:35:34.000000000 +0800
|
||||
+++ istio-new/pkg/config/constants/constants.go 2024-03-04 16:58:05.000000000 +0800
|
||||
@@ -15,8 +15,6 @@
|
||||
package constants
|
||||
|
||||
const (
|
||||
- InternalParentNames = "internal.istio.io/parents"
|
||||
-
|
||||
InternalRouteSemantics = "internal.istio.io/route-semantics"
|
||||
|
||||
RouteSemanticsGateway = "gateway"
|
||||
@@ -129,7 +127,7 @@
|
||||
AlwaysPushLabel = "internal.istio.io/always-push"
|
||||
|
||||
// InternalParentName declares the original resource of an internally-generate config. This is used by the gateway-api.
|
||||
- InternalParentName = "internal.istio.io/parent"
|
||||
+ InternalParentNames = "internal.istio.io/parents"
|
||||
|
||||
// TrustworthyJWTPath is the default 3P token to authenticate with third party services
|
||||
TrustworthyJWTPath = "./var/run/secrets/tokens/istio-token"
|
||||
@@ -0,0 +1,56 @@
|
||||
diff -Naur istio/pilot/pkg/config/kube/gateway/conversion.go istio-new/pilot/pkg/config/kube/gateway/conversion.go
|
||||
--- istio/pilot/pkg/config/kube/gateway/conversion.go 2024-03-08 17:23:49.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/config/kube/gateway/conversion.go 2024-03-08 17:02:50.000000000 +0800
|
||||
@@ -16,6 +16,7 @@
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
+ "path"
|
||||
"regexp"
|
||||
"sort"
|
||||
"strconv"
|
||||
@@ -28,6 +29,7 @@
|
||||
gatewayapiV1beta1 "sigs.k8s.io/gateway-api/apis/v1beta1"
|
||||
|
||||
istio "istio.io/api/networking/v1alpha3"
|
||||
+ "istio.io/istio/pilot/pkg/features"
|
||||
"istio.io/istio/pilot/pkg/model"
|
||||
"istio.io/istio/pilot/pkg/model/credentials"
|
||||
"istio.io/istio/pilot/pkg/model/kstatus"
|
||||
@@ -290,6 +292,16 @@
|
||||
return ret
|
||||
}
|
||||
|
||||
+// Added by ingress
|
||||
+func generateRouteName(obj config.Config) string {
|
||||
+ if obj.Namespace == features.HigressSystemNs {
|
||||
+ return obj.Name
|
||||
+ }
|
||||
+ return path.Join(obj.Namespace, obj.Name)
|
||||
+}
|
||||
+
|
||||
+// End added by ingress
|
||||
+
|
||||
func buildHTTPVirtualServices(ctx *KubernetesResources, obj config.Config, gateways map[parentKey]map[gatewayapiV1beta1.SectionName]*parentInfo, gatewayRoutes map[string]map[string]*config.Config, domain string) {
|
||||
route := obj.Spec.(*gatewayapiV1beta1.HTTPRouteSpec)
|
||||
|
||||
@@ -307,7 +319,7 @@
|
||||
for _, r := range route.Rules {
|
||||
// TODO: implement rewrite, timeout, mirror, corspolicy, retries
|
||||
vs := &istio.HTTPRoute{
|
||||
- Name: obj.Name,
|
||||
+ Name: generateRouteName(obj),
|
||||
}
|
||||
for _, match := range r.Matches {
|
||||
uri, err := createURIMatch(match)
|
||||
diff -Naur istio/pilot/pkg/features/pilot.go istio-new/pilot/pkg/features/pilot.go
|
||||
--- istio/pilot/pkg/features/pilot.go 2024-03-08 17:23:49.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/features/pilot.go 2024-03-08 17:00:05.000000000 +0800
|
||||
@@ -577,6 +577,7 @@
|
||||
"If enabled, the on demand filter will be added to the HCM filters").Get()
|
||||
DefaultUpstreamConcurrencyThreshold = env.RegisterIntVar("DEFAULT_UPSTREAM_CONCURRENCY_THRESHOLD", 1000000,
|
||||
"The default threshold of max_requests/max_pending_requests/max_connections of circuit breaker").Get()
|
||||
+ HigressSystemNs = env.RegisterStringVar("HIGRESS_SYSTEM_NS", "higress-system", "The system namespace of Higress").Get()
|
||||
// End added by ingress
|
||||
)
|
||||
|
||||
20
istio/1.12/patches/istio/20240422-fix-copyvs.patch
Normal file
20
istio/1.12/patches/istio/20240422-fix-copyvs.patch
Normal file
@@ -0,0 +1,20 @@
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/gateway.go istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-04-22 18:08:26.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-04-22 18:07:46.000000000 +0800
|
||||
@@ -581,13 +581,13 @@
|
||||
continue
|
||||
}
|
||||
if len(virtualService.Spec.(*networking.VirtualService).Hosts) > 1 {
|
||||
- copiedVS := &networking.VirtualService{}
|
||||
- copiedVS = virtualService.Spec.(*networking.VirtualService)
|
||||
+ copiedVS := networking.VirtualService{}
|
||||
+ copiedVS = *(virtualService.Spec.(*networking.VirtualService))
|
||||
copiedVS.Hosts = []string{selectHost}
|
||||
selectedVirtualServices = append(selectedVirtualServices, virtualServiceContext{
|
||||
virtualService: config.Config{
|
||||
Meta: virtualService.Meta,
|
||||
- Spec: copiedVS,
|
||||
+ Spec: &copiedVS,
|
||||
Status: virtualService.Status,
|
||||
},
|
||||
server: vsCtx.server,
|
||||
83
istio/1.12/patches/istio/20240518-optimize-rds-cache.patch
Normal file
83
istio/1.12/patches/istio/20240518-optimize-rds-cache.patch
Normal file
@@ -0,0 +1,83 @@
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/gateway.go istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-05-18 19:09:14.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-05-18 18:08:30.000000000 +0800
|
||||
@@ -457,8 +457,46 @@
|
||||
hostVs := push.VirtualServicesForHost(node, hostRDSHost)
|
||||
|
||||
var httpRoutes []config.Config
|
||||
+ var vsDependent []config.Config
|
||||
+
|
||||
+ cacheable := true
|
||||
|
||||
for _, vs := range hostVs {
|
||||
+ vsSpec := vs.Spec.(*networking.VirtualService)
|
||||
+ for _, vsHttpRoute := range vsSpec.Http {
|
||||
+ // check if dynamic port exists, we should not cache RDS
|
||||
+ for _, vsRoute := range vsHttpRoute.Route {
|
||||
+ if vsRoute.Destination.Port == nil {
|
||||
+ cacheable = false
|
||||
+ }
|
||||
+ for _, fallbackDestination := range vsRoute.FallbackClusters {
|
||||
+ if fallbackDestination.Port == nil {
|
||||
+ cacheable = false
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ if vsHttpRoute.Mirror != nil && vsHttpRoute.Mirror.Port == nil {
|
||||
+ cacheable = false
|
||||
+ }
|
||||
+ if vsHttpRoute.Delegate != nil {
|
||||
+ vsDependent = append(vsDependent, config.Config{
|
||||
+ Meta: config.Meta{
|
||||
+ GroupVersionKind: gvk.VirtualService,
|
||||
+ Name: vsHttpRoute.Delegate.Name,
|
||||
+ Namespace: vsHttpRoute.Delegate.Namespace,
|
||||
+ },
|
||||
+ Spec: networking.VirtualService{},
|
||||
+ })
|
||||
+ }
|
||||
+ }
|
||||
+ vsDependent = append(vsDependent, config.Config{
|
||||
+ Meta: config.Meta{
|
||||
+ GroupVersionKind: gvk.VirtualService,
|
||||
+ Name: vs.Name,
|
||||
+ Namespace: vs.Namespace,
|
||||
+ },
|
||||
+ Spec: vs.Spec,
|
||||
+ })
|
||||
if len(vs.Annotations) == 0 {
|
||||
continue
|
||||
}
|
||||
@@ -489,14 +527,19 @@
|
||||
ProxyVersion: node.Metadata.IstioVersion,
|
||||
ListenerPort: rdsPort,
|
||||
// Use same host vs to cache, although the cache can be cleared when the port is different, this can be accepted
|
||||
- VirtualServices: hostVs,
|
||||
+ VirtualServices: vsDependent,
|
||||
HTTPRoutes: httpRoutes,
|
||||
EnvoyFilterKeys: efKeys,
|
||||
}
|
||||
|
||||
- resource, exist := configgen.Cache.Get(routeCache)
|
||||
- if exist {
|
||||
- return resource, true
|
||||
+ var resource *discovery.Resource
|
||||
+ if cacheable {
|
||||
+ resource, exist := configgen.Cache.Get(routeCache)
|
||||
+ if exist {
|
||||
+ return resource, true
|
||||
+ }
|
||||
+ } else {
|
||||
+ log.Warnf("route cache is disabled for RDS:%s", routeName)
|
||||
}
|
||||
|
||||
listenerPort := uint32(rdsPort)
|
||||
@@ -727,7 +770,7 @@
|
||||
Resource: util.MessageToAny(routeCfg),
|
||||
}
|
||||
|
||||
- if features.EnableRDSCaching {
|
||||
+ if features.EnableRDSCaching && cacheable {
|
||||
configgen.Cache.Add(routeCache, req, resource)
|
||||
}
|
||||
|
||||
752
istio/1.12/patches/istio/20240519-proxy-start-script.patch
Normal file
752
istio/1.12/patches/istio/20240519-proxy-start-script.patch
Normal file
@@ -0,0 +1,752 @@
|
||||
diff -Naur istio/pilot/docker/Dockerfile.proxyv2 istio-new/pilot/docker/Dockerfile.proxyv2
|
||||
--- istio/pilot/docker/Dockerfile.proxyv2 2024-05-19 16:40:42.706769894 +0800
|
||||
+++ istio-new/pilot/docker/Dockerfile.proxyv2 2024-05-19 16:07:20.630730574 +0800
|
||||
@@ -28,6 +28,7 @@
|
||||
|
||||
# Copy Envoy bootstrap templates used by pilot-agent
|
||||
COPY envoy_bootstrap.json /var/lib/istio/envoy/envoy_bootstrap_tmpl.json
|
||||
+COPY envoy_bootstrap_lite.json /var/lib/istio/envoy/envoy_bootstrap_lite_tmpl.json
|
||||
COPY gcp_envoy_bootstrap.json /var/lib/istio/envoy/gcp_envoy_bootstrap_tmpl.json
|
||||
|
||||
# Install Envoy.
|
||||
@@ -47,5 +48,30 @@
|
||||
# COPY metadata-exchange-filter.wasm /etc/istio/extensions/metadata-exchange-filter.wasm
|
||||
# COPY metadata-exchange-filter.compiled.wasm /etc/istio/extensions/metadata-exchange-filter.compiled.wasm
|
||||
|
||||
+RUN apt-get update && \
|
||||
+ apt-get install --no-install-recommends -y \
|
||||
+ logrotate \
|
||||
+ cron \
|
||||
+ && apt-get upgrade -y \
|
||||
+ && apt-get clean
|
||||
+
|
||||
+# Latest releases available at https://github.com/aptible/supercronic/releases
|
||||
+ENV SUPERCRONIC_URL=https://higress.io/release-binary/supercronic-linux-${TARGETARCH:-amd64} \
|
||||
+ SUPERCRONIC=supercronic-linux-${TARGETARCH:-amd64}
|
||||
+
|
||||
+RUN curl -fsSLO "$SUPERCRONIC_URL" \
|
||||
+ && chmod +x "$SUPERCRONIC" \
|
||||
+ && mv "$SUPERCRONIC" "/usr/local/bin/${SUPERCRONIC}" \
|
||||
+ && ln -s "/usr/local/bin/${SUPERCRONIC}" /usr/local/bin/supercronic
|
||||
+
|
||||
+
|
||||
+COPY higress-proxy-start.sh /usr/local/bin/higress-proxy-start.sh
|
||||
+
|
||||
+COPY higress-proxy-container-init.sh /usr/local/bin/higress-proxy-container-init.sh
|
||||
+
|
||||
+RUN chmod a+x /usr/local/bin/higress-proxy-container-init.sh;/usr/local/bin/higress-proxy-container-init.sh
|
||||
+
|
||||
+RUN chmod a+x /usr/local/bin/higress-proxy-start.sh
|
||||
+
|
||||
# The pilot-agent will bootstrap Envoy.
|
||||
-ENTRYPOINT ["/usr/local/bin/pilot-agent"]
|
||||
+ENTRYPOINT ["/usr/local/bin/higress-proxy-start.sh"]
|
||||
diff -Naur istio/tools/istio-docker.mk istio-new/tools/istio-docker.mk
|
||||
--- istio/tools/istio-docker.mk 2024-05-19 16:40:42.734769895 +0800
|
||||
+++ istio-new/tools/istio-docker.mk 2024-05-19 16:02:43.222725126 +0800
|
||||
@@ -96,6 +96,9 @@
|
||||
docker.proxyv2: BUILD_ARGS=--build-arg proxy_version=istio-proxy:${PROXY_REPO_SHA} --build-arg istio_version=${VERSION} --build-arg BASE_VERSION=${BASE_VERSION} --build-arg SIDECAR=${SIDECAR} --build-arg HUB=${HUB}
|
||||
docker.proxyv2: ${ISTIO_ENVOY_BOOTSTRAP_CONFIG_DIR}/envoy_bootstrap.json
|
||||
docker.proxyv2: ${ISTIO_ENVOY_BOOTSTRAP_CONFIG_DIR}/gcp_envoy_bootstrap.json
|
||||
+docker.proxyv2: ${ISTIO_ENVOY_BOOTSTRAP_CONFIG_DIR}/higress-proxy-start.sh
|
||||
+docker.proxyv2: ${ISTIO_ENVOY_BOOTSTRAP_CONFIG_DIR}/higress-proxy-container-init.sh
|
||||
+docker.proxyv2: ${ISTIO_ENVOY_BOOTSTRAP_CONFIG_DIR}/envoy_bootstrap_lite.json
|
||||
docker.proxyv2: ${ISTIO_ENVOY_LINUX_ARM64_RELEASE_DIR}/${SIDECAR}
|
||||
docker.proxyv2: ${ISTIO_ENVOY_LINUX_AMD64_RELEASE_DIR}/${SIDECAR}
|
||||
docker.proxyv2: $(ISTIO_OUT_LINUX)/pilot-agent
|
||||
diff -Naur istio/tools/packaging/common/envoy_bootstrap_lite.json istio-new/tools/packaging/common/envoy_bootstrap_lite.json
|
||||
--- istio/tools/packaging/common/envoy_bootstrap_lite.json 1970-01-01 08:00:00.000000000 +0800
|
||||
+++ istio-new/tools/packaging/common/envoy_bootstrap_lite.json 2024-05-19 16:36:39.274765113 +0800
|
||||
@@ -0,0 +1,642 @@
|
||||
+{
|
||||
+ "node": {
|
||||
+ "id": "{{ .nodeID }}",
|
||||
+ "cluster": "{{ .cluster }}",
|
||||
+ "locality": {
|
||||
+ {{- if .region }}
|
||||
+ "region": "{{ .region }}"
|
||||
+ {{- end }}
|
||||
+ {{- if .zone }}
|
||||
+ {{- if .region }}
|
||||
+ ,
|
||||
+ {{- end }}
|
||||
+ "zone": "{{ .zone }}"
|
||||
+ {{- end }}
|
||||
+ {{- if .sub_zone }}
|
||||
+ {{- if or .region .zone }}
|
||||
+ ,
|
||||
+ {{- end }}
|
||||
+ "sub_zone": "{{ .sub_zone }}"
|
||||
+ {{- end }}
|
||||
+ },
|
||||
+ "metadata": {{ .meta_json_str }}
|
||||
+ },
|
||||
+ "layered_runtime": {
|
||||
+ "layers": [
|
||||
+ {
|
||||
+ "name": "global config",
|
||||
+ "static_layer": {{ .runtime_flags }}
|
||||
+ },
|
||||
+ {
|
||||
+ "name": "admin",
|
||||
+ "admin_layer": {}
|
||||
+ }
|
||||
+ ]
|
||||
+ },
|
||||
+ "stats_config": {
|
||||
+ "use_all_default_tags": false,
|
||||
+ "stats_tags": [
|
||||
+ {
|
||||
+ "tag_name": "response_code_class",
|
||||
+ "regex": "_rq(_(\\dxx))$"
|
||||
+ },
|
||||
+ {
|
||||
+ "tag_name": "listener_address",
|
||||
+ "regex": "^listener\\.(((?:[_.[:digit:]]*|[_\\[\\]aAbBcCdDeEfF[:digit:]]*))\\.)"
|
||||
+ },
|
||||
+ {
|
||||
+ "tag_name": "http_conn_manager_prefix",
|
||||
+ "regex": "^http\\.(((outbound_([0-9]{1,3}\\.{0,1}){4}_\\d{0,5})|([^\\.]+))\\.)"
|
||||
+ },
|
||||
+ {
|
||||
+ "tag_name": "cluster_name",
|
||||
+ "regex": "^cluster\\.((.*?)\\.)(http1\\.|http2\\.|health_check\\.|zone\\.|external\\.|circuit_breakers\\.|[^\\.]+$)"
|
||||
+ }
|
||||
+ ],
|
||||
+ "stats_matcher": {
|
||||
+ "exclusion_list": {
|
||||
+ "patterns": [
|
||||
+ {
|
||||
+ "prefix": "vhost"
|
||||
+ },
|
||||
+ {
|
||||
+ "safe_regex": {"regex": "^http.*rds.*", "google_re2":{}}
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ }
|
||||
+ },
|
||||
+ "admin": {
|
||||
+ "access_log_path": "/dev/null",
|
||||
+ "profile_path": "/var/lib/istio/data/envoy.prof",
|
||||
+ "address": {
|
||||
+ "socket_address": {
|
||||
+ "address": "{{ .localhost }}",
|
||||
+ "port_value": {{ .config.ProxyAdminPort }}
|
||||
+ }
|
||||
+ }
|
||||
+ },
|
||||
+ "dynamic_resources": {
|
||||
+ "lds_config": {
|
||||
+ "ads": {},
|
||||
+ "initial_fetch_timeout": "0s",
|
||||
+ "resource_api_version": "V3"
|
||||
+ },
|
||||
+ "cds_config": {
|
||||
+ "ads": {},
|
||||
+ "initial_fetch_timeout": "0s",
|
||||
+ "resource_api_version": "V3"
|
||||
+ },
|
||||
+ "ads_config": {
|
||||
+ "api_type": "{{ .xds_type }}",
|
||||
+ "set_node_on_first_message_only": true,
|
||||
+ "transport_api_version": "V3",
|
||||
+ "grpc_services": [
|
||||
+ {
|
||||
+ "envoy_grpc": {
|
||||
+ "cluster_name": "xds-grpc"
|
||||
+ }
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ },
|
||||
+ "static_resources": {
|
||||
+ "clusters": [
|
||||
+ {
|
||||
+ "name": "prometheus_stats",
|
||||
+ "type": "STATIC",
|
||||
+ "connect_timeout": "0.250s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "prometheus_stats",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {
|
||||
+ "protocol": "TCP",
|
||||
+ "address": "{{ .localhost }}",
|
||||
+ "port_value": {{ .config.ProxyAdminPort }}
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ },
|
||||
+ {
|
||||
+ "name": "agent",
|
||||
+ "type": "STATIC",
|
||||
+ "connect_timeout": "0.250s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "agent",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {
|
||||
+ "protocol": "TCP",
|
||||
+ "address": "{{ .localhost }}",
|
||||
+ "port_value": {{ .config.StatusPort }}
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ },
|
||||
+ {
|
||||
+ "name": "sds-grpc",
|
||||
+ "type": "STATIC",
|
||||
+ "typed_extension_protocol_options": {
|
||||
+ "envoy.extensions.upstreams.http.v3.HttpProtocolOptions": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.upstreams.http.v3.HttpProtocolOptions",
|
||||
+ "explicit_http_config": {
|
||||
+ "http2_protocol_options": {}
|
||||
+ }
|
||||
+ }
|
||||
+ },
|
||||
+ "connect_timeout": "1s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "sds-grpc",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "pipe": {
|
||||
+ "path": "{{ .config.ConfigPath }}/SDS"
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ },
|
||||
+ {
|
||||
+ "name": "xds-grpc",
|
||||
+ "type" : "STATIC",
|
||||
+ "connect_timeout": "1s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "xds-grpc",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "pipe": {
|
||||
+ "path": "{{ .config.ConfigPath }}/XDS"
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ },
|
||||
+ "circuit_breakers": {
|
||||
+ "thresholds": [
|
||||
+ {
|
||||
+ "priority": "DEFAULT",
|
||||
+ "max_connections": 100000,
|
||||
+ "max_pending_requests": 100000,
|
||||
+ "max_requests": 100000
|
||||
+ },
|
||||
+ {
|
||||
+ "priority": "HIGH",
|
||||
+ "max_connections": 100000,
|
||||
+ "max_pending_requests": 100000,
|
||||
+ "max_requests": 100000
|
||||
+ }
|
||||
+ ]
|
||||
+ },
|
||||
+ "upstream_connection_options": {
|
||||
+ "tcp_keepalive": {
|
||||
+ "keepalive_time": 300
|
||||
+ }
|
||||
+ },
|
||||
+ "max_requests_per_connection": 1,
|
||||
+ "typed_extension_protocol_options": {
|
||||
+ "envoy.extensions.upstreams.http.v3.HttpProtocolOptions": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.upstreams.http.v3.HttpProtocolOptions",
|
||||
+ "explicit_http_config": {
|
||||
+ "http2_protocol_options": {}
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{ if .zipkin }}
|
||||
+ ,
|
||||
+ {
|
||||
+ "name": "zipkin",
|
||||
+ {{- if .tracing_tls }}
|
||||
+ "transport_socket": {{ .tracing_tls }},
|
||||
+ {{- end }}
|
||||
+ "type": "STRICT_DNS",
|
||||
+ "respect_dns_ttl": true,
|
||||
+ "dns_lookup_family": "{{ .dns_lookup_family }}",
|
||||
+ "dns_refresh_rate": "30s",
|
||||
+ "connect_timeout": "1s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "zipkin",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {{ .zipkin }}
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ {{ else if .lightstep }}
|
||||
+ ,
|
||||
+ {
|
||||
+ "name": "lightstep",
|
||||
+ {{- if .tracing_tls }}
|
||||
+ "transport_socket": {{ .tracing_tls }},
|
||||
+ {{- end }}
|
||||
+ "typed_extension_protocol_options": {
|
||||
+ "envoy.extensions.upstreams.http.v3.HttpProtocolOptions": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.upstreams.http.v3.HttpProtocolOptions",
|
||||
+ "explicit_http_config": {
|
||||
+ "http2_protocol_options": {}
|
||||
+ }
|
||||
+ }
|
||||
+ },
|
||||
+ "type": "STRICT_DNS",
|
||||
+ "respect_dns_ttl": true,
|
||||
+ "dns_lookup_family": "{{ .dns_lookup_family }}",
|
||||
+ "connect_timeout": "1s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "lightstep",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {{ .lightstep }}
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ {{ else if .datadog }}
|
||||
+ ,
|
||||
+ {
|
||||
+ "name": "datadog_agent",
|
||||
+ {{- if .tracing_tls }}
|
||||
+ "transport_socket": {{ .tracing_tls }},
|
||||
+ {{- end }}
|
||||
+ "connect_timeout": "1s",
|
||||
+ "type": "STRICT_DNS",
|
||||
+ "respect_dns_ttl": true,
|
||||
+ "dns_lookup_family": "{{ .dns_lookup_family }}",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "datadog_agent",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {{ .datadog }}
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+ {{- if .envoy_metrics_service_address }}
|
||||
+ ,
|
||||
+ {
|
||||
+ "name": "envoy_metrics_service",
|
||||
+ "type": "STRICT_DNS",
|
||||
+ {{- if .envoy_metrics_service_tls }}
|
||||
+ "transport_socket": {{ .envoy_metrics_service_tls }},
|
||||
+ {{- end }}
|
||||
+ {{- if .envoy_metrics_service_tcp_keepalive }}
|
||||
+ "upstream_connection_options": {{ .envoy_metrics_service_tcp_keepalive }},
|
||||
+ {{- end }}
|
||||
+ "respect_dns_ttl": true,
|
||||
+ "dns_lookup_family": "{{ .dns_lookup_family }}",
|
||||
+ "connect_timeout": "1s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "typed_extension_protocol_options": {
|
||||
+ "envoy.extensions.upstreams.http.v3.HttpProtocolOptions": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.upstreams.http.v3.HttpProtocolOptions",
|
||||
+ "explicit_http_config": {
|
||||
+ "http2_protocol_options": {}
|
||||
+ }
|
||||
+ }
|
||||
+ },
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "envoy_metrics_service",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {{ .envoy_metrics_service_address }}
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+ {{ if .envoy_accesslog_service_address }}
|
||||
+ ,
|
||||
+ {
|
||||
+ "name": "envoy_accesslog_service",
|
||||
+ "type": "STRICT_DNS",
|
||||
+ {{- if .envoy_accesslog_service_tls }}
|
||||
+ "transport_socket": {{ .envoy_accesslog_service_tls }},
|
||||
+ {{- end }}
|
||||
+ {{- if .envoy_accesslog_service_tcp_keepalive }}
|
||||
+ "upstream_connection_options": {{ .envoy_accesslog_service_tcp_keepalive }},
|
||||
+ {{ end }}
|
||||
+ "respect_dns_ttl": true,
|
||||
+ "dns_lookup_family": "{{ .dns_lookup_family }}",
|
||||
+ "connect_timeout": "1s",
|
||||
+ "lb_policy": "ROUND_ROBIN",
|
||||
+ "typed_extension_protocol_options": {
|
||||
+ "envoy.extensions.upstreams.http.v3.HttpProtocolOptions": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.upstreams.http.v3.HttpProtocolOptions",
|
||||
+ "explicit_http_config": {
|
||||
+ "http2_protocol_options": {}
|
||||
+ }
|
||||
+ }
|
||||
+ },
|
||||
+ "load_assignment": {
|
||||
+ "cluster_name": "envoy_accesslog_service",
|
||||
+ "endpoints": [{
|
||||
+ "lb_endpoints": [{
|
||||
+ "endpoint": {
|
||||
+ "address":{
|
||||
+ "socket_address": {{ .envoy_accesslog_service_address }}
|
||||
+ }
|
||||
+ }
|
||||
+ }]
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+ ],
|
||||
+ "listeners":[
|
||||
+ {
|
||||
+ "address": {
|
||||
+ "socket_address": {
|
||||
+ "protocol": "TCP",
|
||||
+ "address": "{{ .wildcard }}",
|
||||
+ "port_value": {{ .envoy_prometheus_port }}
|
||||
+ }
|
||||
+ },
|
||||
+ "filter_chains": [
|
||||
+ {
|
||||
+ "filters": [
|
||||
+ {
|
||||
+ "name": "envoy.filters.network.http_connection_manager",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.filters.network.http_connection_manager.v3.HttpConnectionManager",
|
||||
+ "codec_type": "AUTO",
|
||||
+ "stat_prefix": "stats",
|
||||
+ "route_config": {
|
||||
+ "virtual_hosts": [
|
||||
+ {
|
||||
+ "name": "backend",
|
||||
+ "domains": [
|
||||
+ "*"
|
||||
+ ],
|
||||
+ "routes": [
|
||||
+ {
|
||||
+ "match": {
|
||||
+ "prefix": "/stats/prometheus"
|
||||
+ },
|
||||
+ "route": {
|
||||
+ "cluster": "prometheus_stats"
|
||||
+ }
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ ]
|
||||
+ },
|
||||
+ "http_filters": [{
|
||||
+ "name": "envoy.filters.http.router",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.filters.http.router.v3.Router"
|
||||
+ }
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ ]
|
||||
+ },
|
||||
+ {
|
||||
+ "address": {
|
||||
+ "socket_address": {
|
||||
+ "protocol": "TCP",
|
||||
+ "address": "{{ .wildcard }}",
|
||||
+ "port_value": {{ .envoy_status_port }}
|
||||
+ }
|
||||
+ },
|
||||
+ "filter_chains": [
|
||||
+ {
|
||||
+ "filters": [
|
||||
+ {
|
||||
+ "name": "envoy.filters.network.http_connection_manager",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.filters.network.http_connection_manager.v3.HttpConnectionManager",
|
||||
+ "codec_type": "AUTO",
|
||||
+ "stat_prefix": "agent",
|
||||
+ "route_config": {
|
||||
+ "virtual_hosts": [
|
||||
+ {
|
||||
+ "name": "backend",
|
||||
+ "domains": [
|
||||
+ "*"
|
||||
+ ],
|
||||
+ "routes": [
|
||||
+ {
|
||||
+ "match": {
|
||||
+ "prefix": "/healthz/ready"
|
||||
+ },
|
||||
+ "route": {
|
||||
+ "cluster": "agent"
|
||||
+ }
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ ]
|
||||
+ },
|
||||
+ "http_filters": [{
|
||||
+ "name": "envoy.filters.http.router",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.extensions.filters.http.router.v3.Router"
|
||||
+ }
|
||||
+ }]
|
||||
+ }
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ ]
|
||||
+ }
|
||||
+ {{- if .zipkin }}
|
||||
+ ,
|
||||
+ "tracing": {
|
||||
+ "http": {
|
||||
+ "name": "envoy.tracers.zipkin",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.trace.v3.ZipkinConfig",
|
||||
+ "collector_cluster": "zipkin",
|
||||
+ "collector_endpoint": "/api/v2/spans",
|
||||
+ "collector_endpoint_version": "HTTP_JSON",
|
||||
+ "trace_id_128bit": true,
|
||||
+ "shared_span_context": false
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{- else if .lightstep }}
|
||||
+ ,
|
||||
+ "tracing": {
|
||||
+ "http": {
|
||||
+ "name": "envoy.tracers.lightstep",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.trace.v3.LightstepConfig",
|
||||
+ "collector_cluster": "lightstep",
|
||||
+ "access_token_file": "{{ .lightstepToken}}"
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{- else if .datadog }}
|
||||
+ ,
|
||||
+ "tracing": {
|
||||
+ "http": {
|
||||
+ "name": "envoy.tracers.datadog",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.trace.v3.DatadogConfig",
|
||||
+ "collector_cluster": "datadog_agent",
|
||||
+ "service_name": "{{ .cluster }}"
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{- else if .openCensusAgent }}
|
||||
+ ,
|
||||
+ "tracing": {
|
||||
+ "http": {
|
||||
+ "name": "envoy.tracers.opencensus",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.trace.v3.OpenCensusConfig",
|
||||
+ "ocagent_exporter_enabled": true,
|
||||
+ "ocagent_address": "{{ .openCensusAgent }}",
|
||||
+ "incoming_trace_context": {{ .openCensusAgentContexts }},
|
||||
+ "outgoing_trace_context": {{ .openCensusAgentContexts }},
|
||||
+ "trace_config": {
|
||||
+ "constant_sampler": {
|
||||
+ "decision": "ALWAYS_PARENT"
|
||||
+ },
|
||||
+ "max_number_of_annotations": 200,
|
||||
+ "max_number_of_attributes": 200,
|
||||
+ "max_number_of_message_events": 200,
|
||||
+ "max_number_of_links": 200
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{- else if .stackdriver }}
|
||||
+ ,
|
||||
+ "tracing": {
|
||||
+ "http": {
|
||||
+ "name": "envoy.tracers.opencensus",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.trace.v3.OpenCensusConfig",
|
||||
+ "stackdriver_exporter_enabled": true,
|
||||
+ "stackdriver_project_id": "{{ .stackdriverProjectID }}",
|
||||
+ {{ if .sts_port }}
|
||||
+ "stackdriver_grpc_service": {
|
||||
+ "google_grpc": {
|
||||
+ "target_uri": "cloudtrace.googleapis.com",
|
||||
+ "stat_prefix": "oc_stackdriver_tracer",
|
||||
+ "channel_credentials": {
|
||||
+ "ssl_credentials": {}
|
||||
+ },
|
||||
+ "call_credentials": [{
|
||||
+ "sts_service": {
|
||||
+ "token_exchange_service_uri": "http://localhost:{{ .sts_port }}/token",
|
||||
+ "subject_token_path": "/var/run/secrets/tokens/istio-token",
|
||||
+ "subject_token_type": "urn:ietf:params:oauth:token-type:jwt",
|
||||
+ "scope": "https://www.googleapis.com/auth/cloud-platform"
|
||||
+ }
|
||||
+ }]
|
||||
+ },
|
||||
+ "initial_metadata": [
|
||||
+ {{ if .gcp_project_id }}
|
||||
+ {
|
||||
+ "key": "x-goog-user-project",
|
||||
+ "value": "{{ .gcp_project_id }}"
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+ ]
|
||||
+ },
|
||||
+ {{ end }}
|
||||
+ "stdout_exporter_enabled": {{ .stackdriverDebug }},
|
||||
+ "incoming_trace_context": ["CLOUD_TRACE_CONTEXT", "TRACE_CONTEXT", "GRPC_TRACE_BIN", "B3"],
|
||||
+ "outgoing_trace_context": ["CLOUD_TRACE_CONTEXT", "TRACE_CONTEXT", "GRPC_TRACE_BIN", "B3"],
|
||||
+ "trace_config":{
|
||||
+ "constant_sampler":{
|
||||
+ "decision": "ALWAYS_PARENT"
|
||||
+ },
|
||||
+ "max_number_of_annotations": {{ .stackdriverMaxAnnotations }},
|
||||
+ "max_number_of_attributes": {{ .stackdriverMaxAttributes }},
|
||||
+ "max_number_of_message_events": {{ .stackdriverMaxEvents }},
|
||||
+ "max_number_of_links": 200
|
||||
+ }
|
||||
+ }
|
||||
+ }}
|
||||
+ {{ end }}
|
||||
+ {{ if or .envoy_metrics_service_address .statsd }}
|
||||
+ ,
|
||||
+ "stats_sinks": [
|
||||
+ {{ if .envoy_metrics_service_address }}
|
||||
+ {
|
||||
+ "name": "envoy.stat_sinks.metrics_service",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.metrics.v3.MetricsServiceConfig",
|
||||
+ "transport_api_version": "V3",
|
||||
+ "grpc_service": {
|
||||
+ "envoy_grpc": {
|
||||
+ "cluster_name": "envoy_metrics_service"
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+ {{ if and .envoy_metrics_service_address .statsd }}
|
||||
+ ,
|
||||
+ {{ end }}
|
||||
+ {{ if .statsd }}
|
||||
+ {
|
||||
+ "name": "envoy.stat_sinks.statsd",
|
||||
+ "typed_config": {
|
||||
+ "@type": "type.googleapis.com/envoy.config.metrics.v3.StatsdSink",
|
||||
+ "address": {
|
||||
+ "socket_address": {{ .statsd }}
|
||||
+ }
|
||||
+ }
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+ ]
|
||||
+ {{ end }}
|
||||
+ {{ if .outlier_log_path }}
|
||||
+ ,
|
||||
+ "cluster_manager": {
|
||||
+ "outlier_detection": {
|
||||
+ "event_log_path": "{{ .outlier_log_path }}"
|
||||
+ }
|
||||
+ }
|
||||
+ {{ end }}
|
||||
+}
|
||||
diff -Naur istio/tools/packaging/common/higress-proxy-container-init.sh istio-new/tools/packaging/common/higress-proxy-container-init.sh
|
||||
--- istio/tools/packaging/common/higress-proxy-container-init.sh 1970-01-01 08:00:00.000000000 +0800
|
||||
+++ istio-new/tools/packaging/common/higress-proxy-container-init.sh 2024-05-19 16:30:06.202757394 +0800
|
||||
@@ -0,0 +1,32 @@
|
||||
+#!/bin/bash
|
||||
+
|
||||
+mkdir -p /var/log/proxy
|
||||
+
|
||||
+mkdir -p /var/lib/istio
|
||||
+
|
||||
+chown -R 1337.1337 /var/log/proxy
|
||||
+
|
||||
+chown -R 1337.1337 /var/lib/logrotate
|
||||
+
|
||||
+chown -R 1337.1337 /var/lib/istio
|
||||
+
|
||||
+cat <<EOF > /etc/logrotate.d/higress-logrotate
|
||||
+/var/log/proxy/access.log
|
||||
+{
|
||||
+su 1337 1337
|
||||
+rotate 5
|
||||
+create 644 1337 1337
|
||||
+nocompress
|
||||
+notifempty
|
||||
+minsize 100M
|
||||
+postrotate
|
||||
+ ps aux|grep "envoy -c"|grep -v "grep"|awk '{print $2}'|xargs -i kill -SIGUSR1 {}
|
||||
+endscript
|
||||
+}
|
||||
+EOF
|
||||
+
|
||||
+chmod -R 0644 /etc/logrotate.d/higress-logrotate
|
||||
+
|
||||
+cat <<EOF > /var/lib/istio/cron.txt
|
||||
+* * * * * /usr/sbin/logrotate /etc/logrotate.d/higress-logrotate
|
||||
+EOF
|
||||
diff -Naur istio/tools/packaging/common/higress-proxy-start.sh istio-new/tools/packaging/common/higress-proxy-start.sh
|
||||
--- istio/tools/packaging/common/higress-proxy-start.sh 1970-01-01 08:00:00.000000000 +0800
|
||||
+++ istio-new/tools/packaging/common/higress-proxy-start.sh 2024-05-19 16:33:18.802761176 +0800
|
||||
@@ -0,0 +1,10 @@
|
||||
+#!/bin/bash
|
||||
+
|
||||
+if [ -n "$LITE_METRICS" ]; then
|
||||
+ cp /var/lib/istio/envoy/envoy_bootstrap_lite_tmpl.json /var/lib/istio/envoy/envoy_bootstrap_tmpl.json
|
||||
+fi
|
||||
+
|
||||
+nohup supercronic /var/lib/istio/cron.txt &> /dev/null &
|
||||
+
|
||||
+/usr/local/bin/pilot-agent $*
|
||||
+
|
||||
83
istio/1.12/patches/istio/20240521-optimize-bootstrap.patch
Normal file
83
istio/1.12/patches/istio/20240521-optimize-bootstrap.patch
Normal file
@@ -0,0 +1,83 @@
|
||||
diff -Naur istio/tools/packaging/common/envoy_bootstrap.json istio-new/tools/packaging/common/envoy_bootstrap.json
|
||||
--- istio/tools/packaging/common/envoy_bootstrap.json 2024-05-21 23:46:21.000000000 +0800
|
||||
+++ istio-new/tools/packaging/common/envoy_bootstrap.json 2024-05-21 23:47:54.000000000 +0800
|
||||
@@ -37,55 +37,15 @@
|
||||
"use_all_default_tags": false,
|
||||
"stats_tags": [
|
||||
{
|
||||
- "tag_name": "phase",
|
||||
- "regex": "(_phase=([a-z_]+))"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "ruleid",
|
||||
- "regex": "(_ruleid=([0-9]+))"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "route",
|
||||
- "regex": "^vhost\\..*?\\.route\\.([^\\.]+\\.)upstream"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "ecds_name",
|
||||
- "regex": "extension_config_discovery\\.(.*?\\.)[^\\.]+$"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "rds_name",
|
||||
- "regex": "rds\\.(.*?\\.)[^\\.]+$"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "sds_name",
|
||||
- "regex": "sds\\.(.*?\\.)[^\\.]+$"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "vhost",
|
||||
- "regex": "^vhost\\.((.*?)\\.)(vcluster|route)"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "vcluster",
|
||||
- "regex": "vcluster\\.((.*?)\\.)upstream"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "dest_zone",
|
||||
- "regex": "zone\\.[^\\.]+\\.([^\\.]+\\.)"
|
||||
- },
|
||||
- {
|
||||
- "tag_name": "from_zone",
|
||||
- "regex": "zone\\.([^\\.]+\\.)"
|
||||
- },
|
||||
- {
|
||||
"tag_name": "cluster_name",
|
||||
- "regex": "^cluster\\.((.*?)\\.)(http1\\.|http2\\.|health_check\\.|zone\\.|external\\.|circuit_breakers\\.|[^\\.]+$)"
|
||||
+ "regex": "^cluster\\.((.+?(\\..+?\\.svc\\.cluster\\.local)?)\\.)"
|
||||
},
|
||||
{
|
||||
"tag_name": "tcp_prefix",
|
||||
"regex": "^tcp\\.((.*?)\\.)\\w+?$"
|
||||
},
|
||||
{
|
||||
- "regex": "(response_code=\\.=(.+?);\\.;)|_rq(_(\\.d{3}))$",
|
||||
+ "regex": "_rq(_(\\d{3}))$",
|
||||
"tag_name": "response_code"
|
||||
},
|
||||
{
|
||||
@@ -98,7 +58,7 @@
|
||||
},
|
||||
{
|
||||
"tag_name": "http_conn_manager_prefix",
|
||||
- "regex": "^http\\.(((outbound_([0-9]{1,3}\\.{0,1}){4}_\\d{0,5})|([^\\.]+))\\.)"
|
||||
+ "regex": "^http\\.(((?:[_.[:digit:]]*|[_\\[\\]aAbBcCdDeEfF[:digit:]]*))\\.)"
|
||||
},
|
||||
{
|
||||
"tag_name": "listener_address",
|
||||
@@ -108,12 +68,6 @@
|
||||
"tag_name": "mongo_prefix",
|
||||
"regex": "^mongo\\.(.+?)\\.(collection|cmd|cx_|op_|delays_|decoding_)(.*?)$"
|
||||
},
|
||||
- {{- range $a, $tag := .extraStatTags }}
|
||||
- {
|
||||
- "regex": "({{ $tag }}=\\.=(.*?);\\.;)",
|
||||
- "tag_name": "{{ $tag }}"
|
||||
- },
|
||||
- {{- end }}
|
||||
{
|
||||
"regex": "(cache\\.(.+?)\\.)",
|
||||
"tag_name": "cache"
|
||||
69
istio/1.12/patches/istio/20240527-fix-vs-merge.patch
Normal file
69
istio/1.12/patches/istio/20240527-fix-vs-merge.patch
Normal file
@@ -0,0 +1,69 @@
|
||||
diff -Naur istio/pilot/pkg/model/push_context.go istio-new/pilot/pkg/model/push_context.go
|
||||
--- istio/pilot/pkg/model/push_context.go 2024-05-27 23:03:09.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/model/push_context.go 2024-05-27 21:33:45.000000000 +0800
|
||||
@@ -1482,8 +1482,14 @@
|
||||
ns := virtualService.Namespace
|
||||
rule := virtualService.Spec.(*networking.VirtualService)
|
||||
// Added by ingress
|
||||
- for _, host := range rule.Hosts {
|
||||
- ps.virtualServiceIndex.byHost[host] = append(ps.virtualServiceIndex.byHost[host], virtualService)
|
||||
+ if len(rule.Gateways) > 0 {
|
||||
+ if len(rule.Hosts) == 0 {
|
||||
+ ps.virtualServiceIndex.byHost[constants.GlobalWildcardHost] = append(ps.virtualServiceIndex.byHost[constants.GlobalWildcardHost], virtualService)
|
||||
+ } else {
|
||||
+ for _, host := range rule.Hosts {
|
||||
+ ps.virtualServiceIndex.byHost[host] = append(ps.virtualServiceIndex.byHost[host], virtualService)
|
||||
+ }
|
||||
+ }
|
||||
}
|
||||
// End added by ingress
|
||||
gwNames := getGatewayNames(rule)
|
||||
diff -Naur istio/pilot/pkg/networking/core/v1alpha3/gateway.go istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go
|
||||
--- istio/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-05-27 23:03:09.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/networking/core/v1alpha3/gateway.go 2024-05-27 22:58:33.000000000 +0800
|
||||
@@ -376,8 +376,15 @@
|
||||
gatewayVirtualServices[gatewayName] = virtualServices
|
||||
}
|
||||
for _, virtualService := range virtualServices {
|
||||
- for _, host := range virtualService.Spec.(*networking.VirtualService).Hosts {
|
||||
- hostSet.Insert(host)
|
||||
+ rule := virtualService.Spec.(*networking.VirtualService)
|
||||
+ if len(rule.Gateways) > 0 {
|
||||
+ if len(rule.Hosts) == 0 {
|
||||
+ hostSet.Insert(constants.GlobalWildcardHost)
|
||||
+ break
|
||||
+ }
|
||||
+ for _, host := range rule.Hosts {
|
||||
+ hostSet.Insert(host)
|
||||
+ }
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -689,7 +696,7 @@
|
||||
vHost = &route.VirtualHost{
|
||||
Name: util.DomainName(hostRDSHost, port),
|
||||
Domains: buildGatewayVirtualHostDomains(hostRDSHost, port),
|
||||
- Routes: routes,
|
||||
+ Routes: append(routes[:0:0], routes...),
|
||||
IncludeRequestAttemptCount: true,
|
||||
TypedPerFilterConfig: mseingress.ConstructTypedPerFilterConfigForVHost(globalHTTPFilters, virtualService),
|
||||
}
|
||||
@@ -884,7 +891,7 @@
|
||||
newVHost := &route.VirtualHost{
|
||||
Name: util.DomainName(string(hostname), port),
|
||||
Domains: buildGatewayVirtualHostDomains(string(hostname), port),
|
||||
- Routes: routes,
|
||||
+ Routes: append(routes[:0:0], routes...),
|
||||
IncludeRequestAttemptCount: true,
|
||||
TypedPerFilterConfig: mseingress.ConstructTypedPerFilterConfigForVHost(globalHTTPFilters, virtualService),
|
||||
}
|
||||
diff -Naur istio/pkg/config/constants/constants.go istio-new/pkg/config/constants/constants.go
|
||||
--- istio/pkg/config/constants/constants.go 2024-05-27 23:03:09.000000000 +0800
|
||||
+++ istio-new/pkg/config/constants/constants.go 2024-05-27 21:31:58.000000000 +0800
|
||||
@@ -145,5 +145,6 @@
|
||||
// Added by ingress
|
||||
HigressHostRDSNamePrefix = "higress-rds-"
|
||||
DefaultScopedRouteName = "scoped-route"
|
||||
+ GlobalWildcardHost = "*"
|
||||
// End added by ingress
|
||||
)
|
||||
17
istio/1.12/patches/istio/20240529-optimize-mcp-cds.patch
Normal file
17
istio/1.12/patches/istio/20240529-optimize-mcp-cds.patch
Normal file
@@ -0,0 +1,17 @@
|
||||
diff -Naur istio/pilot/pkg/model/push_context.go istio-new/pilot/pkg/model/push_context.go
|
||||
--- istio/pilot/pkg/model/push_context.go 2024-05-29 19:29:45.000000000 +0800
|
||||
+++ istio-new/pilot/pkg/model/push_context.go 2024-05-29 19:11:03.000000000 +0800
|
||||
@@ -769,6 +769,13 @@
|
||||
for _, s := range svcs {
|
||||
svcHost := string(s.Hostname)
|
||||
|
||||
+ // Added by ingress
|
||||
+ if s.Attributes.Namespace == "mcp" {
|
||||
+ gwSvcs = append(gwSvcs, s)
|
||||
+ continue
|
||||
+ }
|
||||
+ // End added by ingress
|
||||
+
|
||||
if _, ok := hostsFromGateways[svcHost]; ok {
|
||||
gwSvcs = append(gwSvcs, s)
|
||||
}
|
||||
38
istio/1.12/patches/proxy/20240519-v8-upgrade.patch
Normal file
38
istio/1.12/patches/proxy/20240519-v8-upgrade.patch
Normal file
@@ -0,0 +1,38 @@
|
||||
diff -Naur proxy/scripts/release-binary.sh proxy-new/scripts/release-binary.sh
|
||||
--- proxy/scripts/release-binary.sh 2024-05-19 12:33:33.254478650 +0800
|
||||
+++ proxy-new/scripts/release-binary.sh 2024-05-19 12:31:11.714475870 +0800
|
||||
@@ -112,7 +112,7 @@
|
||||
# k8-opt is the output directory for x86_64 optimized builds (-c opt, so --config=release-symbol and --config=release).
|
||||
# k8-dbg is the output directory for -c dbg builds.
|
||||
#for config in release release-symbol debug
|
||||
-for config in release
|
||||
+for config in release release-symbol
|
||||
do
|
||||
case $config in
|
||||
"release" )
|
||||
diff -Naur proxy/scripts/release-binary.sh proxy-new/scripts/release-binary.sh
|
||||
--- proxy/scripts/release-binary.sh 2024-05-19 12:27:51.030471929 +0800
|
||||
+++ proxy-new/scripts/release-binary.sh 2024-05-19 12:04:55.738444918 +0800
|
||||
@@ -152,10 +152,6 @@
|
||||
echo "Building ${config} proxy"
|
||||
BINARY_NAME="${HOME}/package/${BINARY_BASE_NAME}.tar.gz"
|
||||
SHA256_NAME="${HOME}/${BINARY_BASE_NAME}-${SHA}.sha256"
|
||||
- # All cores are used by com_googlesource_chromium_v8:build within.
|
||||
- # Prebuild this target to avoid stacking this ram intensive task with others.
|
||||
- # shellcheck disable=SC2086
|
||||
- bazel build ${BAZEL_BUILD_ARGS} ${CONFIG_PARAMS} @com_googlesource_chromium_v8//:build
|
||||
# shellcheck disable=SC2086
|
||||
bazel build ${BAZEL_BUILD_ARGS} ${CONFIG_PARAMS} //src/envoy:envoy_tar
|
||||
BAZEL_TARGET="${BAZEL_OUT}/src/envoy/envoy_tar.tar.gz"
|
||||
diff -Naur proxy/tools/deb/test/build_docker.sh proxy-new/tools/deb/test/build_docker.sh
|
||||
--- proxy/tools/deb/test/build_docker.sh 2024-05-19 12:27:51.030471929 +0800
|
||||
+++ proxy-new/tools/deb/test/build_docker.sh 2024-05-19 12:05:07.978445159 +0800
|
||||
@@ -20,8 +20,6 @@
|
||||
# Script requires a working docker on the test machine
|
||||
# It is run in the proxy dir, will create a docker image with proxy deb installed
|
||||
|
||||
-
|
||||
-bazel build @com_googlesource_chromium_v8//:build
|
||||
bazel build tools/deb:istio-proxy
|
||||
|
||||
PROJECT="istio-testing"
|
||||
@@ -20,6 +20,7 @@ import (
|
||||
"net/http"
|
||||
"time"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cert"
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/common"
|
||||
"github.com/alibaba/higress/pkg/ingress/mcp"
|
||||
"github.com/alibaba/higress/pkg/ingress/translation"
|
||||
@@ -110,6 +111,11 @@ type ServerArgs struct {
|
||||
KeepStaleWhenEmpty bool
|
||||
GatewaySelectorKey string
|
||||
GatewaySelectorValue string
|
||||
GatewayHttpPort uint32
|
||||
GatewayHttpsPort uint32
|
||||
EnableAutomaticHttps bool
|
||||
AutomaticHttpsEmail string
|
||||
CertHttpAddress string
|
||||
}
|
||||
|
||||
type readinessProbe func() (bool, error)
|
||||
@@ -131,6 +137,7 @@ type Server struct {
|
||||
xdsServer *xds.DiscoveryServer
|
||||
server server.Instance
|
||||
readinessProbes map[string]readinessProbe
|
||||
certServer *cert.Server
|
||||
}
|
||||
|
||||
var (
|
||||
@@ -166,6 +173,7 @@ func NewServer(args *ServerArgs) (*Server, error) {
|
||||
s.initConfigController,
|
||||
s.initRegistryEventHandlers,
|
||||
s.initAuthenticators,
|
||||
s.initAutomaticHttps,
|
||||
}
|
||||
|
||||
for _, f := range initFuncList {
|
||||
@@ -220,6 +228,8 @@ func (s *Server) initConfigController() error {
|
||||
SystemNamespace: ns,
|
||||
GatewaySelectorKey: s.GatewaySelectorKey,
|
||||
GatewaySelectorValue: s.GatewaySelectorValue,
|
||||
GatewayHttpPort: s.GatewayHttpPort,
|
||||
GatewayHttpsPort: s.GatewayHttpsPort,
|
||||
}
|
||||
if options.ClusterId == "Kubernetes" {
|
||||
options.ClusterId = ""
|
||||
@@ -283,6 +293,15 @@ func (s *Server) Start(stop <-chan struct{}) error {
|
||||
}
|
||||
}()
|
||||
|
||||
if s.EnableAutomaticHttps {
|
||||
go func() {
|
||||
log.Infof("starting Automatic Cert HTTP service at %s", s.CertHttpAddress)
|
||||
if err := s.certServer.Run(stop); err != nil {
|
||||
log.Errorf("error serving Automatic Cert HTTP server: %v", err)
|
||||
}
|
||||
}()
|
||||
}
|
||||
|
||||
s.waitForShutDown(stop)
|
||||
return nil
|
||||
}
|
||||
@@ -366,6 +385,26 @@ func (s *Server) initAuthenticators() error {
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *Server) initAutomaticHttps() error {
|
||||
certOption := &cert.Option{
|
||||
Namespace: PodNamespace,
|
||||
ServerAddress: s.CertHttpAddress,
|
||||
Email: s.AutomaticHttpsEmail,
|
||||
}
|
||||
certServer, err := cert.NewServer(s.kubeClient.Kube(), certOption)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
s.certServer = certServer
|
||||
log.Infof("init cert default config")
|
||||
s.certServer.InitDefaultConfig()
|
||||
if !s.EnableAutomaticHttps {
|
||||
log.Info("automatic https is disabled")
|
||||
return nil
|
||||
}
|
||||
return s.certServer.InitServer()
|
||||
}
|
||||
|
||||
func (s *Server) initKubeClient() error {
|
||||
if s.kubeClient != nil {
|
||||
// Already initialized by startup arguments
|
||||
@@ -394,6 +433,7 @@ func (s *Server) initHttpServer() error {
|
||||
}
|
||||
s.xdsServer.AddDebugHandlers(s.httpMux, nil, true, nil)
|
||||
s.httpMux.HandleFunc("/ready", s.readyHandler)
|
||||
s.httpMux.HandleFunc("/registry/watcherStatus", s.registryWatcherStatusHandler)
|
||||
return nil
|
||||
}
|
||||
|
||||
@@ -409,6 +449,43 @@ func (s *Server) readyHandler(w http.ResponseWriter, _ *http.Request) {
|
||||
w.WriteHeader(http.StatusOK)
|
||||
}
|
||||
|
||||
func (s *Server) registryWatcherStatusHandler(w http.ResponseWriter, _ *http.Request) {
|
||||
ingressTranslation, ok := s.environment.IngressStore.(*translation.IngressTranslation)
|
||||
if !ok {
|
||||
http.Error(w, "IngressStore not found", http.StatusNotFound)
|
||||
return
|
||||
}
|
||||
|
||||
ingressConfig := ingressTranslation.GetIngressConfig()
|
||||
if ingressConfig == nil {
|
||||
http.Error(w, "IngressConfig not found", http.StatusNotFound)
|
||||
return
|
||||
}
|
||||
|
||||
registryReconciler := ingressConfig.RegistryReconciler
|
||||
if registryReconciler == nil {
|
||||
http.Error(w, "RegistryReconciler not found", http.StatusNotFound)
|
||||
return
|
||||
}
|
||||
|
||||
watcherStatusList := registryReconciler.GetRegistryWatcherStatusList()
|
||||
writeJSON(w, watcherStatusList)
|
||||
}
|
||||
|
||||
func writeJSON(w http.ResponseWriter, obj interface{}) {
|
||||
w.Header().Set("Content-Type", "application/json")
|
||||
b, err := config.ToJSON(obj)
|
||||
if err != nil {
|
||||
w.WriteHeader(http.StatusInternalServerError)
|
||||
_, _ = w.Write([]byte(err.Error()))
|
||||
return
|
||||
}
|
||||
_, err = w.Write(b)
|
||||
if err != nil {
|
||||
w.WriteHeader(http.StatusInternalServerError)
|
||||
}
|
||||
}
|
||||
|
||||
// cachesSynced checks whether caches have been synced.
|
||||
func (s *Server) cachesSynced() bool {
|
||||
return s.configController.HasSynced()
|
||||
|
||||
219
pkg/cert/certmgr.go
Normal file
219
pkg/cert/certmgr.go
Normal file
@@ -0,0 +1,219 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"sync"
|
||||
|
||||
"github.com/caddyserver/certmagic"
|
||||
"github.com/mholt/acmez"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
)
|
||||
|
||||
const (
|
||||
EventCertObtained = "cert_obtained"
|
||||
)
|
||||
|
||||
type CertMgr struct {
|
||||
cfg *certmagic.Config
|
||||
client kubernetes.Interface
|
||||
namespace string
|
||||
mux sync.RWMutex
|
||||
storage certmagic.Storage
|
||||
cache *certmagic.Cache
|
||||
myACME *certmagic.ACMEIssuer
|
||||
ingressSolver acmez.Solver
|
||||
configMgr *ConfigMgr
|
||||
secretMgr *SecretMgr
|
||||
}
|
||||
|
||||
func InitCertMgr(opts *Option, clientSet kubernetes.Interface, config *Config) (*CertMgr, error) {
|
||||
CertLog.Infof("certmgr init config: %+v", config)
|
||||
// Init certmagic config
|
||||
// First make a pointer to a Cache as we need to reference the same Cache in
|
||||
// GetConfigForCert below.
|
||||
var cache *certmagic.Cache
|
||||
var storage certmagic.Storage
|
||||
storage, _ = NewConfigmapStorage(opts.Namespace, clientSet)
|
||||
renewalWindowRatio := float64(config.RenewBeforeDays / RenewMaxDays)
|
||||
magicConfig := certmagic.Config{
|
||||
RenewalWindowRatio: renewalWindowRatio,
|
||||
Storage: storage,
|
||||
}
|
||||
cache = certmagic.NewCache(certmagic.CacheOptions{
|
||||
GetConfigForCert: func(cert certmagic.Certificate) (*certmagic.Config, error) {
|
||||
// Here we use New to get a valid Config associated with the same cache.
|
||||
// The provided Config is used as a template and will be completed with
|
||||
// any defaults that are set in the Default config.
|
||||
return certmagic.New(cache, magicConfig), nil
|
||||
},
|
||||
})
|
||||
// init certmagic
|
||||
cfg := certmagic.New(cache, magicConfig)
|
||||
// Init certmagic acme
|
||||
issuer := config.GetIssuer(IssuerTypeLetsencrypt)
|
||||
if issuer == nil {
|
||||
// should never happen here
|
||||
return nil, fmt.Errorf("there is no Letsencrypt Issuer found in config")
|
||||
}
|
||||
|
||||
myACME := certmagic.NewACMEIssuer(cfg, certmagic.ACMEIssuer{
|
||||
//CA: certmagic.LetsEncryptStagingCA,
|
||||
CA: certmagic.LetsEncryptProductionCA,
|
||||
Email: issuer.Email,
|
||||
Agreed: true,
|
||||
DisableHTTPChallenge: false,
|
||||
DisableTLSALPNChallenge: true,
|
||||
})
|
||||
// inject http01 solver
|
||||
ingressSolver, _ := NewIngressSolver(opts.Namespace, clientSet, myACME)
|
||||
myACME.Http01Solver = ingressSolver
|
||||
// init issuers
|
||||
cfg.Issuers = []certmagic.Issuer{myACME}
|
||||
|
||||
configMgr, _ := NewConfigMgr(opts.Namespace, clientSet)
|
||||
secretMgr, _ := NewSecretMgr(opts.Namespace, clientSet)
|
||||
|
||||
certMgr := &CertMgr{
|
||||
cfg: cfg,
|
||||
client: clientSet,
|
||||
namespace: opts.Namespace,
|
||||
myACME: myACME,
|
||||
ingressSolver: ingressSolver,
|
||||
configMgr: configMgr,
|
||||
secretMgr: secretMgr,
|
||||
cache: cache,
|
||||
}
|
||||
certMgr.cfg.OnEvent = certMgr.OnEvent
|
||||
return certMgr, nil
|
||||
}
|
||||
func (s *CertMgr) Reconcile(ctx context.Context, oldConfig *Config, newConfig *Config) error {
|
||||
CertLog.Infof("cermgr reconcile old config:%+v to new config:%+v", oldConfig, newConfig)
|
||||
// sync email
|
||||
if oldConfig != nil && newConfig != nil {
|
||||
oldIssuer := oldConfig.GetIssuer(IssuerTypeLetsencrypt)
|
||||
newIssuer := newConfig.GetIssuer(IssuerTypeLetsencrypt)
|
||||
if oldIssuer.Email != newIssuer.Email {
|
||||
// TODO before sync email, maybe need to clean up cache and account
|
||||
}
|
||||
}
|
||||
|
||||
// sync domains
|
||||
newDomains := make([]string, 0)
|
||||
newDomainsMap := make(map[string]string, 0)
|
||||
removeDomains := make([]string, 0)
|
||||
|
||||
if newConfig != nil {
|
||||
for _, config := range newConfig.CredentialConfig {
|
||||
if config.TLSIssuer == IssuerTypeLetsencrypt {
|
||||
for _, newDomain := range config.Domains {
|
||||
newDomains = append(newDomains, newDomain)
|
||||
newDomainsMap[newDomain] = newDomain
|
||||
}
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if oldConfig != nil {
|
||||
for _, config := range oldConfig.CredentialConfig {
|
||||
if config.TLSIssuer == IssuerTypeLetsencrypt {
|
||||
for _, oldDomain := range config.Domains {
|
||||
if _, ok := newDomainsMap[oldDomain]; !ok {
|
||||
removeDomains = append(removeDomains, oldDomain)
|
||||
}
|
||||
}
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if newConfig.AutomaticHttps == true {
|
||||
newIssuer := newConfig.GetIssuer(IssuerTypeLetsencrypt)
|
||||
// clean up unused domains
|
||||
s.cleanSync(context.Background(), removeDomains)
|
||||
// sync email
|
||||
s.myACME.Email = newIssuer.Email
|
||||
// sync RenewalWindowRatio
|
||||
s.cfg.RenewalWindowRatio = float64(newConfig.RenewBeforeDays / RenewMaxDays)
|
||||
// start cache
|
||||
s.cache.Start()
|
||||
// sync domains
|
||||
s.manageSync(context.Background(), newDomains)
|
||||
s.configMgr.SetConfig(newConfig)
|
||||
} else {
|
||||
// stop cache maintainAssets
|
||||
s.cache.Stop()
|
||||
s.configMgr.SetConfig(newConfig)
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *CertMgr) manageSync(ctx context.Context, domainNames []string) error {
|
||||
CertLog.Infof("cert manage sync domains:%v", domainNames)
|
||||
return s.cfg.ManageSync(ctx, domainNames)
|
||||
}
|
||||
|
||||
func (s *CertMgr) cleanSync(ctx context.Context, domainNames []string) error {
|
||||
//TODO implement clean up domains
|
||||
CertLog.Infof("cert clean sync domains:%v", domainNames)
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *CertMgr) OnEvent(ctx context.Context, event string, data map[string]any) error {
|
||||
CertLog.Infof("certmgr receive event:% data:%+v", event, data)
|
||||
/**
|
||||
event: cert_obtained
|
||||
cfg.emit(ctx, "cert_obtained", map[string]any{
|
||||
"renewal": true,
|
||||
"remaining": timeLeft,
|
||||
"identifier": name,
|
||||
"issuer": issuerKey,
|
||||
"storage_path": StorageKeys.CertsSitePrefix(issuerKey, certKey),
|
||||
"private_key_path": StorageKeys.SitePrivateKey(issuerKey, certKey),
|
||||
"certificate_path": StorageKeys.SiteCert(issuerKey, certKey),
|
||||
"metadata_path": StorageKeys.SiteMeta(issuerKey, certKey),
|
||||
})
|
||||
*/
|
||||
if event == EventCertObtained {
|
||||
// obtain certificate and update secret
|
||||
domain := data["identifier"].(string)
|
||||
isRenew := data["renewal"].(bool)
|
||||
privateKeyPath := data["private_key_path"].(string)
|
||||
certificatePath := data["certificate_path"].(string)
|
||||
privateKey, err := s.cfg.Storage.Load(context.Background(), privateKeyPath)
|
||||
certificate, err := s.cfg.Storage.Load(context.Background(), certificatePath)
|
||||
certChain, err := parseCertsFromPEMBundle(certificate)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
notAfterTime := notAfter(certChain[0])
|
||||
notBeforeTime := notBefore(certChain[0])
|
||||
secretName := s.configMgr.GetConfig().GetSecretNameByDomain(IssuerTypeLetsencrypt, domain)
|
||||
if len(secretName) == 0 {
|
||||
CertLog.Errorf("can not find secret name for domain % in config", domain)
|
||||
return nil
|
||||
}
|
||||
err2 := s.secretMgr.Update(domain, secretName, privateKey, certificate, notBeforeTime, notAfterTime, isRenew)
|
||||
if err2 != nil {
|
||||
CertLog.Errorf("update secretName %s for domain %s error: %v", secretName, domain, err2)
|
||||
}
|
||||
return err
|
||||
}
|
||||
return nil
|
||||
}
|
||||
292
pkg/cert/config.go
Normal file
292
pkg/cert/config.go
Normal file
@@ -0,0 +1,292 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"strings"
|
||||
"sync/atomic"
|
||||
"time"
|
||||
|
||||
"istio.io/istio/pkg/config/host"
|
||||
v1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
"sigs.k8s.io/yaml"
|
||||
)
|
||||
|
||||
const (
|
||||
ConfigmapCertName = "higress-https"
|
||||
ConfigmapCertConfigKey = "cert"
|
||||
DefaultRenewBeforeDays = 30
|
||||
RenewMaxDays = 90
|
||||
)
|
||||
|
||||
type IssuerName string
|
||||
|
||||
const (
|
||||
IssuerTypeAliyunSSL IssuerName = "aliyunssl"
|
||||
IssuerTypeLetsencrypt IssuerName = "letsencrypt"
|
||||
)
|
||||
|
||||
// Config is the configuration of automatic https.
|
||||
type Config struct {
|
||||
AutomaticHttps bool `json:"automaticHttps"`
|
||||
FallbackForInvalidSecret bool `json:"fallbackForInvalidSecret"`
|
||||
RenewBeforeDays int `json:"renewBeforeDays"`
|
||||
CredentialConfig []CredentialEntry `json:"credentialConfig"`
|
||||
ACMEIssuer []ACMEIssuerEntry `json:"acmeIssuer"`
|
||||
Version string `json:"version"`
|
||||
}
|
||||
|
||||
func (c *Config) GetIssuer(issuerName IssuerName) *ACMEIssuerEntry {
|
||||
for _, issuer := range c.ACMEIssuer {
|
||||
if issuer.Name == issuerName {
|
||||
return &issuer
|
||||
}
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (c *Config) MatchSecretNameByDomain(domain string) string {
|
||||
for _, credential := range c.CredentialConfig {
|
||||
for _, credDomain := range credential.Domains {
|
||||
if host.Name(strings.ToLower(domain)).SubsetOf(host.Name(strings.ToLower(credDomain))) {
|
||||
return credential.TLSSecret
|
||||
}
|
||||
}
|
||||
}
|
||||
return ""
|
||||
}
|
||||
|
||||
func (c *Config) GetSecretNameByDomain(issuerName IssuerName, domain string) string {
|
||||
for _, credential := range c.CredentialConfig {
|
||||
if credential.TLSIssuer == issuerName {
|
||||
for _, credDomain := range credential.Domains {
|
||||
if host.Name(strings.ToLower(domain)).SubsetOf(host.Name(strings.ToLower(credDomain))) {
|
||||
return credential.TLSSecret
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
return ""
|
||||
}
|
||||
|
||||
func (c *Config) Validate() error {
|
||||
// check acmeIssuer
|
||||
if len(c.ACMEIssuer) == 0 {
|
||||
return fmt.Errorf("acmeIssuer is empty")
|
||||
}
|
||||
for _, issuer := range c.ACMEIssuer {
|
||||
switch issuer.Name {
|
||||
case IssuerTypeLetsencrypt:
|
||||
if issuer.Email == "" {
|
||||
return fmt.Errorf("acmeIssuer %s email is empty", issuer.Name)
|
||||
}
|
||||
if !ValidateEmail(issuer.Email) {
|
||||
return fmt.Errorf("acmeIssuer %s email %s is invalid", issuer.Name, issuer.Email)
|
||||
}
|
||||
default:
|
||||
return fmt.Errorf("acmeIssuer name %s is not supported", issuer.Name)
|
||||
}
|
||||
}
|
||||
// check credentialConfig
|
||||
for _, credential := range c.CredentialConfig {
|
||||
if len(credential.Domains) == 0 {
|
||||
return fmt.Errorf("credentialConfig domains is empty")
|
||||
}
|
||||
if credential.TLSSecret == "" {
|
||||
return fmt.Errorf("credentialConfig tlsSecret is empty")
|
||||
}
|
||||
if credential.TLSIssuer == IssuerTypeLetsencrypt {
|
||||
if len(credential.Domains) > 1 {
|
||||
return fmt.Errorf("credentialConfig tlsIssuer %s only support one domain", credential.TLSIssuer)
|
||||
}
|
||||
}
|
||||
if credential.TLSIssuer != IssuerTypeLetsencrypt && len(credential.TLSIssuer) > 0 {
|
||||
return fmt.Errorf("credential tls issuer %s is not support", credential.TLSIssuer)
|
||||
}
|
||||
}
|
||||
|
||||
if c.RenewBeforeDays <= 0 {
|
||||
return fmt.Errorf("RenewBeforeDays should be large than zero")
|
||||
}
|
||||
|
||||
if c.RenewBeforeDays >= RenewMaxDays {
|
||||
return fmt.Errorf("RenewBeforeDays should be less than %d", RenewMaxDays)
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
type CredentialEntry struct {
|
||||
Domains []string `json:"domains"`
|
||||
TLSIssuer IssuerName `json:"tlsIssuer,omitempty"`
|
||||
TLSSecret string `json:"tlsSecret,omitempty"`
|
||||
CACertSecret string `json:"cacertSecret,omitempty"`
|
||||
}
|
||||
|
||||
type ACMEIssuerEntry struct {
|
||||
Name IssuerName `json:"name"`
|
||||
Email string `json:"email"`
|
||||
AK string `json:"ak"` // Only applicable for certain issuers like 'aliyunssl'
|
||||
SK string `json:"sk"` // Only applicable for certain issuers like 'aliyunssl'
|
||||
}
|
||||
type ConfigMgr struct {
|
||||
client kubernetes.Interface
|
||||
config atomic.Value
|
||||
namespace string
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) SetConfig(config *Config) {
|
||||
c.config.Store(config)
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) GetConfig() *Config {
|
||||
value := c.config.Load()
|
||||
if value != nil {
|
||||
if config, ok := value.(*Config); ok {
|
||||
return config
|
||||
}
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) InitConfig(email string) (*Config, error) {
|
||||
var defaultConfig *Config
|
||||
cm, err := c.GetConfigmap()
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if len(strings.TrimSpace(email)) == 0 {
|
||||
email = getRandEmail()
|
||||
}
|
||||
defaultConfig = newDefaultConfig(email)
|
||||
err2 := c.ApplyConfigmap(defaultConfig)
|
||||
if err2 != nil {
|
||||
return nil, err2
|
||||
}
|
||||
}
|
||||
return nil, err
|
||||
} else {
|
||||
defaultConfig, err = c.ParseConfigFromConfigmap(cm)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
}
|
||||
return defaultConfig, nil
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) ParseConfigFromConfigmap(configmap *v1.ConfigMap) (*Config, error) {
|
||||
if _, ok := configmap.Data[ConfigmapCertConfigKey]; !ok {
|
||||
return nil, fmt.Errorf("no cert key %s in configmap %s", ConfigmapCertConfigKey, configmap.Name)
|
||||
}
|
||||
|
||||
config := newDefaultConfig("")
|
||||
if err := yaml.Unmarshal([]byte(configmap.Data[ConfigmapCertConfigKey]), config); err != nil {
|
||||
return nil, fmt.Errorf("data:%s, convert to higress config error, error: %+v", configmap.Data[ConfigmapCertConfigKey], err)
|
||||
}
|
||||
// validate config
|
||||
if err := config.Validate(); err != nil {
|
||||
return nil, err
|
||||
}
|
||||
return config, nil
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) GetConfigFromConfigmap() (*Config, error) {
|
||||
var config *Config
|
||||
cm, err := c.GetConfigmap()
|
||||
if err != nil {
|
||||
return nil, err
|
||||
} else {
|
||||
config, err = c.ParseConfigFromConfigmap(cm)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
}
|
||||
return config, nil
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) GetConfigmap() (configmap *v1.ConfigMap, err error) {
|
||||
configmapName := ConfigmapCertName
|
||||
cm, err := c.client.CoreV1().ConfigMaps(c.namespace).Get(context.Background(), configmapName, metav1.GetOptions{})
|
||||
return cm, err
|
||||
}
|
||||
|
||||
func (c *ConfigMgr) ApplyConfigmap(config *Config) error {
|
||||
configmapName := ConfigmapCertName
|
||||
cm := &v1.ConfigMap{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Namespace: c.namespace,
|
||||
Name: configmapName,
|
||||
},
|
||||
}
|
||||
bytes, err := yaml.Marshal(config)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
cm.Data = make(map[string]string, 0)
|
||||
cm.Data[ConfigmapCertConfigKey] = string(bytes)
|
||||
|
||||
_, err = c.client.CoreV1().ConfigMaps(c.namespace).Get(context.Background(), configmapName, metav1.GetOptions{})
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
if _, err = c.client.CoreV1().ConfigMaps(c.namespace).Create(context.Background(), cm, metav1.CreateOptions{}); err != nil {
|
||||
return err
|
||||
}
|
||||
} else {
|
||||
return err
|
||||
}
|
||||
} else {
|
||||
if _, err = c.client.CoreV1().ConfigMaps(c.namespace).Update(context.Background(), cm, metav1.UpdateOptions{}); err != nil {
|
||||
return err
|
||||
}
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func NewConfigMgr(namespace string, client kubernetes.Interface) (*ConfigMgr, error) {
|
||||
configMgr := &ConfigMgr{
|
||||
client: client,
|
||||
namespace: namespace,
|
||||
}
|
||||
return configMgr, nil
|
||||
}
|
||||
|
||||
func newDefaultConfig(email string) *Config {
|
||||
|
||||
defaultIssuer := []ACMEIssuerEntry{
|
||||
{
|
||||
Name: IssuerTypeLetsencrypt,
|
||||
Email: email,
|
||||
},
|
||||
}
|
||||
defaultCredentialConfig := make([]CredentialEntry, 0)
|
||||
config := &Config{
|
||||
AutomaticHttps: true,
|
||||
FallbackForInvalidSecret: false,
|
||||
RenewBeforeDays: DefaultRenewBeforeDays,
|
||||
ACMEIssuer: defaultIssuer,
|
||||
CredentialConfig: defaultCredentialConfig,
|
||||
Version: time.Now().Format("20060102030405"),
|
||||
}
|
||||
return config
|
||||
}
|
||||
|
||||
func getRandEmail() string {
|
||||
num1 := rangeRandom(100, 100000)
|
||||
num2 := rangeRandom(100, 100000)
|
||||
return fmt.Sprintf("your%d@yours%d.com", num1, num2)
|
||||
}
|
||||
122
pkg/cert/config_test.go
Normal file
122
pkg/cert/config_test.go
Normal file
@@ -0,0 +1,122 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"testing"
|
||||
|
||||
"github.com/stretchr/testify/assert"
|
||||
)
|
||||
|
||||
func TestMatchSecretNameByDomain(t *testing.T) {
|
||||
tests := []struct {
|
||||
name string
|
||||
domain string
|
||||
credentialCfg []CredentialEntry
|
||||
expected string
|
||||
}{
|
||||
{
|
||||
name: "Exact match",
|
||||
domain: "example.com",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"example.com"},
|
||||
TLSSecret: "example-com-tls",
|
||||
},
|
||||
},
|
||||
expected: "example-com-tls",
|
||||
},
|
||||
|
||||
{
|
||||
name: "Exact match ignore case ",
|
||||
domain: "eXample.com",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"example.com"},
|
||||
TLSSecret: "example-com-tls",
|
||||
},
|
||||
},
|
||||
expected: "example-com-tls",
|
||||
},
|
||||
{
|
||||
name: "Wildcard match",
|
||||
domain: "sub.example.com",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"*.example.com"},
|
||||
TLSSecret: "wildcard-example-com-tls",
|
||||
},
|
||||
},
|
||||
expected: "wildcard-example-com-tls",
|
||||
},
|
||||
|
||||
{
|
||||
name: "Wildcard match ignore case",
|
||||
domain: "sub.Example.com",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"*.example.com"},
|
||||
TLSSecret: "wildcard-example-com-tls",
|
||||
},
|
||||
},
|
||||
expected: "wildcard-example-com-tls",
|
||||
},
|
||||
{
|
||||
name: "* match",
|
||||
domain: "blog.example.co.uk",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"*"},
|
||||
TLSSecret: "blog-co-uk-tls",
|
||||
},
|
||||
},
|
||||
expected: "blog-co-uk-tls",
|
||||
},
|
||||
{
|
||||
name: "No match",
|
||||
domain: "unknown.com",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"example.com"},
|
||||
TLSSecret: "example-com-tls",
|
||||
},
|
||||
},
|
||||
expected: "",
|
||||
},
|
||||
{
|
||||
name: "Multiple matches - first match wins",
|
||||
domain: "example.com",
|
||||
credentialCfg: []CredentialEntry{
|
||||
{
|
||||
Domains: []string{"example.com"},
|
||||
TLSSecret: "example-com-tls",
|
||||
},
|
||||
{
|
||||
Domains: []string{"*.example.com"},
|
||||
TLSSecret: "wildcard-example-com-tls",
|
||||
},
|
||||
},
|
||||
expected: "example-com-tls",
|
||||
},
|
||||
}
|
||||
|
||||
for _, tt := range tests {
|
||||
t.Run(tt.name, func(t *testing.T) {
|
||||
cfg := Config{CredentialConfig: tt.credentialCfg}
|
||||
result := cfg.MatchSecretNameByDomain(tt.domain)
|
||||
assert.Equal(t, tt.expected, result)
|
||||
})
|
||||
}
|
||||
}
|
||||
165
pkg/cert/controller.go
Normal file
165
pkg/cert/controller.go
Normal file
@@ -0,0 +1,165 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"reflect"
|
||||
"time"
|
||||
|
||||
"k8s.io/apimachinery/pkg/util/runtime"
|
||||
"k8s.io/apimachinery/pkg/util/wait"
|
||||
"k8s.io/client-go/informers"
|
||||
v1informer "k8s.io/client-go/informers/core/v1"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
"k8s.io/client-go/tools/cache"
|
||||
"k8s.io/client-go/util/workqueue"
|
||||
)
|
||||
|
||||
const (
|
||||
workNum = 1
|
||||
maxRetry = 2
|
||||
configMapName = "higress-https"
|
||||
)
|
||||
|
||||
type Controller struct {
|
||||
namespace string
|
||||
ConfigMapInformer v1informer.ConfigMapInformer
|
||||
client kubernetes.Interface
|
||||
queue workqueue.RateLimitingInterface
|
||||
configMgr *ConfigMgr
|
||||
server *Server
|
||||
certMgr *CertMgr
|
||||
factory informers.SharedInformerFactory
|
||||
}
|
||||
|
||||
func (c *Controller) addConfigmap(obj interface{}) {
|
||||
key, err := cache.MetaNamespaceKeyFunc(obj)
|
||||
if err != nil {
|
||||
return
|
||||
}
|
||||
namespace, name, _ := cache.SplitMetaNamespaceKey(key)
|
||||
if namespace != c.namespace || name != configMapName {
|
||||
return
|
||||
}
|
||||
c.enqueue(name)
|
||||
|
||||
}
|
||||
func (c *Controller) updateConfigmap(oldObj interface{}, newObj interface{}) {
|
||||
key, err := cache.MetaNamespaceKeyFunc(oldObj)
|
||||
if err != nil {
|
||||
return
|
||||
}
|
||||
namespace, name, _ := cache.SplitMetaNamespaceKey(key)
|
||||
if namespace != c.namespace || name != configMapName {
|
||||
return
|
||||
}
|
||||
if reflect.DeepEqual(oldObj, newObj) {
|
||||
return
|
||||
}
|
||||
c.enqueue(name)
|
||||
}
|
||||
|
||||
func (c *Controller) enqueue(name string) {
|
||||
c.queue.Add(name)
|
||||
}
|
||||
|
||||
func (c *Controller) cachesSynced() bool {
|
||||
return c.ConfigMapInformer.Informer().HasSynced()
|
||||
}
|
||||
|
||||
func (c *Controller) Run(stopCh <-chan struct{}) error {
|
||||
defer runtime.HandleCrash()
|
||||
defer c.queue.ShutDown()
|
||||
CertLog.Info("Waiting for informer caches to sync")
|
||||
c.factory.Start(stopCh)
|
||||
if ok := cache.WaitForCacheSync(stopCh, c.cachesSynced); !ok {
|
||||
return fmt.Errorf("failed to wait for caches to sync")
|
||||
}
|
||||
CertLog.Info("Starting controller")
|
||||
// Launch one workers to process configmap resources
|
||||
for i := 0; i < workNum; i++ {
|
||||
go wait.Until(c.worker, time.Minute, stopCh)
|
||||
}
|
||||
CertLog.Info("Started workers")
|
||||
<-stopCh
|
||||
CertLog.Info("Shutting down workers")
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func (c *Controller) worker() {
|
||||
for c.processNextItem() {
|
||||
|
||||
}
|
||||
}
|
||||
|
||||
func (c *Controller) processNextItem() bool {
|
||||
item, shutdown := c.queue.Get()
|
||||
if shutdown {
|
||||
return false
|
||||
}
|
||||
defer c.queue.Done(item)
|
||||
key := item.(string)
|
||||
CertLog.Infof("controller process item:%s", key)
|
||||
err := c.syncConfigmap(key)
|
||||
if err != nil {
|
||||
c.handleError(key, err)
|
||||
}
|
||||
return true
|
||||
}
|
||||
|
||||
func (c *Controller) syncConfigmap(key string) error {
|
||||
configmap, err := c.ConfigMapInformer.Lister().ConfigMaps(c.namespace).Get(key)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
newConfig, err := c.configMgr.ParseConfigFromConfigmap(configmap)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
oldConfig := c.configMgr.GetConfig()
|
||||
// reconcile old config and new config
|
||||
return c.certMgr.Reconcile(context.Background(), oldConfig, newConfig)
|
||||
}
|
||||
|
||||
func (c *Controller) handleError(key string, err error) {
|
||||
runtime.HandleError(err)
|
||||
CertLog.Errorf("%+v", err)
|
||||
c.queue.Forget(key)
|
||||
}
|
||||
|
||||
func NewController(client kubernetes.Interface, namespace string, certMgr *CertMgr, configMgr *ConfigMgr) (*Controller, error) {
|
||||
kubeInformerFactory := informers.NewSharedInformerFactoryWithOptions(client, 0, informers.WithNamespace(namespace))
|
||||
configmapInformer := kubeInformerFactory.Core().V1().ConfigMaps()
|
||||
c := &Controller{
|
||||
certMgr: certMgr,
|
||||
configMgr: configMgr,
|
||||
client: client,
|
||||
namespace: namespace,
|
||||
factory: kubeInformerFactory,
|
||||
ConfigMapInformer: configmapInformer,
|
||||
queue: workqueue.NewNamedRateLimitingQueue(workqueue.DefaultControllerRateLimiter(), "ingressManage"),
|
||||
}
|
||||
|
||||
CertLog.Info("Setting up configmap informer event handlers")
|
||||
configmapInformer.Informer().AddEventHandler(cache.ResourceEventHandlerFuncs{
|
||||
AddFunc: c.addConfigmap,
|
||||
UpdateFunc: c.updateConfigmap,
|
||||
})
|
||||
|
||||
return c, nil
|
||||
}
|
||||
158
pkg/cert/ingress.go
Normal file
158
pkg/cert/ingress.go
Normal file
@@ -0,0 +1,158 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"strings"
|
||||
"sync"
|
||||
"time"
|
||||
|
||||
"github.com/caddyserver/certmagic"
|
||||
"github.com/mholt/acmez"
|
||||
"github.com/mholt/acmez/acme"
|
||||
v1 "k8s.io/api/networking/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
)
|
||||
|
||||
const (
|
||||
IngressClassName = "higress"
|
||||
IngressServiceName = "higress-controller"
|
||||
IngressNamePefix = "higress-http-solver-"
|
||||
IngressPathPrefix = "/.well-known/acme-challenge/"
|
||||
IngressServicePort = 8889
|
||||
)
|
||||
|
||||
type IngressSolver struct {
|
||||
client kubernetes.Interface
|
||||
acmeIssuer *certmagic.ACMEIssuer
|
||||
solversMu sync.Mutex
|
||||
namespace string
|
||||
ingressDelay time.Duration
|
||||
}
|
||||
|
||||
func NewIngressSolver(namespace string, client kubernetes.Interface, acmeIssuer *certmagic.ACMEIssuer) (acmez.Solver, error) {
|
||||
solver := &IngressSolver{
|
||||
namespace: namespace,
|
||||
client: client,
|
||||
acmeIssuer: acmeIssuer,
|
||||
ingressDelay: 5 * time.Second,
|
||||
}
|
||||
return solver, nil
|
||||
}
|
||||
|
||||
func (s *IngressSolver) Present(_ context.Context, challenge acme.Challenge) error {
|
||||
CertLog.Infof("ingress solver present challenge:%+v", challenge)
|
||||
s.solversMu.Lock()
|
||||
defer s.solversMu.Unlock()
|
||||
ingressName := s.getIngressName(challenge)
|
||||
ingress := s.constructIngress(challenge)
|
||||
CertLog.Infof("update ingress name:%s, ingress:%v", ingressName, ingress)
|
||||
_, err := s.client.NetworkingV1().Ingresses(s.namespace).Get(context.Background(), ingressName, metav1.GetOptions{})
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
// create ingress
|
||||
_, err2 := s.client.NetworkingV1().Ingresses(s.namespace).Create(context.Background(), ingress, metav1.CreateOptions{})
|
||||
return err2
|
||||
}
|
||||
return err
|
||||
}
|
||||
_, err1 := s.client.NetworkingV1().Ingresses(s.namespace).Update(context.Background(), ingress, metav1.UpdateOptions{})
|
||||
if err1 != nil {
|
||||
return err1
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *IngressSolver) Wait(ctx context.Context, challenge acme.Challenge) error {
|
||||
CertLog.Infof("ingress solver wait challenge:%+v", challenge)
|
||||
// wait for ingress ready
|
||||
if s.ingressDelay > 0 {
|
||||
select {
|
||||
case <-time.After(s.ingressDelay):
|
||||
case <-ctx.Done():
|
||||
return ctx.Err()
|
||||
}
|
||||
}
|
||||
CertLog.Infof("ingress solver wait challenge done")
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *IngressSolver) CleanUp(_ context.Context, challenge acme.Challenge) error {
|
||||
CertLog.Infof("ingress solver cleanup challenge:%+v", challenge)
|
||||
s.solversMu.Lock()
|
||||
defer s.solversMu.Unlock()
|
||||
ingressName := s.getIngressName(challenge)
|
||||
CertLog.Infof("cleanup ingress name:%s", ingressName)
|
||||
err := s.client.NetworkingV1().Ingresses(s.namespace).Delete(context.Background(), ingressName, metav1.DeleteOptions{})
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *IngressSolver) Delete(_ context.Context, challenge acme.Challenge) error {
|
||||
s.solversMu.Lock()
|
||||
defer s.solversMu.Unlock()
|
||||
err := s.client.NetworkingV1().Ingresses(s.namespace).Delete(context.Background(), s.getIngressName(challenge), metav1.DeleteOptions{})
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *IngressSolver) getIngressName(challenge acme.Challenge) string {
|
||||
return IngressNamePefix + strings.ReplaceAll(challenge.Identifier.Value, ".", "-")
|
||||
}
|
||||
|
||||
func (s *IngressSolver) constructIngress(challenge acme.Challenge) *v1.Ingress {
|
||||
ingressClassName := IngressClassName
|
||||
ingressDomain := challenge.Identifier.Value
|
||||
ingressPath := IngressPathPrefix + challenge.Token
|
||||
ingress := v1.Ingress{}
|
||||
ingress.Name = s.getIngressName(challenge)
|
||||
ingress.Namespace = s.namespace
|
||||
pathType := v1.PathTypePrefix
|
||||
ingress.Spec = v1.IngressSpec{
|
||||
IngressClassName: &ingressClassName,
|
||||
Rules: []v1.IngressRule{
|
||||
{
|
||||
Host: ingressDomain,
|
||||
IngressRuleValue: v1.IngressRuleValue{
|
||||
HTTP: &v1.HTTPIngressRuleValue{
|
||||
Paths: []v1.HTTPIngressPath{
|
||||
{
|
||||
Path: ingressPath,
|
||||
PathType: &pathType,
|
||||
Backend: v1.IngressBackend{
|
||||
Service: &v1.IngressServiceBackend{
|
||||
Name: IngressServiceName,
|
||||
Port: v1.ServiceBackendPort{
|
||||
Number: IngressServicePort,
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
return &ingress
|
||||
}
|
||||
19
pkg/cert/log.go
Normal file
19
pkg/cert/log.go
Normal file
@@ -0,0 +1,19 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import "istio.io/pkg/log"
|
||||
|
||||
var CertLog = log.RegisterScope("cert", "Higress Cert process.", 0)
|
||||
108
pkg/cert/secret.go
Normal file
108
pkg/cert/secret.go
Normal file
@@ -0,0 +1,108 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"strconv"
|
||||
"strings"
|
||||
"time"
|
||||
|
||||
v1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
)
|
||||
|
||||
const (
|
||||
SecretNamePrefix = "higress-secret-"
|
||||
)
|
||||
|
||||
type SecretMgr struct {
|
||||
client kubernetes.Interface
|
||||
namespace string
|
||||
}
|
||||
|
||||
func NewSecretMgr(namespace string, client kubernetes.Interface) (*SecretMgr, error) {
|
||||
secretMgr := &SecretMgr{
|
||||
namespace: namespace,
|
||||
client: client,
|
||||
}
|
||||
|
||||
return secretMgr, nil
|
||||
}
|
||||
|
||||
func (s *SecretMgr) Update(domain string, secretName string, privateKey []byte, certificate []byte, notBefore time.Time, notAfter time.Time, isRenew bool) error {
|
||||
//secretName := s.getSecretName(domain)
|
||||
secret := s.constructSecret(domain, privateKey, certificate, notBefore, notAfter, isRenew)
|
||||
_, err := s.client.CoreV1().Secrets(s.namespace).Get(context.Background(), secretName, metav1.GetOptions{})
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
// create secret
|
||||
_, err2 := s.client.CoreV1().Secrets(s.namespace).Create(context.Background(), secret, metav1.CreateOptions{})
|
||||
return err2
|
||||
}
|
||||
return err
|
||||
}
|
||||
// check secret annotations
|
||||
if _, ok := secret.Annotations["higress.io/cert-domain"]; !ok {
|
||||
return fmt.Errorf("the secret name %s is not automatic https secret name for the domain:%s, please rename it in config", secretName, domain)
|
||||
}
|
||||
_, err1 := s.client.CoreV1().Secrets(s.namespace).Update(context.Background(), secret, metav1.UpdateOptions{})
|
||||
if err1 != nil {
|
||||
return err1
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *SecretMgr) Delete(domain string) error {
|
||||
secretName := s.getSecretName(domain)
|
||||
err := s.client.CoreV1().Secrets(s.namespace).Delete(context.Background(), secretName, metav1.DeleteOptions{})
|
||||
return err
|
||||
}
|
||||
|
||||
func (s *SecretMgr) getSecretName(domain string) string {
|
||||
return SecretNamePrefix + strings.ReplaceAll(strings.TrimSpace(domain), ".", "-")
|
||||
}
|
||||
|
||||
func (s *SecretMgr) constructSecret(domain string, privateKey []byte, certificate []byte, notBefore time.Time, notAfter time.Time, isRenew bool) *v1.Secret {
|
||||
secretName := s.getSecretName(domain)
|
||||
annotationMap := make(map[string]string, 0)
|
||||
annotationMap["higress.io/cert-domain"] = domain
|
||||
annotationMap["higress.io/cert-notAfter"] = notAfter.Format("2006-01-02 15:04:05")
|
||||
annotationMap["higress.io/cert-notBefore"] = notBefore.Format("2006-01-02 15:04:05")
|
||||
annotationMap["higress.io/cert-renew"] = strconv.FormatBool(isRenew)
|
||||
if isRenew {
|
||||
annotationMap["higress.io/cert-renew-time"] = time.Now().Format("2006-01-02 15:04:05")
|
||||
}
|
||||
// Required fields:
|
||||
// - Secret.Data["tls.key"] - TLS private key.
|
||||
// Secret.Data["tls.crt"] - TLS certificate.
|
||||
dataMap := make(map[string][]byte, 0)
|
||||
dataMap["tls.key"] = privateKey
|
||||
dataMap["tls.crt"] = certificate
|
||||
secret := &v1.Secret{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Name: secretName,
|
||||
Namespace: s.namespace,
|
||||
Annotations: annotationMap,
|
||||
},
|
||||
Type: v1.SecretTypeTLS,
|
||||
Data: dataMap,
|
||||
}
|
||||
return secret
|
||||
}
|
||||
115
pkg/cert/server.go
Normal file
115
pkg/cert/server.go
Normal file
@@ -0,0 +1,115 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"fmt"
|
||||
"net"
|
||||
"net/http"
|
||||
"time"
|
||||
|
||||
"github.com/caddyserver/certmagic"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
)
|
||||
|
||||
type Option struct {
|
||||
Namespace string
|
||||
ServerAddress string
|
||||
Email string
|
||||
}
|
||||
|
||||
type Server struct {
|
||||
httpServer *http.Server
|
||||
opts *Option
|
||||
clientSet kubernetes.Interface
|
||||
controller *Controller
|
||||
certMgr *CertMgr
|
||||
}
|
||||
|
||||
func NewServer(clientSet kubernetes.Interface, opts *Option) (*Server, error) {
|
||||
server := &Server{
|
||||
clientSet: clientSet,
|
||||
opts: opts,
|
||||
}
|
||||
return server, nil
|
||||
}
|
||||
|
||||
func (s *Server) InitDefaultConfig() error {
|
||||
configMgr, _ := NewConfigMgr(s.opts.Namespace, s.clientSet)
|
||||
// init config if there is not existed
|
||||
_, err := configMgr.InitConfig(s.opts.Email)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *Server) InitServer() error {
|
||||
configMgr, _ := NewConfigMgr(s.opts.Namespace, s.clientSet)
|
||||
// init config if there is not existed
|
||||
defaultConfig, err := configMgr.InitConfig(s.opts.Email)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
// init certmgr
|
||||
certMgr, err := InitCertMgr(s.opts, s.clientSet, defaultConfig) // config and start
|
||||
s.certMgr = certMgr
|
||||
// init controller
|
||||
controller, err := NewController(s.clientSet, s.opts.Namespace, certMgr, configMgr)
|
||||
s.controller = controller
|
||||
// init http server
|
||||
s.initHttpServer()
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *Server) initHttpServer() error {
|
||||
CertLog.Infof("server init http server")
|
||||
ctx := context.Background()
|
||||
mux := http.NewServeMux()
|
||||
mux.HandleFunc("/", func(w http.ResponseWriter, r *http.Request) {
|
||||
fmt.Fprintf(w, "Lookit my cool website over HTTPS!")
|
||||
})
|
||||
httpServer := &http.Server{
|
||||
ReadHeaderTimeout: 5 * time.Second,
|
||||
ReadTimeout: 5 * time.Second,
|
||||
WriteTimeout: 5 * time.Second,
|
||||
IdleTimeout: 5 * time.Second,
|
||||
Addr: s.opts.ServerAddress,
|
||||
BaseContext: func(listener net.Listener) context.Context { return ctx },
|
||||
}
|
||||
cfg := s.certMgr.cfg
|
||||
if len(cfg.Issuers) > 0 {
|
||||
if am, ok := cfg.Issuers[0].(*certmagic.ACMEIssuer); ok {
|
||||
httpServer.Handler = am.HTTPChallengeHandler(mux)
|
||||
}
|
||||
} else {
|
||||
httpServer.Handler = mux
|
||||
}
|
||||
s.httpServer = httpServer
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *Server) Run(stopCh <-chan struct{}) error {
|
||||
go s.controller.Run(stopCh)
|
||||
CertLog.Infof("server run")
|
||||
go func() {
|
||||
<-stopCh
|
||||
CertLog.Infof("server http server shutdown now...")
|
||||
s.httpServer.Shutdown(context.Background())
|
||||
}()
|
||||
err := s.httpServer.ListenAndServe()
|
||||
return err
|
||||
}
|
||||
337
pkg/cert/storage.go
Normal file
337
pkg/cert/storage.go
Normal file
@@ -0,0 +1,337 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
"encoding/json"
|
||||
"fmt"
|
||||
"io/fs"
|
||||
"path"
|
||||
"strings"
|
||||
"sync"
|
||||
"time"
|
||||
|
||||
"github.com/caddyserver/certmagic"
|
||||
v1 "k8s.io/api/core/v1"
|
||||
"k8s.io/apimachinery/pkg/api/errors"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"k8s.io/client-go/kubernetes"
|
||||
)
|
||||
|
||||
const (
|
||||
CertificatesPrefix = "/certificates"
|
||||
ConfigmapStoreCertficatesPrefix = "higress-cert-store-certificates-"
|
||||
ConfigmapStoreDefaultName = "higress-cert-store-default"
|
||||
)
|
||||
|
||||
var _ certmagic.Storage = (*ConfigmapStorage)(nil)
|
||||
|
||||
type ConfigmapStorage struct {
|
||||
namespace string
|
||||
client kubernetes.Interface
|
||||
mux sync.RWMutex
|
||||
}
|
||||
|
||||
type HashValue struct {
|
||||
K string `json:"k,omitempty"`
|
||||
V []byte `json:"v,omitempty"`
|
||||
}
|
||||
|
||||
func NewConfigmapStorage(namespace string, client kubernetes.Interface) (certmagic.Storage, error) {
|
||||
storage := &ConfigmapStorage{
|
||||
namespace: namespace,
|
||||
client: client,
|
||||
}
|
||||
return storage, nil
|
||||
}
|
||||
|
||||
// Exists returns true if key exists in s.
|
||||
func (s *ConfigmapStorage) Exists(_ context.Context, key string) bool {
|
||||
s.mux.RLock()
|
||||
defer s.mux.RUnlock()
|
||||
cm, err := s.getConfigmapStoreByKey(key)
|
||||
if err != nil {
|
||||
return false
|
||||
}
|
||||
if cm.Data == nil {
|
||||
return false
|
||||
}
|
||||
|
||||
hashKey := fastHash([]byte(key))
|
||||
if _, ok := cm.Data[hashKey]; ok {
|
||||
return true
|
||||
}
|
||||
return false
|
||||
}
|
||||
|
||||
// Store saves value at key.
|
||||
func (s *ConfigmapStorage) Store(_ context.Context, key string, value []byte) error {
|
||||
s.mux.Lock()
|
||||
defer s.mux.Unlock()
|
||||
cm, err := s.getConfigmapStoreByKey(key)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
if cm.Data == nil {
|
||||
cm.Data = make(map[string]string, 0)
|
||||
}
|
||||
|
||||
hashKey := fastHash([]byte(key))
|
||||
hashV := &HashValue{
|
||||
K: key,
|
||||
V: value,
|
||||
}
|
||||
bytes, err := json.Marshal(hashV)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
cm.Data[hashKey] = string(bytes)
|
||||
return s.updateConfigmap(cm)
|
||||
}
|
||||
|
||||
// Load retrieves the value at key.
|
||||
func (s *ConfigmapStorage) Load(_ context.Context, key string) ([]byte, error) {
|
||||
s.mux.RLock()
|
||||
defer s.mux.RUnlock()
|
||||
var value []byte
|
||||
cm, err := s.getConfigmapStoreByKey(key)
|
||||
if err != nil {
|
||||
return value, err
|
||||
}
|
||||
if cm.Data == nil {
|
||||
return value, fs.ErrNotExist
|
||||
}
|
||||
|
||||
hashKey := fastHash([]byte(key))
|
||||
if v, ok := cm.Data[hashKey]; ok {
|
||||
hV := &HashValue{}
|
||||
err = json.Unmarshal([]byte(v), hV)
|
||||
if err != nil {
|
||||
return value, err
|
||||
}
|
||||
return hV.V, nil
|
||||
}
|
||||
return value, fs.ErrNotExist
|
||||
}
|
||||
|
||||
// Delete deletes the value at key.
|
||||
func (s *ConfigmapStorage) Delete(_ context.Context, key string) error {
|
||||
s.mux.Lock()
|
||||
defer s.mux.Unlock()
|
||||
cm, err := s.getConfigmapStoreByKey(key)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
if cm.Data == nil {
|
||||
cm.Data = make(map[string]string, 0)
|
||||
}
|
||||
hashKey := fastHash([]byte(key))
|
||||
delete(cm.Data, hashKey)
|
||||
return s.updateConfigmap(cm)
|
||||
}
|
||||
|
||||
// List returns all keys that match the prefix.
|
||||
// If the prefix is "/certificates", it retrieves all ConfigMaps, otherwise only one.
|
||||
func (s *ConfigmapStorage) List(ctx context.Context, prefix string, recursive bool) ([]string, error) {
|
||||
s.mux.RLock()
|
||||
defer s.mux.RUnlock()
|
||||
var keys []string
|
||||
var configmapKeys []string
|
||||
visitedDirs := make(map[string]struct{})
|
||||
|
||||
// Check if the prefix corresponds to a specific key
|
||||
hashPrefix := fastHash([]byte(prefix))
|
||||
if strings.HasPrefix(prefix, CertificatesPrefix) {
|
||||
// If the prefix is "/certificates", get all ConfigMaps and traverse each one
|
||||
// List all ConfigMaps in the namespace with label higress.io/cert-https=true
|
||||
configmaps, err := s.client.CoreV1().ConfigMaps(s.namespace).List(ctx, metav1.ListOptions{FieldSelector: "metadata.annotations['higress.io/cert-https'] == 'true'"})
|
||||
if err != nil {
|
||||
return keys, err
|
||||
}
|
||||
|
||||
for _, cm := range configmaps.Items {
|
||||
// Check if the ConfigMap name starts with the expected prefix
|
||||
if strings.HasPrefix(cm.Name, ConfigmapStoreCertficatesPrefix) {
|
||||
// Add the keys from Data field to the list
|
||||
for _, v := range cm.Data {
|
||||
// Unmarshal the value into hashValue struct
|
||||
var hv HashValue
|
||||
if err := json.Unmarshal([]byte(v), &hv); err != nil {
|
||||
return nil, err
|
||||
}
|
||||
// Check if the key starts with the specified prefix
|
||||
if strings.HasPrefix(hv.K, prefix) {
|
||||
// Add the key to the list
|
||||
configmapKeys = append(configmapKeys, hv.K)
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
} else {
|
||||
// If not starting with "/certificates", get the specific ConfigMap
|
||||
cm, err := s.getConfigmapStoreByKey(prefix)
|
||||
if err != nil {
|
||||
return keys, err
|
||||
}
|
||||
|
||||
if _, ok := cm.Data[hashPrefix]; ok {
|
||||
// The prefix corresponds to a specific key, add it to the list
|
||||
configmapKeys = append(configmapKeys, prefix)
|
||||
} else {
|
||||
// The prefix is considered a directory
|
||||
for _, v := range cm.Data {
|
||||
// Unmarshal the value into hashValue struct
|
||||
var hv HashValue
|
||||
if err := json.Unmarshal([]byte(v), &hv); err != nil {
|
||||
return nil, err
|
||||
}
|
||||
// Check if the key starts with the specified prefix
|
||||
if strings.HasPrefix(hv.K, prefix) {
|
||||
// Add the key to the list
|
||||
configmapKeys = append(configmapKeys, hv.K)
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
// return all
|
||||
if recursive {
|
||||
return configmapKeys, nil
|
||||
}
|
||||
|
||||
// only return sub dirs
|
||||
for _, key := range configmapKeys {
|
||||
subPath := strings.TrimPrefix(strings.ReplaceAll(key, prefix, ""), "/")
|
||||
paths := strings.Split(subPath, "/")
|
||||
if len(paths) > 0 {
|
||||
subDir := path.Join(prefix, paths[0])
|
||||
if _, ok := visitedDirs[subDir]; !ok {
|
||||
keys = append(keys, subDir)
|
||||
}
|
||||
visitedDirs[subDir] = struct{}{}
|
||||
}
|
||||
}
|
||||
|
||||
return keys, nil
|
||||
}
|
||||
|
||||
// Stat returns information about key. only support for no certificates path
|
||||
func (s *ConfigmapStorage) Stat(_ context.Context, key string) (certmagic.KeyInfo, error) {
|
||||
s.mux.RLock()
|
||||
defer s.mux.RUnlock()
|
||||
// Create a new KeyInfo struct
|
||||
info := certmagic.KeyInfo{}
|
||||
|
||||
// Get the ConfigMap containing the keys
|
||||
cm, err := s.getConfigmapStoreByKey(key)
|
||||
if err != nil {
|
||||
return info, err
|
||||
}
|
||||
|
||||
// Check if the key exists in the ConfigMap
|
||||
hashKey := fastHash([]byte(key))
|
||||
if data, ok := cm.Data[hashKey]; ok {
|
||||
// The key exists, populate the KeyInfo struct
|
||||
info.Key = key
|
||||
info.Modified = time.Now() // Since we're not tracking modification time in ConfigMap
|
||||
info.Size = int64(len(data))
|
||||
info.IsTerminal = true
|
||||
} else {
|
||||
// Check if there are other keys with the same prefix
|
||||
prefixKeys := make([]string, 0)
|
||||
for _, v := range cm.Data {
|
||||
var hv HashValue
|
||||
if err := json.Unmarshal([]byte(v), &hv); err != nil {
|
||||
return info, err
|
||||
}
|
||||
// Check if the key starts with the specified prefix
|
||||
if strings.HasPrefix(hv.K, key) {
|
||||
// Add the key to the list
|
||||
prefixKeys = append(prefixKeys, hv.K)
|
||||
}
|
||||
}
|
||||
// If there are multiple keys with the same prefix, then it's not a terminal node
|
||||
if len(prefixKeys) > 0 {
|
||||
info.Key = key
|
||||
info.IsTerminal = false
|
||||
} else {
|
||||
return info, fmt.Errorf("prefix '%s' is not existed", key)
|
||||
}
|
||||
}
|
||||
return info, nil
|
||||
}
|
||||
|
||||
// Lock obtains a lock named by the given name. It blocks
|
||||
// until the lock can be obtained or an error is returned.
|
||||
func (s *ConfigmapStorage) Lock(ctx context.Context, name string) error {
|
||||
return nil
|
||||
}
|
||||
|
||||
// Unlock releases the lock for name.
|
||||
func (s *ConfigmapStorage) Unlock(_ context.Context, name string) error {
|
||||
return nil
|
||||
}
|
||||
|
||||
func (s *ConfigmapStorage) String() string {
|
||||
return "ConfigmapStorage"
|
||||
}
|
||||
|
||||
func (s *ConfigmapStorage) getConfigmapStoreNameByKey(key string) string {
|
||||
parts := strings.SplitN(key, "/", 10)
|
||||
if len(parts) >= 4 && parts[1] == "certificates" {
|
||||
domain := strings.TrimSuffix(parts[3], ".crt")
|
||||
domain = strings.TrimSuffix(domain, ".key")
|
||||
domain = strings.TrimSuffix(domain, ".json")
|
||||
issuerKey := parts[2]
|
||||
return ConfigmapStoreCertficatesPrefix + fastHash([]byte(issuerKey+domain))
|
||||
}
|
||||
return ConfigmapStoreDefaultName
|
||||
}
|
||||
|
||||
func (s *ConfigmapStorage) getConfigmapStoreByKey(key string) (*v1.ConfigMap, error) {
|
||||
configmapName := s.getConfigmapStoreNameByKey(key)
|
||||
cm, err := s.client.CoreV1().ConfigMaps(s.namespace).Get(context.Background(), configmapName, metav1.GetOptions{})
|
||||
if err != nil {
|
||||
if errors.IsNotFound(err) {
|
||||
// Save default ConfigMap
|
||||
cm = &v1.ConfigMap{
|
||||
ObjectMeta: metav1.ObjectMeta{
|
||||
Namespace: s.namespace,
|
||||
Name: configmapName,
|
||||
Annotations: map[string]string{"higress.io/cert-https": "true"},
|
||||
},
|
||||
}
|
||||
_, err = s.client.CoreV1().ConfigMaps(s.namespace).Create(context.Background(), cm, metav1.CreateOptions{})
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
} else {
|
||||
return nil, err
|
||||
}
|
||||
}
|
||||
return cm, nil
|
||||
}
|
||||
|
||||
// updateConfigmap adds or updates the annotation higress.io/cert-https to true.
|
||||
func (s *ConfigmapStorage) updateConfigmap(configmap *v1.ConfigMap) error {
|
||||
if configmap.ObjectMeta.Annotations == nil {
|
||||
configmap.ObjectMeta.Annotations = make(map[string]string)
|
||||
}
|
||||
configmap.ObjectMeta.Annotations["higress.io/cert-https"] = "true"
|
||||
|
||||
_, err := s.client.CoreV1().ConfigMaps(configmap.Namespace).Update(context.Background(), configmap, metav1.UpdateOptions{})
|
||||
return err
|
||||
}
|
||||
325
pkg/cert/storage_test.go
Normal file
325
pkg/cert/storage_test.go
Normal file
@@ -0,0 +1,325 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"context"
|
||||
metav1 "k8s.io/apimachinery/pkg/apis/meta/v1"
|
||||
"testing"
|
||||
|
||||
"github.com/stretchr/testify/assert"
|
||||
"k8s.io/client-go/kubernetes/fake"
|
||||
)
|
||||
|
||||
func TestGetConfigmapStoreNameByKey(t *testing.T) {
|
||||
// Create a fake client for testing
|
||||
fakeClient := fake.NewSimpleClientset()
|
||||
// Create a new ConfigmapStorage instance for testing
|
||||
namespace := "your-namespace"
|
||||
storage := &ConfigmapStorage{
|
||||
namespace: namespace,
|
||||
client: fakeClient,
|
||||
}
|
||||
tests := []struct {
|
||||
name string
|
||||
key string
|
||||
expected string
|
||||
}{
|
||||
{
|
||||
name: "certificate crt",
|
||||
key: "/certificates/issuerKey/domain.crt",
|
||||
expected: "higress-cert-store-certificates-" + fastHash([]byte("issuerKey"+"domain")),
|
||||
},
|
||||
{
|
||||
name: "certificate meta",
|
||||
key: "/certificates/issuerKey/domain.json",
|
||||
expected: "higress-cert-store-certificates-" + fastHash([]byte("issuerKey"+"domain")),
|
||||
},
|
||||
{
|
||||
name: "certificate key",
|
||||
key: "/certificates/issuerKey/domain.key",
|
||||
expected: "higress-cert-store-certificates-" + fastHash([]byte("issuerKey"+"domain")),
|
||||
},
|
||||
{
|
||||
name: "user key",
|
||||
key: "/users/hello/2",
|
||||
expected: "higress-cert-store-default",
|
||||
},
|
||||
{
|
||||
name: "Empty Key",
|
||||
key: "",
|
||||
expected: "higress-cert-store-default",
|
||||
},
|
||||
}
|
||||
|
||||
for _, test := range tests {
|
||||
t.Run(test.name, func(t *testing.T) {
|
||||
storageName := storage.getConfigmapStoreNameByKey(test.key)
|
||||
assert.Equal(t, test.expected, storageName)
|
||||
})
|
||||
}
|
||||
}
|
||||
|
||||
func TestExists(t *testing.T) {
|
||||
// Create a fake client for testing
|
||||
fakeClient := fake.NewSimpleClientset()
|
||||
|
||||
// Create a new ConfigmapStorage instance for testing
|
||||
namespace := "your-namespace"
|
||||
storage, err := NewConfigmapStorage(namespace, fakeClient)
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Store a test key
|
||||
testKey := "/certificates/issuer1/domain1.crt"
|
||||
err = storage.Store(context.Background(), testKey, []byte("test-data"))
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Define test cases
|
||||
tests := []struct {
|
||||
name string
|
||||
key string
|
||||
shouldExist bool
|
||||
}{
|
||||
{
|
||||
name: "Existing Key",
|
||||
key: "/certificates/issuer1/domain1.crt",
|
||||
shouldExist: true,
|
||||
},
|
||||
{
|
||||
name: "Non-Existent Key1",
|
||||
key: "/certificates/issuer2/domain2.crt",
|
||||
shouldExist: false,
|
||||
},
|
||||
{
|
||||
name: "Non-Existent Key2",
|
||||
key: "/users/hello/a",
|
||||
shouldExist: false,
|
||||
},
|
||||
// Add more test cases as needed
|
||||
}
|
||||
|
||||
// Run tests
|
||||
for _, test := range tests {
|
||||
t.Run(test.name, func(t *testing.T) {
|
||||
exists := storage.Exists(context.Background(), test.key)
|
||||
assert.Equal(t, test.shouldExist, exists)
|
||||
})
|
||||
}
|
||||
}
|
||||
|
||||
func TestLoad(t *testing.T) {
|
||||
// Create a fake client for testing
|
||||
fakeClient := fake.NewSimpleClientset()
|
||||
|
||||
// Create a new ConfigmapStorage instance for testing
|
||||
namespace := "your-namespace"
|
||||
storage, err := NewConfigmapStorage(namespace, fakeClient)
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Store a test key
|
||||
testKey := "/certificates/issuer1/domain1.crt"
|
||||
testValue := []byte("test-data")
|
||||
err = storage.Store(context.Background(), testKey, testValue)
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Define test cases
|
||||
tests := []struct {
|
||||
name string
|
||||
key string
|
||||
expected []byte
|
||||
shouldError bool
|
||||
}{
|
||||
{
|
||||
name: "Existing Key",
|
||||
key: "/certificates/issuer1/domain1.crt",
|
||||
expected: testValue,
|
||||
shouldError: false,
|
||||
},
|
||||
{
|
||||
name: "Non-Existent Key",
|
||||
key: "/certificates/issuer2/domain2.crt",
|
||||
expected: nil,
|
||||
shouldError: true,
|
||||
},
|
||||
// Add more test cases as needed
|
||||
}
|
||||
|
||||
// Run tests
|
||||
for _, test := range tests {
|
||||
t.Run(test.name, func(t *testing.T) {
|
||||
value, err := storage.Load(context.Background(), test.key)
|
||||
if test.shouldError {
|
||||
assert.Error(t, err)
|
||||
assert.Nil(t, value)
|
||||
} else {
|
||||
assert.NoError(t, err)
|
||||
assert.Equal(t, test.expected, value)
|
||||
}
|
||||
})
|
||||
}
|
||||
}
|
||||
|
||||
func TestStore(t *testing.T) {
|
||||
// Create a fake client for testing
|
||||
fakeClient := fake.NewSimpleClientset()
|
||||
|
||||
// Create a new ConfigmapStorage instance for testing
|
||||
namespace := "your-namespace"
|
||||
storage := ConfigmapStorage{
|
||||
namespace: namespace,
|
||||
client: fakeClient,
|
||||
}
|
||||
|
||||
// Define test cases
|
||||
tests := []struct {
|
||||
name string
|
||||
key string
|
||||
value []byte
|
||||
expected map[string]string
|
||||
expectedConfigmapName string
|
||||
shouldError bool
|
||||
}{
|
||||
{
|
||||
name: "Store Key with /certificates prefix",
|
||||
key: "/certificates/issuer1/domain1.crt",
|
||||
value: []byte("test-data1"),
|
||||
expected: map[string]string{fastHash([]byte("/certificates/issuer1/domain1.crt")): `{"k":"/certificates/issuer1/domain1.crt","v":"dGVzdC1kYXRhMQ=="}`},
|
||||
expectedConfigmapName: "higress-cert-store-certificates-" + fastHash([]byte("issuer1"+"domain1")),
|
||||
shouldError: false,
|
||||
},
|
||||
{
|
||||
name: "Store Key with /certificates prefix (additional data)",
|
||||
key: "/certificates/issuer2/domain2.crt",
|
||||
value: []byte("test-data2"),
|
||||
expected: map[string]string{
|
||||
fastHash([]byte("/certificates/issuer2/domain2.crt")): `{"k":"/certificates/issuer2/domain2.crt","v":"dGVzdC1kYXRhMg=="}`,
|
||||
},
|
||||
expectedConfigmapName: "higress-cert-store-certificates-" + fastHash([]byte("issuer2"+"domain2")),
|
||||
shouldError: false,
|
||||
},
|
||||
{
|
||||
name: "Store Key without /certificates prefix",
|
||||
key: "/other/path/data.txt",
|
||||
value: []byte("test-data3"),
|
||||
expected: map[string]string{fastHash([]byte("/other/path/data.txt")): `{"k":"/other/path/data.txt","v":"dGVzdC1kYXRhMw=="}`},
|
||||
expectedConfigmapName: "higress-cert-store-default",
|
||||
shouldError: false,
|
||||
},
|
||||
// Add more test cases as needed
|
||||
}
|
||||
|
||||
// Run tests
|
||||
for _, test := range tests {
|
||||
t.Run(test.name, func(t *testing.T) {
|
||||
err := storage.Store(context.Background(), test.key, test.value)
|
||||
if test.shouldError {
|
||||
assert.Error(t, err)
|
||||
} else {
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Check the contents of the ConfigMap after storing
|
||||
configmapName := storage.getConfigmapStoreNameByKey(test.key)
|
||||
cm, err := fakeClient.CoreV1().ConfigMaps(namespace).Get(context.Background(), configmapName, metav1.GetOptions{})
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Check if the data is as expected
|
||||
assert.Equal(t, test.expected, cm.Data)
|
||||
|
||||
// Check if the configmapName is correct
|
||||
assert.Equal(t, test.expectedConfigmapName, configmapName)
|
||||
}
|
||||
})
|
||||
}
|
||||
}
|
||||
|
||||
func TestList(t *testing.T) {
|
||||
// Create a fake client for testing
|
||||
fakeClient := fake.NewSimpleClientset()
|
||||
|
||||
// Create a new ConfigmapStorage instance for testing
|
||||
namespace := "your-namespace"
|
||||
storage, err := NewConfigmapStorage(namespace, fakeClient)
|
||||
assert.NoError(t, err)
|
||||
|
||||
// Store some test data
|
||||
// Store some test data
|
||||
testKeys := []string{
|
||||
"/certificates/issuer1/domain1.crt",
|
||||
"/certificates/issuer1/domain2.crt",
|
||||
"/certificates/issuer1/domain3.crt", // Added another domain for issuer1
|
||||
"/certificates/issuer2/domain4.crt",
|
||||
"/certificates/issuer2/domain5.crt",
|
||||
"/certificates/issuer3/subdomain1/domain6.crt", // Two-level subdirectory under issuer3
|
||||
"/certificates/issuer3/subdomain1/subdomain2/domain7.crt", // Two more levels under issuer3
|
||||
"/other-prefix/key1/file1",
|
||||
"/other-prefix/key1/file2",
|
||||
"/other-prefix/key2/file3",
|
||||
"/other-prefix/key2/file4",
|
||||
}
|
||||
|
||||
for _, key := range testKeys {
|
||||
err := storage.Store(context.Background(), key, []byte("test-data"))
|
||||
assert.NoError(t, err)
|
||||
}
|
||||
|
||||
// Define test cases
|
||||
tests := []struct {
|
||||
name string
|
||||
prefix string
|
||||
recursive bool
|
||||
expected []string
|
||||
}{
|
||||
{
|
||||
name: "List Certificates (Non-Recursive)",
|
||||
prefix: "/certificates",
|
||||
recursive: false,
|
||||
expected: []string{"/certificates/issuer1", "/certificates/issuer2", "/certificates/issuer3"},
|
||||
},
|
||||
{
|
||||
name: "List Certificates (Recursive)",
|
||||
prefix: "/certificates",
|
||||
recursive: true,
|
||||
expected: []string{"/certificates/issuer1/domain1.crt", "/certificates/issuer1/domain2.crt", "/certificates/issuer1/domain3.crt", "/certificates/issuer2/domain4.crt", "/certificates/issuer2/domain5.crt", "/certificates/issuer3/subdomain1/domain6.crt", "/certificates/issuer3/subdomain1/subdomain2/domain7.crt"},
|
||||
},
|
||||
{
|
||||
name: "List Other Prefix (Non-Recursive)",
|
||||
prefix: "/other-prefix",
|
||||
recursive: false,
|
||||
expected: []string{"/other-prefix/key1", "/other-prefix/key2"},
|
||||
},
|
||||
|
||||
{
|
||||
name: "List Other Prefix (Non-Recursive)",
|
||||
prefix: "/other-prefix/key1",
|
||||
recursive: false,
|
||||
expected: []string{"/other-prefix/key1/file1", "/other-prefix/key1/file2"},
|
||||
},
|
||||
{
|
||||
name: "List Other Prefix (Recursive)",
|
||||
prefix: "/other-prefix",
|
||||
recursive: true,
|
||||
expected: []string{"/other-prefix/key1/file1", "/other-prefix/key1/file2", "/other-prefix/key2/file3", "/other-prefix/key2/file4"},
|
||||
},
|
||||
}
|
||||
|
||||
// Run tests
|
||||
for _, test := range tests {
|
||||
t.Run(test.name, func(t *testing.T) {
|
||||
keys, err := storage.List(context.Background(), test.prefix, test.recursive)
|
||||
assert.NoError(t, err)
|
||||
assert.ElementsMatch(t, test.expected, keys)
|
||||
})
|
||||
}
|
||||
}
|
||||
97
pkg/cert/util.go
Normal file
97
pkg/cert/util.go
Normal file
@@ -0,0 +1,97 @@
|
||||
// Copyright (c) 2022 Alibaba Group Holding Ltd.
|
||||
//
|
||||
// Licensed under the Apache License, Version 2.0 (the "License");
|
||||
// you may not use this file except in compliance with the License.
|
||||
// You may obtain a copy of the License at
|
||||
//
|
||||
// http://www.apache.org/licenses/LICENSE-2.0
|
||||
//
|
||||
// Unless required by applicable law or agreed to in writing, software
|
||||
// distributed under the License is distributed on an "AS IS" BASIS,
|
||||
// WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
|
||||
// See the License for the specific language governing permissions and
|
||||
// limitations under the License.
|
||||
|
||||
package cert
|
||||
|
||||
import (
|
||||
"crypto/x509"
|
||||
"encoding/pem"
|
||||
"fmt"
|
||||
"hash/fnv"
|
||||
"math/rand"
|
||||
"net"
|
||||
"regexp"
|
||||
"time"
|
||||
)
|
||||
|
||||
// parseCertsFromPEMBundle parses a certificate bundle from top to bottom and returns
|
||||
// a slice of x509 certificates. This function will error if no certificates are found.
|
||||
func parseCertsFromPEMBundle(bundle []byte) ([]*x509.Certificate, error) {
|
||||
var certificates []*x509.Certificate
|
||||
var certDERBlock *pem.Block
|
||||
for {
|
||||
certDERBlock, bundle = pem.Decode(bundle)
|
||||
if certDERBlock == nil {
|
||||
break
|
||||
}
|
||||
if certDERBlock.Type == "CERTIFICATE" {
|
||||
cert, err := x509.ParseCertificate(certDERBlock.Bytes)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
certificates = append(certificates, cert)
|
||||
}
|
||||
}
|
||||
if len(certificates) == 0 {
|
||||
return nil, fmt.Errorf("no certificates found in bundle")
|
||||
}
|
||||
return certificates, nil
|
||||
}
|
||||
|
||||
func notAfter(cert *x509.Certificate) time.Time {
|
||||
if cert == nil {
|
||||
return time.Time{}
|
||||
}
|
||||
return cert.NotAfter.Truncate(time.Second).Add(1 * time.Second)
|
||||
}
|
||||
|
||||
func notBefore(cert *x509.Certificate) time.Time {
|
||||
if cert == nil {
|
||||
return time.Time{}
|
||||
}
|
||||
return cert.NotBefore.Truncate(time.Second).Add(1 * time.Second)
|
||||
}
|
||||
|
||||
// hostOnly returns only the host portion of hostport.
|
||||
// If there is no port or if there is an error splitting
|
||||
// the port off, the whole input string is returned.
|
||||
func hostOnly(hostport string) string {
|
||||
host, _, err := net.SplitHostPort(hostport)
|
||||
if err != nil {
|
||||
return hostport // OK; probably had no port to begin with
|
||||
}
|
||||
return host
|
||||
}
|
||||
|
||||
func rangeRandom(min, max int) (number int) {
|
||||
r := rand.New(rand.NewSource(time.Now().UnixNano()))
|
||||
number = r.Intn(max-min) + min
|
||||
return number
|
||||
}
|
||||
|
||||
func ValidateEmail(email string) bool {
|
||||
pattern := `^[a-zA-Z0-9._%+\-]+@[a-zA-Z0-9.\-]+\.[a-zA-Z]{2,}$`
|
||||
regExp := regexp.MustCompile(pattern)
|
||||
if regExp.MatchString(email) {
|
||||
return true
|
||||
} else {
|
||||
return false
|
||||
}
|
||||
}
|
||||
|
||||
func fastHash(input []byte) string {
|
||||
h := fnv.New32a()
|
||||
h.Write(input)
|
||||
return fmt.Sprintf("%x", h.Sum32())
|
||||
}
|
||||
@@ -24,14 +24,13 @@ import (
|
||||
"runtime"
|
||||
"strings"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cmd/hgctl/kubernetes"
|
||||
"github.com/alibaba/higress/pkg/cmd/options"
|
||||
"github.com/docker/cli/cli/command"
|
||||
"github.com/docker/cli/cli/flags"
|
||||
types2 "github.com/docker/docker/api/types"
|
||||
"github.com/pkg/errors"
|
||||
"github.com/spf13/cobra"
|
||||
"k8s.io/apimachinery/pkg/types"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cmd/hgctl/docker"
|
||||
"github.com/alibaba/higress/pkg/cmd/hgctl/kubernetes"
|
||||
"github.com/alibaba/higress/pkg/cmd/options"
|
||||
)
|
||||
|
||||
var (
|
||||
@@ -55,7 +54,9 @@ var (
|
||||
|
||||
proxyAdminPort int
|
||||
|
||||
docker = false
|
||||
project = "higress"
|
||||
|
||||
dockerCli = false
|
||||
)
|
||||
|
||||
const (
|
||||
@@ -107,7 +108,7 @@ func newDashboardCmd() *cobra.Command {
|
||||
|
||||
consoleCmd := consoleDashCmd()
|
||||
consoleCmd.PersistentFlags().IntVar(&consolePort, "ui-port", defaultConsolePort, "The component dashboard UI port.")
|
||||
consoleCmd.PersistentFlags().BoolVar(&docker, "docker", false, "Search higress console from docker")
|
||||
consoleCmd.PersistentFlags().BoolVar(&dockerCli, "docker", false, "Search higress console from docker")
|
||||
dashboardCmd.AddCommand(consoleCmd)
|
||||
|
||||
controllerDebugCmd := controllerDebugCmd()
|
||||
@@ -165,23 +166,23 @@ func consoleDashCmd() *cobra.Command {
|
||||
hgctl dash console
|
||||
hgctl d console`,
|
||||
RunE: func(cmd *cobra.Command, args []string) error {
|
||||
if docker {
|
||||
return accessDocker(cmd)
|
||||
if dockerCli {
|
||||
return accessDockerCompose(cmd)
|
||||
}
|
||||
client, err := kubernetes.NewCLIClient(options.DefaultConfigFlags.ToRawKubeConfigLoader())
|
||||
if err != nil {
|
||||
fmt.Printf("build kubernetes CLI client fail: %v\ntry to access docker container\n", err)
|
||||
return accessDocker(cmd)
|
||||
return accessDockerCompose(cmd)
|
||||
}
|
||||
pl, err := client.PodsForSelector(addonNamespace, "app.kubernetes.io/name=higress-console")
|
||||
if err != nil {
|
||||
fmt.Printf("build kubernetes CLI client fail: %v\ntry to access docker container\n", err)
|
||||
return accessDocker(cmd)
|
||||
return accessDockerCompose(cmd)
|
||||
}
|
||||
|
||||
if len(pl.Items) < 1 {
|
||||
fmt.Printf("no higress console pods found\ntry to access docker container\n")
|
||||
return accessDocker(cmd)
|
||||
return accessDockerCompose(cmd)
|
||||
}
|
||||
|
||||
// only use the first pod in the list
|
||||
@@ -193,27 +194,26 @@ func consoleDashCmd() *cobra.Command {
|
||||
return cmd
|
||||
}
|
||||
|
||||
// accessDocker access docker container
|
||||
func accessDocker(cmd *cobra.Command) error {
|
||||
dockerCli, err := command.NewDockerCli(command.WithCombinedStreams(os.Stdout))
|
||||
// accessDockerCompose access docker compose ps
|
||||
func accessDockerCompose(cmd *cobra.Command) error {
|
||||
cli, err := docker.NewCompose(cmd.OutOrStdout())
|
||||
if err != nil {
|
||||
return fmt.Errorf("build docker CLI client fail: %w", err)
|
||||
return errors.Wrap(err, "failed to build the docker compose client")
|
||||
}
|
||||
err = dockerCli.Initialize(flags.NewClientOptions())
|
||||
|
||||
list, err := cli.Ps(context.TODO(), project)
|
||||
if err != nil {
|
||||
return fmt.Errorf("docker client initialize fail: %w", err)
|
||||
return errors.Wrap(err, "failed to build the docker compose ps")
|
||||
}
|
||||
apiClient := dockerCli.Client()
|
||||
list, err := apiClient.ContainerList(context.Background(), types2.ContainerListOptions{})
|
||||
for _, container := range list {
|
||||
for i, name := range container.Names {
|
||||
if strings.Contains(name, "higress-console") {
|
||||
port := container.Ports[i].PublicPort
|
||||
// not support define ip address
|
||||
url := fmt.Sprintf("http://localhost:%d", port)
|
||||
if strings.Contains(container.Service, "console") {
|
||||
// not support define ip address
|
||||
if container.Publishers != nil {
|
||||
url := fmt.Sprintf("http://localhost:%d", container.Publishers[0].PublishedPort)
|
||||
openBrowser(url, cmd.OutOrStdout(), browser)
|
||||
return nil
|
||||
}
|
||||
|
||||
return nil
|
||||
}
|
||||
}
|
||||
return errors.New("no higress console container found")
|
||||
|
||||
@@ -109,3 +109,7 @@ func (c Compose) List(ctx context.Context) ([]api.Stack, error) {
|
||||
func (c Compose) Down(ctx context.Context, name string) error {
|
||||
return c.client.Down(ctx, name, api.DownOptions{})
|
||||
}
|
||||
|
||||
func (c Compose) Ps(ctx context.Context, name string) ([]api.ContainerSummary, error) {
|
||||
return c.client.Ps(ctx, name, api.PsOptions{})
|
||||
}
|
||||
|
||||
@@ -17,6 +17,7 @@ package helm
|
||||
import (
|
||||
"errors"
|
||||
"fmt"
|
||||
"regexp"
|
||||
"strings"
|
||||
|
||||
"istio.io/istio/operator/pkg/util"
|
||||
@@ -84,9 +85,10 @@ func (p ProfileGlobal) Validate(install InstallMode) []error {
|
||||
}
|
||||
|
||||
type ProfileConsole struct {
|
||||
Port uint32 `json:"port,omitempty"`
|
||||
Replicas uint32 `json:"replicas,omitempty"`
|
||||
O11yEnabled bool `json:"o11YEnabled,omitempty"`
|
||||
Port uint32 `json:"port,omitempty"`
|
||||
Replicas uint32 `json:"replicas,omitempty"`
|
||||
O11yEnabled bool `json:"o11YEnabled,omitempty"`
|
||||
Resources Resource `json:"resources,omitempty"`
|
||||
}
|
||||
|
||||
func (p ProfileConsole) SetFlags(install InstallMode) ([]string, error) {
|
||||
@@ -112,14 +114,31 @@ func (p ProfileConsole) Validate(install InstallMode) []error {
|
||||
}
|
||||
}
|
||||
|
||||
// set default value
|
||||
if p.Resources.Requests.CPU == "" {
|
||||
p.Resources.Requests.CPU = "250m"
|
||||
}
|
||||
if p.Resources.Requests.Memory == "" {
|
||||
p.Resources.Requests.Memory = "512Mi"
|
||||
}
|
||||
if p.Resources.Limits.CPU == "" {
|
||||
p.Resources.Limits.CPU = "2000m"
|
||||
}
|
||||
if p.Resources.Limits.Memory == "" {
|
||||
p.Resources.Limits.Memory = "2048Mi"
|
||||
}
|
||||
|
||||
errs = append(errs, p.Resources.Validate()...)
|
||||
|
||||
return errs
|
||||
}
|
||||
|
||||
type ProfileGateway struct {
|
||||
Replicas uint32 `json:"replicas,omitempty"`
|
||||
HttpPort uint32 `json:"httpPort,omitempty"`
|
||||
HttpsPort uint32 `json:"httpsPort,omitempty"`
|
||||
MetricsPort uint32 `json:"metricsPort,omitempty"`
|
||||
Replicas uint32 `json:"replicas,omitempty"`
|
||||
HttpPort uint32 `json:"httpPort,omitempty"`
|
||||
HttpsPort uint32 `json:"httpsPort,omitempty"`
|
||||
MetricsPort uint32 `json:"metricsPort,omitempty"`
|
||||
Resources Resource `json:"resources,omitempty"`
|
||||
}
|
||||
|
||||
func (p ProfileGateway) SetFlags(install InstallMode) ([]string, error) {
|
||||
@@ -149,11 +168,29 @@ func (p ProfileGateway) Validate(install InstallMode) []error {
|
||||
errs = append(errs, errors.New("gateway.MetricsPort need be large than zero"))
|
||||
}
|
||||
}
|
||||
|
||||
// set default value
|
||||
if p.Resources.Requests.CPU == "" {
|
||||
p.Resources.Requests.CPU = "2000m"
|
||||
}
|
||||
if p.Resources.Requests.Memory == "" {
|
||||
p.Resources.Requests.Memory = "2048Mi"
|
||||
}
|
||||
if p.Resources.Limits.CPU == "" {
|
||||
p.Resources.Limits.CPU = "2000m"
|
||||
}
|
||||
if p.Resources.Limits.Memory == "" {
|
||||
p.Resources.Limits.Memory = "2048Mi"
|
||||
}
|
||||
|
||||
errs = append(errs, p.Resources.Validate()...)
|
||||
|
||||
return errs
|
||||
}
|
||||
|
||||
type ProfileController struct {
|
||||
Replicas uint32 `json:"replicas,omitempty"`
|
||||
Replicas uint32 `json:"replicas,omitempty"`
|
||||
Resources Resource `json:"resources,omitempty"`
|
||||
}
|
||||
|
||||
func (p ProfileController) SetFlags(install InstallMode) ([]string, error) {
|
||||
@@ -171,6 +208,23 @@ func (p ProfileController) Validate(install InstallMode) []error {
|
||||
errs = append(errs, errors.New("controller.replica need be large than zero"))
|
||||
}
|
||||
}
|
||||
|
||||
// set default value
|
||||
if p.Resources.Requests.CPU == "" {
|
||||
p.Resources.Requests.CPU = "500m"
|
||||
}
|
||||
if p.Resources.Requests.Memory == "" {
|
||||
p.Resources.Requests.Memory = "2048Mi"
|
||||
}
|
||||
if p.Resources.Limits.CPU == "" {
|
||||
p.Resources.Limits.CPU = "1000m"
|
||||
}
|
||||
if p.Resources.Limits.Memory == "" {
|
||||
p.Resources.Limits.Memory = "2048Mi"
|
||||
}
|
||||
|
||||
errs = append(errs, p.Resources.Validate()...)
|
||||
|
||||
return errs
|
||||
}
|
||||
|
||||
@@ -248,14 +302,62 @@ func (p *Profile) ValuesYaml() (string, error) {
|
||||
setFlags = append(setFlags, controllerFlags...)
|
||||
|
||||
valueOverlayYAML := ""
|
||||
if p.Values != nil {
|
||||
out, err := yaml.Marshal(p.Values)
|
||||
if err != nil {
|
||||
return "", err
|
||||
}
|
||||
valueOverlayYAML = string(out)
|
||||
if p.Values == nil {
|
||||
p.Values = make(map[string]any)
|
||||
}
|
||||
|
||||
resourceMap := make(map[string]any)
|
||||
resourceMap["higress-core"] = map[string]interface{}{
|
||||
"controller": map[string]interface{}{
|
||||
"resources": map[string]interface{}{
|
||||
"requests": map[string]interface{}{
|
||||
"cpu": p.Controller.Resources.Requests.CPU,
|
||||
"memory": p.Controller.Resources.Requests.Memory,
|
||||
},
|
||||
"limits": map[string]interface{}{
|
||||
"cpu": p.Controller.Resources.Limits.CPU,
|
||||
"memory": p.Controller.Resources.Limits.Memory,
|
||||
},
|
||||
},
|
||||
},
|
||||
"gateway": map[string]interface{}{
|
||||
"resources": map[string]interface{}{
|
||||
"requests": map[string]interface{}{
|
||||
"cpu": p.Gateway.Resources.Requests.CPU,
|
||||
"memory": p.Gateway.Resources.Requests.Memory,
|
||||
},
|
||||
"limits": map[string]interface{}{
|
||||
"cpu": p.Gateway.Resources.Limits.CPU,
|
||||
"memory": p.Gateway.Resources.Limits.Memory,
|
||||
},
|
||||
},
|
||||
},
|
||||
}
|
||||
resourceMap["higress-console"] = map[string]interface{}{
|
||||
"resources": map[string]interface{}{
|
||||
"requests": map[string]interface{}{
|
||||
"cpu": p.Console.Resources.Requests.CPU,
|
||||
"memory": p.Console.Resources.Requests.Memory,
|
||||
},
|
||||
"limits": map[string]interface{}{
|
||||
"cpu": p.Console.Resources.Limits.CPU,
|
||||
"memory": p.Console.Resources.Limits.Memory,
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
resourceYAML, err := yaml.Marshal(resourceMap)
|
||||
if err != nil {
|
||||
return "", err
|
||||
}
|
||||
|
||||
out, err := yaml.Marshal(p.Values)
|
||||
if err != nil {
|
||||
return "", err
|
||||
}
|
||||
|
||||
valueOverlayYAML, err = util.OverlayYAML(string(resourceYAML), string(out))
|
||||
|
||||
flagsYAML, err := overlaySetFlagValues("", setFlags)
|
||||
if err != nil {
|
||||
return "", err
|
||||
@@ -343,3 +445,54 @@ func ToString(errors []error, separator string) string {
|
||||
}
|
||||
return out
|
||||
}
|
||||
|
||||
type Resource struct {
|
||||
Requests Requests `json:"requests,omitempty"`
|
||||
Limits Limits `json:"limits,omitempty"`
|
||||
}
|
||||
|
||||
type Requests struct {
|
||||
CPU string `json:"cpu,omitempty"`
|
||||
Memory string `json:"memory,omitempty"`
|
||||
}
|
||||
|
||||
type Limits struct {
|
||||
CPU string `json:"cpu,omitempty"`
|
||||
Memory string `json:"memory,omitempty"`
|
||||
}
|
||||
|
||||
func (r Resource) Validate() []error {
|
||||
errs := make([]error, 0)
|
||||
|
||||
r.Requests.CPU = strings.ReplaceAll(r.Requests.CPU, " ", "")
|
||||
r.Requests.Memory = strings.ReplaceAll(r.Requests.Memory, " ", "")
|
||||
r.Limits.CPU = strings.ReplaceAll(r.Limits.CPU, " ", "")
|
||||
r.Limits.Memory = strings.ReplaceAll(r.Limits.Memory, " ", "")
|
||||
|
||||
if !isValidK8SResourceFormat(r.Requests.CPU) {
|
||||
errs = append(errs, fmt.Errorf("requests CPU has invalid format"))
|
||||
}
|
||||
if !isValidK8SResourceFormat(r.Requests.Memory) {
|
||||
errs = append(errs, fmt.Errorf("requests memory has invalid format"))
|
||||
}
|
||||
if !isValidK8SResourceFormat(r.Limits.CPU) {
|
||||
errs = append(errs, fmt.Errorf("limits CPU has invalid format"))
|
||||
}
|
||||
if !isValidK8SResourceFormat(r.Limits.Memory) {
|
||||
errs = append(errs, fmt.Errorf("limits memory has invalid format"))
|
||||
}
|
||||
return errs
|
||||
}
|
||||
|
||||
func isValidK8SResourceFormat(resource string) bool {
|
||||
pattern := `^\d+((n|u|m|k|Ki|M|Mi|G|Gi|T|Ti|P|Pi|E|Ei)?)$`
|
||||
match, _ := regexp.MatchString(pattern, resource)
|
||||
if !match {
|
||||
return false
|
||||
}
|
||||
|
||||
if len(resource) == 0 || resource[0] == '-' || resource[0] == '0' {
|
||||
return false
|
||||
}
|
||||
return true
|
||||
}
|
||||
|
||||
@@ -584,7 +584,7 @@ func locateChart(cpOpts *action.ChartPathOptions, name string, settings *cli.Env
|
||||
return fileAbsPath, nil
|
||||
}
|
||||
|
||||
func ParseLatestVersion(repoUrl string, version string) (string, error) {
|
||||
func ParseLatestVersion(repoUrl string, version string, devel bool) (string, error) {
|
||||
|
||||
cpOpts := &action.ChartPathOptions{
|
||||
RepoURL: repoUrl,
|
||||
@@ -632,7 +632,16 @@ func ParseLatestVersion(repoUrl string, version string) (string, error) {
|
||||
|
||||
// get higress helm chart latest version
|
||||
if entries, ok := indexFile.Entries[RepoChartIndexYamlHigressIndex]; ok {
|
||||
return entries[0].AppVersion, nil
|
||||
if devel {
|
||||
return entries[0].AppVersion, nil
|
||||
}
|
||||
|
||||
if chatVersion, err := indexFile.Get(RepoChartIndexYamlHigressIndex, ""); err != nil {
|
||||
return "", errors.New("can't find higress latest version")
|
||||
} else {
|
||||
return chatVersion.Version, nil
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
return "", errors.New("can't find higress latest version")
|
||||
|
||||
@@ -52,6 +52,8 @@ type InstallArgs struct {
|
||||
Set []string
|
||||
// ManifestsPath is a path to a ManifestsPath and profiles directory in the local filesystem with a release tgz.
|
||||
ManifestsPath string
|
||||
// Devel if set true when version is latest, it will get latest version, otherwise it will get latest stable version
|
||||
Devel bool
|
||||
}
|
||||
|
||||
func (a *InstallArgs) String() string {
|
||||
@@ -67,6 +69,7 @@ func addInstallFlags(cmd *cobra.Command, args *InstallArgs) {
|
||||
cmd.PersistentFlags().StringSliceVarP(&args.InFilenames, "filename", "f", nil, filenameFlagHelpStr)
|
||||
cmd.PersistentFlags().StringArrayVarP(&args.Set, "set", "s", nil, setFlagHelpStr)
|
||||
cmd.PersistentFlags().StringVarP(&args.ManifestsPath, "manifests", "d", "", manifestsFlagHelpStr)
|
||||
cmd.PersistentFlags().BoolVar(&args.Devel, "devel", false, "use development versions (alpha, beta, and release candidate releases), If version is set, this is ignored")
|
||||
}
|
||||
|
||||
// --manifests is an alias for --set installPackagePath=
|
||||
@@ -141,7 +144,7 @@ func install(writer io.Writer, iArgs *InstallArgs) error {
|
||||
return err
|
||||
}
|
||||
|
||||
err = installManifests(profile, writer)
|
||||
err = installManifests(profile, writer, iArgs.Devel)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to install manifests: %v", err)
|
||||
}
|
||||
@@ -192,8 +195,8 @@ func promptProfileName(writer io.Writer) string {
|
||||
|
||||
}
|
||||
|
||||
func installManifests(profile *helm.Profile, writer io.Writer) error {
|
||||
installer, err := installer.NewInstaller(profile, writer, false)
|
||||
func installManifests(profile *helm.Profile, writer io.Writer, devel bool) error {
|
||||
installer, err := installer.NewInstaller(profile, writer, false, devel, installer.InstallInstallerMode)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
@@ -52,6 +52,8 @@ type ComponentOptions struct {
|
||||
Quiet bool
|
||||
// Capabilities
|
||||
Capabilities *chartutil.Capabilities
|
||||
// devel
|
||||
Devel bool
|
||||
}
|
||||
|
||||
type ComponentOption func(*ComponentOptions)
|
||||
@@ -98,6 +100,12 @@ func WithQuiet() ComponentOption {
|
||||
}
|
||||
}
|
||||
|
||||
func WithDevel(devel bool) ComponentOption {
|
||||
return func(opts *ComponentOptions) {
|
||||
opts.Devel = devel
|
||||
}
|
||||
}
|
||||
|
||||
func renderComponentManifest(spec any, renderer helm.Renderer, addOn bool, name ComponentName, namespace string) (string, error) {
|
||||
var valsBytes []byte
|
||||
var valsYaml string
|
||||
|
||||
@@ -52,7 +52,7 @@ func (h *HigressComponent) Run() error {
|
||||
// Parse latest version
|
||||
if h.opts.Version == helm.RepoLatestVersion {
|
||||
|
||||
latestVersion, err := helm.ParseLatestVersion(h.opts.RepoURL, h.opts.Version)
|
||||
latestVersion, err := helm.ParseLatestVersion(h.opts.RepoURL, h.opts.Version, h.opts.Devel)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
@@ -28,6 +28,8 @@ import (
|
||||
"k8s.io/client-go/util/homedir"
|
||||
)
|
||||
|
||||
type InstallerMode int32
|
||||
|
||||
const (
|
||||
HgctlHomeDirPath = ".hgctl"
|
||||
StandaloneInstalledPath = "higress-standalone"
|
||||
@@ -37,20 +39,26 @@ const (
|
||||
DefaultIstioNamespace = "istio-system"
|
||||
)
|
||||
|
||||
const (
|
||||
InstallInstallerMode InstallerMode = iota
|
||||
UpgradeInstallerMode
|
||||
UninstallInstallerMode
|
||||
)
|
||||
|
||||
type Installer interface {
|
||||
Install() error
|
||||
UnInstall() error
|
||||
Upgrade() error
|
||||
}
|
||||
|
||||
func NewInstaller(profile *helm.Profile, writer io.Writer, quiet bool) (Installer, error) {
|
||||
func NewInstaller(profile *helm.Profile, writer io.Writer, quiet bool, devel bool, installerMode InstallerMode) (Installer, error) {
|
||||
switch profile.Global.Install {
|
||||
case helm.InstallK8s, helm.InstallLocalK8s:
|
||||
cliClient, err := kubernetes.NewCLIClient(options.DefaultConfigFlags.ToRawKubeConfigLoader())
|
||||
if err != nil {
|
||||
return nil, fmt.Errorf("failed to build kubernetes client: %w", err)
|
||||
}
|
||||
installer, err := NewK8sInstaller(profile, cliClient, writer, quiet)
|
||||
installer, err := NewK8sInstaller(profile, cliClient, writer, quiet, devel, installerMode)
|
||||
return installer, err
|
||||
case helm.InstallLocalDocker:
|
||||
installer, err := NewDockerInstaller(profile, writer, quiet)
|
||||
|
||||
@@ -254,7 +254,7 @@ func (o *K8sInstaller) isNamespacedObject(obj *object.K8sObject) bool {
|
||||
return false
|
||||
}
|
||||
|
||||
func NewK8sInstaller(profile *helm.Profile, cli kubernetes.CLIClient, writer io.Writer, quiet bool) (*K8sInstaller, error) {
|
||||
func NewK8sInstaller(profile *helm.Profile, cli kubernetes.CLIClient, writer io.Writer, quiet bool, devel bool, installerMode InstallerMode) (*K8sInstaller, error) {
|
||||
if profile == nil {
|
||||
return nil, errors.New("install profile is empty")
|
||||
}
|
||||
@@ -267,14 +267,20 @@ func NewK8sInstaller(profile *helm.Profile, cli kubernetes.CLIClient, writer io.
|
||||
}
|
||||
fmt.Fprintf(writer, "%s\n", capabilities.KubeVersion.Version)
|
||||
// initialize components
|
||||
higressVersion := profile.Charts.Higress.Version
|
||||
if installerMode == UninstallInstallerMode {
|
||||
// uninstall
|
||||
higressVersion = profile.HigressVersion
|
||||
}
|
||||
components := make(map[ComponentName]Component)
|
||||
opts := []ComponentOption{
|
||||
WithComponentNamespace(profile.Global.Namespace),
|
||||
WithComponentChartPath(profile.InstallPackagePath),
|
||||
WithComponentVersion(profile.Charts.Higress.Version),
|
||||
WithComponentVersion(higressVersion),
|
||||
WithComponentRepoURL(profile.Charts.Higress.Url),
|
||||
WithComponentChartName(profile.Charts.Higress.Name),
|
||||
WithComponentCapabilities(capabilities),
|
||||
WithDevel(devel),
|
||||
}
|
||||
if quiet {
|
||||
opts = append(opts, WithQuiet())
|
||||
|
||||
@@ -37,6 +37,8 @@ type ManifestArgs struct {
|
||||
Set []string
|
||||
// ManifestsPath is a path to a ManifestsPath and profiles directory in the local filesystem with a release tgz.
|
||||
ManifestsPath string
|
||||
// Devel if set true when version is latest, it will get latest version, otherwise it will get latest stable version
|
||||
Devel bool
|
||||
}
|
||||
|
||||
func (a *ManifestArgs) String() string {
|
||||
@@ -70,6 +72,7 @@ func addManifestFlags(cmd *cobra.Command, args *ManifestArgs) {
|
||||
cmd.PersistentFlags().StringSliceVarP(&args.InFilenames, "filename", "f", nil, filenameFlagHelpStr)
|
||||
cmd.PersistentFlags().StringArrayVarP(&args.Set, "set", "s", nil, setFlagHelpStr)
|
||||
cmd.PersistentFlags().StringVarP(&args.ManifestsPath, "manifests", "d", "", manifestsFlagHelpStr)
|
||||
cmd.PersistentFlags().BoolVar(&args.Devel, "devel", false, "use development versions (alpha, beta, and release candidate releases), If version is set, this is ignored")
|
||||
}
|
||||
|
||||
// newManifestGenerateCmd generates a higress install manifest and applies it to a cluster
|
||||
@@ -113,20 +116,20 @@ func generate(writer io.Writer, iArgs *ManifestArgs) error {
|
||||
return err
|
||||
}
|
||||
|
||||
err = genManifests(profile, writer)
|
||||
err = genManifests(profile, writer, iArgs.Devel)
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to install manifests: %v", err)
|
||||
}
|
||||
return nil
|
||||
}
|
||||
|
||||
func genManifests(profile *helm.Profile, writer io.Writer) error {
|
||||
func genManifests(profile *helm.Profile, writer io.Writer, devel bool) error {
|
||||
cliClient, err := kubernetes.NewCLIClient(options.DefaultConfigFlags.ToRawKubeConfigLoader())
|
||||
if err != nil {
|
||||
return fmt.Errorf("failed to build kubernetes client: %w", err)
|
||||
}
|
||||
|
||||
op, err := installer.NewK8sInstaller(profile, cliClient, writer, true)
|
||||
op, err := installer.NewK8sInstaller(profile, cliClient, writer, true, devel, installer.InstallInstallerMode)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
@@ -10,15 +10,36 @@ console:
|
||||
port: 8080
|
||||
replicas: 1
|
||||
o11yEnabled: false
|
||||
resources:
|
||||
requests:
|
||||
cpu: 250m
|
||||
memory: 512Mi
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
|
||||
gateway:
|
||||
replicas: 1
|
||||
httpPort: 80
|
||||
httpsPort: 443
|
||||
metricsPort: 15020
|
||||
resources:
|
||||
requests:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
|
||||
controller:
|
||||
replicas: 1
|
||||
resources:
|
||||
requests:
|
||||
cpu: 500m
|
||||
memory: 2048Mi
|
||||
limits:
|
||||
cpu: 1000m
|
||||
memory: 2048Mi
|
||||
|
||||
storage:
|
||||
url: nacos://127.0.0.1:8848 # file://opt/higress/conf
|
||||
|
||||
@@ -9,12 +9,33 @@ global:
|
||||
console:
|
||||
replicas: 1
|
||||
o11yEnabled: false
|
||||
resources:
|
||||
requests:
|
||||
cpu: 250m
|
||||
memory: 512Mi
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
|
||||
gateway:
|
||||
replicas: 2
|
||||
resources:
|
||||
requests:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
|
||||
controller:
|
||||
replicas: 1
|
||||
resources:
|
||||
requests:
|
||||
cpu: 500m
|
||||
memory: 2048Mi
|
||||
limits:
|
||||
cpu: 1000m
|
||||
memory: 2048Mi
|
||||
|
||||
# values passed through to helm
|
||||
values:
|
||||
|
||||
@@ -9,12 +9,33 @@ global:
|
||||
console:
|
||||
replicas: 1
|
||||
o11yEnabled: true
|
||||
resources:
|
||||
requests:
|
||||
cpu: 250m
|
||||
memory: 512Mi
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
|
||||
gateway:
|
||||
replicas: 1
|
||||
resources:
|
||||
requests:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
limits:
|
||||
cpu: 2000m
|
||||
memory: 2048Mi
|
||||
|
||||
controller:
|
||||
replicas: 1
|
||||
resources:
|
||||
requests:
|
||||
cpu: 500m
|
||||
memory: 2048Mi
|
||||
limits:
|
||||
cpu: 1000m
|
||||
memory: 2048Mi
|
||||
|
||||
# values passed through to helm
|
||||
values:
|
||||
|
||||
@@ -18,6 +18,7 @@ import (
|
||||
"fmt"
|
||||
"io"
|
||||
"os"
|
||||
"os/exec"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cmd/hgctl/plugin/option"
|
||||
"github.com/alibaba/higress/pkg/cmd/hgctl/plugin/utils"
|
||||
@@ -86,6 +87,12 @@ func runInit(w io.Writer, target string) (err error) {
|
||||
return errors.Wrap(err, "failed to create option.yaml")
|
||||
}
|
||||
|
||||
cmd := exec.Command("go", "mod", "tidy")
|
||||
cmd.Dir = dir
|
||||
if err := cmd.Run(); err != nil {
|
||||
return errors.Wrap(err, "failed to run go mod tidy")
|
||||
}
|
||||
|
||||
fmt.Fprintf(w, "Initialized the project in %q\n", dir)
|
||||
|
||||
return nil
|
||||
|
||||
@@ -31,8 +31,8 @@ package main
|
||||
|
||||
import (
|
||||
"github.com/tidwall/gjson"
|
||||
"github.com/tetratelabs/proxy-wasm-go-sdk/proxywasm"
|
||||
"github.com/tetratelabs/proxy-wasm-go-sdk/proxywasm/types"
|
||||
"github.com/higress-group/proxy-wasm-go-sdk/proxywasm"
|
||||
"github.com/higress-group/proxy-wasm-go-sdk/proxywasm/types"
|
||||
"github.com/alibaba/higress/plugins/wasm-go/pkg/wrapper"
|
||||
)
|
||||
|
||||
@@ -93,8 +93,8 @@ module {{ .Name }}
|
||||
go 1.19
|
||||
|
||||
require (
|
||||
github.com/alibaba/higress/plugins/wasm-go v0.0.0-20231019123123-86b223bc75f1
|
||||
github.com/tetratelabs/proxy-wasm-go-sdk v0.22.0
|
||||
github.com/alibaba/higress/plugins/wasm-go main
|
||||
github.com/higress-group/proxy-wasm-go-sdk main
|
||||
github.com/tidwall/gjson v1.14.3
|
||||
)
|
||||
`
|
||||
|
||||
@@ -75,9 +75,15 @@ static_resources:
|
||||
stat_prefix: ingress_http
|
||||
# Output envoy logs to stdout
|
||||
access_log:
|
||||
- name: envoy.access_loggers.stdout
|
||||
- name: envoy.access_loggers.file
|
||||
filter:
|
||||
not_health_check_filter: {}
|
||||
typed_config:
|
||||
"@type": type.googleapis.com/envoy.extensions.access_loggers.stream.v3.StdoutAccessLog
|
||||
"@type": type.googleapis.com/envoy.extensions.access_loggers.file.v3.FileAccessLog
|
||||
path: /dev/stdout
|
||||
log_format:
|
||||
text_format_source:
|
||||
inline_string: "{\"authority\":\"%REQ(X-ENVOY-ORIGINAL-HOST?:AUTHORITY)%\",\"bytes_received\":\"%BYTES_RECEIVED%\",\"bytes_sent\":\"%BYTES_SENT%\",\"downstream_local_address\":\"%DOWNSTREAM_LOCAL_ADDRESS%\",\"downstream_remote_address\":\"%DOWNSTREAM_REMOTE_ADDRESS%\",\"duration\":\"%DURATION%\",\"istio_policy_status\":\"%DYNAMIC_METADATA(istio.mixer:status)%\",\"method\":\"%REQ(:METHOD)%\",\"path\":\"%REQ(X-ENVOY-ORIGINAL-PATH?:PATH)%\",\"protocol\":\"%PROTOCOL%\",\"request_id\":\"%REQ(X-REQUEST-ID)%\",\"requested_server_name\":\"%REQUESTED_SERVER_NAME%\",\"response_code\":\"%RESPONSE_CODE%\",\"response_flags\":\"%RESPONSE_FLAGS%\",\"route_name\":\"%ROUTE_NAME%\",\"start_time\":\"%START_TIME%\",\"trace_id\":\"%REQ(X-B3-TRACEID)%\",\"upstream_cluster\":\"%UPSTREAM_CLUSTER%\",\"upstream_host\":\"%UPSTREAM_HOST%\",\"upstream_local_address\":\"%UPSTREAM_LOCAL_ADDRESS%\",\"upstream_service_time\":\"%RESP(X-ENVOY-UPSTREAM-SERVICE-TIME)%\",\"upstream_transport_failure_reason\":\"%UPSTREAM_TRANSPORT_FAILURE_REASON%\",\"user_agent\":\"%REQ(USER-AGENT)%\",\"x_forwarded_for\":\"%REQ(X-FORWARDED-FOR)%\"}\n"
|
||||
# Modify as required
|
||||
route_config:
|
||||
name: local_route
|
||||
|
||||
@@ -124,7 +124,7 @@ func (s *JSONSchemaPropsOrBool) UnmarshalJSON(data []byte) error {
|
||||
|
||||
func (s JSONSchemaPropsOrBool) MarshalYAML() (interface{}, error) {
|
||||
if s.Schema != nil {
|
||||
return yaml.Marshal(s.Schema)
|
||||
return s.Schema, nil
|
||||
}
|
||||
|
||||
if s.Schema == nil && !s.Allows {
|
||||
|
||||
@@ -33,7 +33,7 @@ type WasmPluginMeta struct {
|
||||
Spec WasmPluginSpec `json:"spec" yaml:"spec"`
|
||||
}
|
||||
|
||||
func defaultWsamPluginMeta() *WasmPluginMeta {
|
||||
func defaultWasmPluginMeta() *WasmPluginMeta {
|
||||
return &WasmPluginMeta{
|
||||
APIVersion: "1.0.0",
|
||||
Info: WasmPluginInfo{
|
||||
@@ -77,7 +77,7 @@ func ParseGoSrc(dir, model string) (*WasmPluginMeta, error) {
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
meta := defaultWsamPluginMeta()
|
||||
meta := defaultWasmPluginMeta()
|
||||
meta.setByConfigModel(m)
|
||||
return meta, nil
|
||||
}
|
||||
@@ -96,26 +96,33 @@ func recursiveSetSchema(model *Model, parent *JSONSchemaProps) (string, *JSONSch
|
||||
}
|
||||
newName := cur.HandleFieldTags(model.Tag, parent, model.Name)
|
||||
if IsArray(model.Type) {
|
||||
item := NewJSONSchemaProps()
|
||||
item.Type = GetItemType(cur.Type)
|
||||
cur.Type = "array"
|
||||
if IsObject(item.Type) {
|
||||
item.Properties = make(map[string]JSONSchemaProps)
|
||||
for _, field := range model.Fields {
|
||||
name, child := recursiveSetSchema(&field, cur)
|
||||
item.Properties[name] = *child
|
||||
}
|
||||
}
|
||||
cur.Items = &JSONSchemaPropsOrArray{Schema: item}
|
||||
itemModel := &*model
|
||||
itemModel.Type = GetItemType(model.Type)
|
||||
_, itemSchema := recursiveSetSchema(itemModel, nil)
|
||||
cur.Items = &JSONSchemaPropsOrArray{Schema: itemSchema}
|
||||
} else if IsMap(model.Type) {
|
||||
cur.Type = "object"
|
||||
valueModel := &*model
|
||||
valueModel.Type = GetValueType(model.Type)
|
||||
valueModel.Tag = ""
|
||||
valueModel.Doc = ""
|
||||
_, valueSchema := recursiveSetSchema(valueModel, nil)
|
||||
cur.AdditionalProperties = &JSONSchemaPropsOrBool{Schema: valueSchema}
|
||||
} else if IsObject(model.Type) { // type may be `array of object`, and it is handled in the first branch
|
||||
for _, field := range model.Fields {
|
||||
name, child := recursiveSetSchema(&field, cur)
|
||||
cur.Properties[name] = *child
|
||||
}
|
||||
cur.Properties = make(map[string]JSONSchemaProps)
|
||||
recursiveObjectProperties(cur, model)
|
||||
}
|
||||
return newName, cur
|
||||
}
|
||||
|
||||
func recursiveObjectProperties(parent *JSONSchemaProps, model *Model) {
|
||||
for _, field := range model.Fields {
|
||||
name, child := recursiveSetSchema(&field, parent)
|
||||
parent.Properties[name] = *child
|
||||
}
|
||||
}
|
||||
|
||||
func (meta *WasmPluginMeta) setModelAnnotations(comment string) {
|
||||
as := GetAnnotations(comment)
|
||||
for _, a := range as {
|
||||
|
||||
@@ -30,6 +30,7 @@ import (
|
||||
|
||||
const (
|
||||
ArrayPrefix = "array of "
|
||||
MapPrefix = "map of "
|
||||
ObjectSuffix = "object"
|
||||
)
|
||||
|
||||
@@ -40,7 +41,23 @@ func IsArray(typ string) bool {
|
||||
|
||||
// GetItemType returns the item type of array, e.g.: array of int -> int
|
||||
func GetItemType(typ string) string {
|
||||
return strings.TrimPrefix(typ, ArrayPrefix)
|
||||
if !IsArray(typ) {
|
||||
return typ
|
||||
}
|
||||
return typ[len(ArrayPrefix):]
|
||||
}
|
||||
|
||||
// IsMap returns true if the given type is a `map of <type>`
|
||||
func IsMap(typ string) bool {
|
||||
return strings.HasPrefix(typ, MapPrefix)
|
||||
}
|
||||
|
||||
// GetValueType returns the value type of map, e.g.: map of int -> int
|
||||
func GetValueType(typ string) string {
|
||||
if !IsMap(typ) {
|
||||
return typ
|
||||
}
|
||||
return typ[len(MapPrefix):]
|
||||
}
|
||||
|
||||
// IsObject returns true if the given type is an `object` or an `array of object`
|
||||
@@ -50,7 +67,7 @@ func IsObject(typ string) bool {
|
||||
|
||||
var (
|
||||
ErrInvalidModel = errors.New("invalid model")
|
||||
ErrInvalidFiledType = errors.New("invalid field type")
|
||||
ErrInvalidFieldType = errors.New("invalid field type")
|
||||
)
|
||||
|
||||
type ModelParser struct {
|
||||
@@ -248,24 +265,24 @@ func (p *ModelParser) parseModelFields(model string) (fields []Model, err error)
|
||||
if field.Tag != nil {
|
||||
ignore, err := fd.setTag(field.Tag.Value)
|
||||
if err != nil {
|
||||
return nil, errors.Wrapf(err, "failed to parse tag %q of the field %q", fd.Tag, fd.Name)
|
||||
return nil, errors.Wrapf(err, "failed to parse tag %q of the field %q", field.Tag, fd.Name)
|
||||
}
|
||||
if ignore {
|
||||
continue
|
||||
}
|
||||
}
|
||||
fd.Type, err = p.parseFiledType(pkgName, field.Type)
|
||||
fd.Type, err = p.parseFieldType(pkgName, field.Type)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
return nil, errors.Wrapf(err, "failed to parse type %q of the field %q", field.Type, fd.Name)
|
||||
}
|
||||
if IsObject(fd.Type) {
|
||||
subModel, err := p.getModelName(field.Type)
|
||||
subModel, err := p.doGetModelName(pkgName, field.Type)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
return nil, errors.Wrapf(err, "failed to get the sub-model name of the field %q with type %q", fd.Name, field.Type)
|
||||
}
|
||||
fd.Fields, err = p.parseModelFields(subModel)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
return nil, errors.Wrapf(err, "failed to parse sub-model of the field %q with type %q", fd.Name, field.Type)
|
||||
}
|
||||
}
|
||||
fields = append(fields, fd)
|
||||
@@ -313,51 +330,63 @@ func (p *ModelParser) doGetModelName(pkgName string, typ ast.Expr) (string, erro
|
||||
return p.doGetModelName(pkgName, t.X)
|
||||
case *ast.ArrayType: // slice or array
|
||||
return p.doGetModelName(pkgName, t.Elt)
|
||||
case *ast.MapType:
|
||||
return p.doGetModelName(pkgName, t.Value)
|
||||
case *ast.SelectorExpr: // <pkg_name>.<field_name>
|
||||
pkg, ok := t.X.(*ast.Ident)
|
||||
if !ok {
|
||||
return "", ErrInvalidFiledType
|
||||
return "", ErrInvalidFieldType
|
||||
}
|
||||
pName := pkg.Name + "."
|
||||
return p.doGetModelName(pName, t.Sel)
|
||||
case *ast.Ident:
|
||||
return pkgName + t.Name, nil
|
||||
default:
|
||||
return "", ErrInvalidFiledType
|
||||
return "", ErrInvalidFieldType
|
||||
}
|
||||
}
|
||||
|
||||
func (p *ModelParser) parseFiledType(pkgName string, typ ast.Expr) (string, error) {
|
||||
func (p *ModelParser) parseFieldType(pkgName string, typ ast.Expr) (string, error) {
|
||||
switch t := typ.(type) {
|
||||
case *ast.StructType: // nested struct
|
||||
return string(JsonTypeObject), nil
|
||||
case *ast.StarExpr: // *int -> int
|
||||
return p.parseFiledType(pkgName, t.X)
|
||||
return p.parseFieldType(pkgName, t.X)
|
||||
case *ast.ArrayType: // slice or array
|
||||
ret, err := p.parseFiledType(pkgName, t.Elt)
|
||||
ret, err := p.parseFieldType(pkgName, t.Elt)
|
||||
if err != nil {
|
||||
return "", err
|
||||
}
|
||||
return ArrayPrefix + ret, nil
|
||||
case *ast.MapType:
|
||||
if keyIdent, ok := t.Key.(*ast.Ident); !ok {
|
||||
return "", ErrInvalidFieldType
|
||||
} else if keyIdent.Name != "string" {
|
||||
return "", ErrInvalidFieldType
|
||||
} else if ret, err := p.parseFieldType(pkgName, t.Value); err != nil {
|
||||
return "", err
|
||||
} else {
|
||||
return MapPrefix + ret, nil
|
||||
}
|
||||
case *ast.SelectorExpr: // <pkg_name>.<field_name>
|
||||
pkg, ok := t.X.(*ast.Ident)
|
||||
if !ok {
|
||||
return "", ErrInvalidFiledType
|
||||
return "", ErrInvalidFieldType
|
||||
}
|
||||
pName := pkg.Name + "."
|
||||
return p.parseFiledType(pName, t.Sel)
|
||||
return p.parseFieldType(pName, t.Sel)
|
||||
case *ast.Ident:
|
||||
fName := pkgName + t.Name
|
||||
if _, ok := p.structs[fName]; ok {
|
||||
return string(JsonTypeObject), nil
|
||||
}
|
||||
if alias, ok := p.alias[fName]; ok {
|
||||
return p.parseFiledType(pkgName, alias.expr)
|
||||
return p.parseFieldType(pkgName, alias.expr)
|
||||
}
|
||||
jsonType, err := convert2JsonType(t.Name)
|
||||
return string(jsonType), err
|
||||
default:
|
||||
return "", ErrInvalidFiledType
|
||||
return "", ErrInvalidFieldType
|
||||
}
|
||||
}
|
||||
|
||||
@@ -375,7 +404,7 @@ func convert2JsonType(typ string) (JsonType, error) {
|
||||
case "struct":
|
||||
return JsonTypeObject, nil
|
||||
default:
|
||||
return "", ErrInvalidFiledType
|
||||
return "", ErrInvalidFieldType
|
||||
}
|
||||
}
|
||||
|
||||
@@ -388,4 +417,5 @@ const (
|
||||
JsonTypeString JsonType = "string"
|
||||
JsonTypeObject JsonType = "object"
|
||||
JsonTypeArray JsonType = "array"
|
||||
JsonTypeMap JsonType = "map"
|
||||
)
|
||||
|
||||
@@ -126,7 +126,7 @@ func promptUninstall(writer io.Writer) bool {
|
||||
}
|
||||
|
||||
func uninstallManifests(profile *helm.Profile, writer io.Writer, uiArgs *uninstallArgs) error {
|
||||
installer, err := installer.NewInstaller(profile, writer, false)
|
||||
installer, err := installer.NewInstaller(profile, writer, false, false, installer.UninstallInstallerMode)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
@@ -37,6 +37,7 @@ func addUpgradeFlags(cmd *cobra.Command, args *upgradeArgs) {
|
||||
cmd.PersistentFlags().StringSliceVarP(&args.InFilenames, "filename", "f", nil, filenameFlagHelpStr)
|
||||
cmd.PersistentFlags().StringArrayVarP(&args.Set, "set", "s", nil, setFlagHelpStr)
|
||||
cmd.PersistentFlags().StringVarP(&args.ManifestsPath, "manifests", "d", "", manifestsFlagHelpStr)
|
||||
cmd.PersistentFlags().BoolVar(&args.Devel, "devel", false, "use development versions (alpha, beta, and release candidate releases), If version is set, this is ignored")
|
||||
}
|
||||
|
||||
// newUpgradeCmd upgrades Istio control plane in-place with eligibility checks.
|
||||
@@ -91,7 +92,7 @@ func upgrade(writer io.Writer, iArgs *InstallArgs) error {
|
||||
return nil
|
||||
}
|
||||
|
||||
err = upgradeManifests(profile, writer)
|
||||
err = upgradeManifests(profile, writer, iArgs.Devel)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
@@ -120,8 +121,8 @@ func promptUpgrade(writer io.Writer) bool {
|
||||
}
|
||||
}
|
||||
|
||||
func upgradeManifests(profile *helm.Profile, writer io.Writer) error {
|
||||
installer, err := installer.NewInstaller(profile, writer, false)
|
||||
func upgradeManifests(profile *helm.Profile, writer io.Writer, devel bool) error {
|
||||
installer, err := installer.NewInstaller(profile, writer, false, devel, installer.UpgradeInstallerMode)
|
||||
if err != nil {
|
||||
return err
|
||||
}
|
||||
|
||||
@@ -76,6 +76,7 @@ func getServerCommand() *cobra.Command {
|
||||
Debug: true,
|
||||
NativeIstio: true,
|
||||
HttpAddress: ":8888",
|
||||
CertHttpAddress: ":8889",
|
||||
GrpcAddress: ":15051",
|
||||
GrpcKeepAliveOptions: keepalive.DefaultOption(),
|
||||
XdsOptions: bootstrap.XdsOptions{
|
||||
@@ -112,6 +113,14 @@ func getServerCommand() *cobra.Command {
|
||||
|
||||
serveCmd.PersistentFlags().IntVar(&serverArgs.RegistryOptions.KubeOptions.KubernetesAPIBurst, "kubernetesApiBurst", 160,
|
||||
"Maximum burst for throttle when communicating with the kubernetes API")
|
||||
serveCmd.PersistentFlags().Uint32Var(&serverArgs.GatewayHttpPort, "gatewayHttpPort", 80,
|
||||
"Http listening port of gateway pod")
|
||||
serveCmd.PersistentFlags().Uint32Var(&serverArgs.GatewayHttpsPort, "gatewayHttpsPort", 443,
|
||||
"Https listening port of gateway pod")
|
||||
|
||||
serveCmd.PersistentFlags().BoolVar(&serverArgs.EnableAutomaticHttps, "enableAutomaticHttps", false, "if true, enables automatic https")
|
||||
serveCmd.PersistentFlags().StringVar(&serverArgs.AutomaticHttpsEmail, "automaticHttpsEmail", "", "email for automatic https")
|
||||
serveCmd.PersistentFlags().StringVar(&serverArgs.CertHttpAddress, "certHttpAddress", serverArgs.CertHttpAddress, "the cert http address")
|
||||
|
||||
loggingOptions.AttachCobraFlags(serveCmd)
|
||||
serverArgs.GrpcKeepAliveOptions.AttachCobraFlags(serveCmd)
|
||||
|
||||
@@ -19,6 +19,7 @@ import (
|
||||
"encoding/json"
|
||||
"errors"
|
||||
"fmt"
|
||||
"sort"
|
||||
"strings"
|
||||
"sync"
|
||||
|
||||
@@ -50,6 +51,7 @@ import (
|
||||
higressv1 "github.com/alibaba/higress/api/networking/v1"
|
||||
extlisterv1 "github.com/alibaba/higress/client/pkg/listers/extensions/v1alpha1"
|
||||
netlisterv1 "github.com/alibaba/higress/client/pkg/listers/networking/v1"
|
||||
"github.com/alibaba/higress/pkg/cert"
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/annotations"
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/common"
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/configmap"
|
||||
@@ -143,6 +145,8 @@ type IngressConfig struct {
|
||||
namespace string
|
||||
|
||||
clusterId string
|
||||
|
||||
httpsConfigMgr *cert.ConfigMgr
|
||||
}
|
||||
|
||||
func NewIngressConfig(localKubeClient kube.Client, XDSUpdater model.XDSUpdater, namespace, clusterId string) *IngressConfig {
|
||||
@@ -179,6 +183,9 @@ func NewIngressConfig(localKubeClient kube.Client, XDSUpdater model.XDSUpdater,
|
||||
higressConfigController := configmap.NewController(localKubeClient, clusterId, namespace)
|
||||
config.configmapMgr = configmap.NewConfigmapMgr(XDSUpdater, namespace, higressConfigController, higressConfigController.Lister())
|
||||
|
||||
httpsConfigMgr, _ := cert.NewConfigMgr(namespace, localKubeClient)
|
||||
config.httpsConfigMgr = httpsConfigMgr
|
||||
|
||||
return config
|
||||
}
|
||||
|
||||
@@ -346,6 +353,10 @@ func (m *IngressConfig) convertGateways(configs []common.WrapperConfig) []config
|
||||
Gateways: map[string]*common.WrapperGateway{},
|
||||
}
|
||||
|
||||
httpsCredentialConfig, err := m.httpsConfigMgr.GetConfigFromConfigmap()
|
||||
if err != nil {
|
||||
IngressLog.Errorf("Get higress https configmap err %v", err)
|
||||
}
|
||||
for idx := range configs {
|
||||
cfg := configs[idx]
|
||||
clusterId := common.GetClusterId(cfg.Config.Annotations)
|
||||
@@ -355,7 +366,7 @@ func (m *IngressConfig) convertGateways(configs []common.WrapperConfig) []config
|
||||
if ingressController == nil {
|
||||
continue
|
||||
}
|
||||
if err := ingressController.ConvertGateway(&convertOptions, &cfg); err != nil {
|
||||
if err := ingressController.ConvertGateway(&convertOptions, &cfg, httpsCredentialConfig); err != nil {
|
||||
IngressLog.Errorf("Convert ingress %s/%s to gateway fail in cluster %s, err %v", cfg.Config.Namespace, cfg.Config.Name, clusterId, err)
|
||||
}
|
||||
}
|
||||
@@ -474,9 +485,6 @@ func (m *IngressConfig) convertVirtualService(configs []common.WrapperConfig) []
|
||||
gateways := []string{m.namespace + "/" +
|
||||
common.CreateConvertedName(m.clusterId, cleanHost),
|
||||
common.CreateConvertedName(constants.IstioIngressGatewayName, cleanHost)}
|
||||
if host != "*" {
|
||||
gateways = append(gateways, m.namespace+"/"+common.CreateConvertedName(m.clusterId, common.CleanHost("*")))
|
||||
}
|
||||
|
||||
wrapperVS, exist := convertOptions.VirtualServices[host]
|
||||
if !exist {
|
||||
@@ -515,6 +523,7 @@ func (m *IngressConfig) convertEnvoyFilter(convertOptions *common.ConvertOptions
|
||||
var envoyFilters []config.Config
|
||||
mappings := map[string]*common.Rule{}
|
||||
|
||||
initHttp2RpcGlobalConfig := true
|
||||
for _, routes := range convertOptions.HTTPRoutes {
|
||||
for _, route := range routes {
|
||||
if strings.HasSuffix(route.HTTPRoute.Name, "app-root") {
|
||||
@@ -524,12 +533,13 @@ func (m *IngressConfig) convertEnvoyFilter(convertOptions *common.ConvertOptions
|
||||
http2rpc := route.WrapperConfig.AnnotationsConfig.Http2Rpc
|
||||
if http2rpc != nil {
|
||||
IngressLog.Infof("Found http2rpc for name %s", http2rpc.Name)
|
||||
envoyFilter, err := m.constructHttp2RpcEnvoyFilter(http2rpc, route, m.namespace)
|
||||
envoyFilter, err := m.constructHttp2RpcEnvoyFilter(http2rpc, route, m.namespace, initHttp2RpcGlobalConfig)
|
||||
if err != nil {
|
||||
IngressLog.Infof("Construct http2rpc EnvoyFilter error %v", err)
|
||||
} else {
|
||||
IngressLog.Infof("Append http2rpc EnvoyFilter for name %s", http2rpc.Name)
|
||||
envoyFilters = append(envoyFilters, *envoyFilter)
|
||||
initHttp2RpcGlobalConfig = false
|
||||
}
|
||||
}
|
||||
|
||||
@@ -673,6 +683,18 @@ func (m *IngressConfig) convertDestinationRule(configs []common.WrapperConfig) [
|
||||
|
||||
out := make([]config.Config, 0, len(destinationRules))
|
||||
for _, dr := range destinationRules {
|
||||
sort.SliceStable(dr.DestinationRule.TrafficPolicy.PortLevelSettings, func(i, j int) bool {
|
||||
portI := dr.DestinationRule.TrafficPolicy.PortLevelSettings[i].Port
|
||||
portJ := dr.DestinationRule.TrafficPolicy.PortLevelSettings[j].Port
|
||||
if portI == nil && portJ == nil {
|
||||
return true
|
||||
} else if portI == nil {
|
||||
return true
|
||||
} else if portJ == nil {
|
||||
return false
|
||||
}
|
||||
return portI.Number < portJ.Number
|
||||
})
|
||||
drName := util.CreateDestinationRuleName(m.clusterId, dr.ServiceKey.Namespace, dr.ServiceKey.Name)
|
||||
out = append(out, config.Config{
|
||||
Meta: config.Meta{
|
||||
@@ -788,7 +810,9 @@ func (m *IngressConfig) convertIstioWasmPlugin(obj *higressext.WasmPlugin) (*ext
|
||||
PluginConfig: obj.PluginConfig,
|
||||
PluginName: obj.PluginName,
|
||||
Phase: extensions.PluginPhase(obj.Phase),
|
||||
Priority: obj.Priority,
|
||||
}
|
||||
if obj.GetPriority() != nil {
|
||||
result.Priority = &types.Int64Value{Value: int64(obj.GetPriority().Value)}
|
||||
}
|
||||
if result.PluginConfig != nil {
|
||||
return result, nil
|
||||
@@ -809,7 +833,9 @@ func (m *IngressConfig) convertIstioWasmPlugin(obj *higressext.WasmPlugin) (*ext
|
||||
continue
|
||||
}
|
||||
if rule.Config == nil {
|
||||
return nil, errors.New("invalid rule has no config")
|
||||
rule.Config = &types.Struct{
|
||||
Fields: map[string]*types.Value{},
|
||||
}
|
||||
}
|
||||
v := &types.Value_StructValue{
|
||||
StructValue: rule.Config,
|
||||
@@ -1129,7 +1155,7 @@ func (m *IngressConfig) applyCanaryIngresses(convertOptions *common.ConvertOptio
|
||||
}
|
||||
}
|
||||
|
||||
func (m *IngressConfig) constructHttp2RpcEnvoyFilter(http2rpcConfig *annotations.Http2RpcConfig, route *common.WrapperHTTPRoute, namespace string) (*config.Config, error) {
|
||||
func (m *IngressConfig) constructHttp2RpcEnvoyFilter(http2rpcConfig *annotations.Http2RpcConfig, route *common.WrapperHTTPRoute, namespace string, initHttp2RpcGlobalConfig bool) (*config.Config, error) {
|
||||
mappings := m.http2rpcs
|
||||
IngressLog.Infof("Found http2rpc mappings %v", mappings)
|
||||
if _, exist := mappings[http2rpcConfig.Name]; !exist {
|
||||
@@ -1149,75 +1175,39 @@ func (m *IngressConfig) constructHttp2RpcEnvoyFilter(http2rpcConfig *annotations
|
||||
if err != nil {
|
||||
return nil, errors.New(err.Error())
|
||||
}
|
||||
|
||||
return &config.Config{
|
||||
Meta: config.Meta{
|
||||
GroupVersionKind: gvk.EnvoyFilter,
|
||||
Name: common.CreateConvertedName(constants.IstioIngressGatewayName, http2rpcConfig.Name),
|
||||
Namespace: namespace,
|
||||
configPatches := []*networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
{
|
||||
ApplyTo: networking.EnvoyFilter_HTTP_ROUTE,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_RouteConfiguration{
|
||||
RouteConfiguration: &networking.EnvoyFilter_RouteConfigurationMatch{
|
||||
Vhost: &networking.EnvoyFilter_RouteConfigurationMatch_VirtualHostMatch{
|
||||
Route: &networking.EnvoyFilter_RouteConfigurationMatch_RouteMatch{
|
||||
Name: httpRoute.Name,
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: typeStruct,
|
||||
},
|
||||
},
|
||||
Spec: &networking.EnvoyFilter{
|
||||
ConfigPatches: []*networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
{
|
||||
ApplyTo: networking.EnvoyFilter_HTTP_FILTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_Listener{
|
||||
Listener: &networking.EnvoyFilter_ListenerMatch{
|
||||
FilterChain: &networking.EnvoyFilter_ListenerMatch_FilterChainMatch{
|
||||
Filter: &networking.EnvoyFilter_ListenerMatch_FilterMatch{
|
||||
Name: "envoy.filters.network.http_connection_manager",
|
||||
SubFilter: &networking.EnvoyFilter_ListenerMatch_SubFilterMatch{
|
||||
Name: "envoy.filters.http.router",
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_INSERT_BEFORE,
|
||||
Value: buildPatchStruct(`{
|
||||
"name":"envoy.filters.http.http_dubbo_transcoder",
|
||||
"typed_config":{
|
||||
"@type":"type.googleapis.com/udpa.type.v1.TypedStruct",
|
||||
"type_url":"type.googleapis.com/envoy.extensions.filters.http.http_dubbo_transcoder.v3.HttpDubboTranscoder"
|
||||
}
|
||||
}`),
|
||||
{
|
||||
ApplyTo: networking.EnvoyFilter_CLUSTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_Cluster{
|
||||
Cluster: &networking.EnvoyFilter_ClusterMatch{
|
||||
Service: httpRouteDestination.Destination.Host,
|
||||
},
|
||||
},
|
||||
{
|
||||
ApplyTo: networking.EnvoyFilter_HTTP_ROUTE,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_RouteConfiguration{
|
||||
RouteConfiguration: &networking.EnvoyFilter_RouteConfigurationMatch{
|
||||
Vhost: &networking.EnvoyFilter_RouteConfigurationMatch_VirtualHostMatch{
|
||||
Route: &networking.EnvoyFilter_RouteConfigurationMatch_RouteMatch{
|
||||
Name: httpRoute.Name,
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: typeStruct,
|
||||
},
|
||||
},
|
||||
{
|
||||
ApplyTo: networking.EnvoyFilter_CLUSTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_Cluster{
|
||||
Cluster: &networking.EnvoyFilter_ClusterMatch{
|
||||
Service: httpRouteDestination.Destination.Host,
|
||||
},
|
||||
},
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: buildPatchStruct(`{
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: buildPatchStruct(`{
|
||||
"upstream_config": {
|
||||
"name":"envoy.upstreams.http.dubbo_tcp",
|
||||
"typed_config":{
|
||||
@@ -1226,9 +1216,47 @@ func (m *IngressConfig) constructHttp2RpcEnvoyFilter(http2rpcConfig *annotations
|
||||
}
|
||||
}
|
||||
}`),
|
||||
},
|
||||
},
|
||||
}
|
||||
if initHttp2RpcGlobalConfig {
|
||||
configPatches = append(configPatches, &networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
ApplyTo: networking.EnvoyFilter_HTTP_FILTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_Listener{
|
||||
Listener: &networking.EnvoyFilter_ListenerMatch{
|
||||
FilterChain: &networking.EnvoyFilter_ListenerMatch_FilterChainMatch{
|
||||
Filter: &networking.EnvoyFilter_ListenerMatch_FilterMatch{
|
||||
Name: "envoy.filters.network.http_connection_manager",
|
||||
SubFilter: &networking.EnvoyFilter_ListenerMatch_SubFilterMatch{
|
||||
Name: "envoy.filters.http.router",
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_INSERT_BEFORE,
|
||||
Value: buildPatchStruct(`{
|
||||
"name":"envoy.filters.http.http_dubbo_transcoder",
|
||||
"typed_config":{
|
||||
"@type":"type.googleapis.com/udpa.type.v1.TypedStruct",
|
||||
"type_url":"type.googleapis.com/envoy.extensions.filters.http.http_dubbo_transcoder.v3.HttpDubboTranscoder"
|
||||
}
|
||||
}`),
|
||||
},
|
||||
})
|
||||
}
|
||||
return &config.Config{
|
||||
Meta: config.Meta{
|
||||
GroupVersionKind: gvk.EnvoyFilter,
|
||||
Name: common.CreateConvertedName(constants.IstioIngressGatewayName, http2rpcConfig.Name),
|
||||
Namespace: namespace,
|
||||
},
|
||||
Spec: &networking.EnvoyFilter{
|
||||
ConfigPatches: configPatches,
|
||||
},
|
||||
}, nil
|
||||
}
|
||||
|
||||
@@ -111,14 +111,18 @@ func TestNormalizeWeightedCluster(t *testing.T) {
|
||||
func TestConvertGatewaysForIngress(t *testing.T) {
|
||||
fake := kube.NewFakeClient()
|
||||
v1Beta1Options := common.Options{
|
||||
Enable: true,
|
||||
ClusterId: "ingress-v1beta1",
|
||||
RawClusterId: "ingress-v1beta1__",
|
||||
Enable: true,
|
||||
ClusterId: "ingress-v1beta1",
|
||||
RawClusterId: "ingress-v1beta1__",
|
||||
GatewayHttpPort: 80,
|
||||
GatewayHttpsPort: 443,
|
||||
}
|
||||
v1Options := common.Options{
|
||||
Enable: true,
|
||||
ClusterId: "ingress-v1",
|
||||
RawClusterId: "ingress-v1__",
|
||||
Enable: true,
|
||||
ClusterId: "ingress-v1",
|
||||
RawClusterId: "ingress-v1__",
|
||||
GatewayHttpPort: 80,
|
||||
GatewayHttpsPort: 443,
|
||||
}
|
||||
ingressV1Beta1Controller := controllerv1beta1.NewController(fake, fake, v1Beta1Options, nil)
|
||||
ingressV1Controller := controllerv1.NewController(fake, fake, v1Options, nil)
|
||||
|
||||
@@ -314,9 +314,6 @@ func (m *KIngressConfig) convertVirtualService(configs []common.WrapperConfig) [
|
||||
gateways := []string{m.namespace + "/" +
|
||||
common.CreateConvertedName(m.clusterId, cleanHost),
|
||||
common.CreateConvertedName(constants.IstioIngressGatewayName, cleanHost)}
|
||||
if host != "*" {
|
||||
gateways = append(gateways, m.namespace+"/"+common.CreateConvertedName(m.clusterId, common.CleanHost("*")))
|
||||
}
|
||||
|
||||
wrapperVS, exist := convertOptions.VirtualServices[host]
|
||||
if !exist {
|
||||
|
||||
@@ -83,7 +83,7 @@ func (i *Ingress) NeedRegexMatch(path string) bool {
|
||||
if i.Rewrite == nil {
|
||||
return false
|
||||
}
|
||||
if strings.ContainsAny(path, `\.+*?()|[]{}^$`) {
|
||||
if i.Rewrite.RewriteTarget != "" && strings.ContainsAny(path, `\.+*?()|[]{}^$`) {
|
||||
return true
|
||||
}
|
||||
if strings.ContainsAny(i.Rewrite.RewriteTarget, `$\`) {
|
||||
|
||||
@@ -67,6 +67,15 @@ func TestNeedRegexMatch(t *testing.T) {
|
||||
inputPath: "/.*",
|
||||
expect: true,
|
||||
},
|
||||
{
|
||||
input: &Ingress{
|
||||
Rewrite: &RewriteConfig{
|
||||
UseRegex: false,
|
||||
},
|
||||
},
|
||||
inputPath: "/.",
|
||||
expect: false,
|
||||
},
|
||||
{
|
||||
input: &Ingress{
|
||||
Rewrite: &RewriteConfig{
|
||||
|
||||
@@ -23,13 +23,14 @@ import (
|
||||
)
|
||||
|
||||
const (
|
||||
exact = "exact"
|
||||
regex = "regex"
|
||||
prefix = "prefix"
|
||||
MatchMethod = "match-method"
|
||||
MatchQuery = "match-query"
|
||||
MatchHeader = "match-header"
|
||||
sep = " "
|
||||
exact = "exact"
|
||||
regex = "regex"
|
||||
prefix = "prefix"
|
||||
MatchMethod = "match-method"
|
||||
MatchQuery = "match-query"
|
||||
MatchHeader = "match-header"
|
||||
MatchPseudoHeader = "match-pseudo-header"
|
||||
sep = " "
|
||||
)
|
||||
|
||||
var (
|
||||
@@ -56,6 +57,24 @@ func (m match) Parse(annotations Annotations, config *Ingress, _ *GlobalContext)
|
||||
IngressLog.Errorf("parse headers error %v within ingress %s/%s", err, config.Namespace, config.Name)
|
||||
}
|
||||
|
||||
var pseudoHeaderMatches map[string]map[string]string
|
||||
if pseudoHeaderMatches, err = m.matchByHeaderOrQueryParma(annotations, MatchPseudoHeader, pseudoHeaderMatches); err != nil {
|
||||
IngressLog.Errorf("parse headers error %v within ingress %s/%s", err, config.Namespace, config.Name)
|
||||
}
|
||||
if pseudoHeaderMatches != nil && len(pseudoHeaderMatches) > 0 {
|
||||
if config.Match.Headers == nil {
|
||||
config.Match.Headers = make(map[string]map[string]string)
|
||||
}
|
||||
for typ, mmap := range pseudoHeaderMatches {
|
||||
if config.Match.Headers[typ] == nil {
|
||||
config.Match.Headers[typ] = make(map[string]string)
|
||||
}
|
||||
for k, v := range mmap {
|
||||
config.Match.Headers[typ][":"+k] = v
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
if config.Match.QueryParams, err = m.matchByHeaderOrQueryParma(annotations, MatchQuery, config.Match.QueryParams); err != nil {
|
||||
IngressLog.Errorf("parse query params error %v within ingress %s/%s", err, config.Namespace, config.Name)
|
||||
}
|
||||
|
||||
@@ -15,6 +15,7 @@
|
||||
package annotations
|
||||
|
||||
import (
|
||||
"strings"
|
||||
"testing"
|
||||
|
||||
"github.com/google/go-cmp/cmp"
|
||||
@@ -112,11 +113,47 @@ func TestMatch_ParseHeaders(t *testing.T) {
|
||||
},
|
||||
},
|
||||
},
|
||||
{
|
||||
typ: "exact",
|
||||
key: ":method",
|
||||
value: "GET",
|
||||
expect: map[string]map[string]string{
|
||||
exact: {
|
||||
":method": "GET",
|
||||
},
|
||||
},
|
||||
},
|
||||
{
|
||||
typ: "prefix",
|
||||
key: ":path",
|
||||
value: "/foo",
|
||||
expect: map[string]map[string]string{
|
||||
prefix: {
|
||||
":path": "/foo",
|
||||
},
|
||||
},
|
||||
},
|
||||
{
|
||||
typ: "regex",
|
||||
key: ":authority",
|
||||
value: "test\\d+\\.com",
|
||||
expect: map[string]map[string]string{
|
||||
regex: {
|
||||
":authority": "test\\d+\\.com",
|
||||
},
|
||||
},
|
||||
},
|
||||
}
|
||||
|
||||
for _, tt := range testCases {
|
||||
t.Run("", func(t *testing.T) {
|
||||
key := buildHigressAnnotationKey(tt.typ + "-" + MatchHeader + "-" + tt.key)
|
||||
matchKeyword := MatchHeader
|
||||
headerKey := tt.key
|
||||
if strings.HasPrefix(headerKey, ":") {
|
||||
headerKey = strings.TrimPrefix(headerKey, ":")
|
||||
matchKeyword = MatchPseudoHeader
|
||||
}
|
||||
key := buildHigressAnnotationKey(tt.typ + "-" + matchKeyword + "-" + headerKey)
|
||||
input := Annotations{key: tt.value}
|
||||
config := &Ingress{}
|
||||
_ = parser.Parse(input, config, nil)
|
||||
|
||||
@@ -65,7 +65,12 @@ func (u upstreamTLS) Parse(annotations Annotations, config *Ingress, _ *GlobalCo
|
||||
}
|
||||
|
||||
defer func() {
|
||||
config.UpstreamTLS = upstreamTLSConfig
|
||||
if upstreamTLSConfig.BackendProtocol == defaultBackendProtocol {
|
||||
// no need destination rule when use HTTP protocol
|
||||
config.UpstreamTLS = nil
|
||||
} else {
|
||||
config.UpstreamTLS = upstreamTLSConfig
|
||||
}
|
||||
}()
|
||||
|
||||
if proto, err := annotations.ParseStringASAP(backendProtocol); err == nil {
|
||||
|
||||
@@ -33,6 +33,12 @@ func TestUpstreamTLSParse(t *testing.T) {
|
||||
input: Annotations{},
|
||||
expect: nil,
|
||||
},
|
||||
{
|
||||
input: Annotations{
|
||||
buildNginxAnnotationKey(backendProtocol): "HTTP",
|
||||
},
|
||||
expect: nil,
|
||||
},
|
||||
{
|
||||
input: Annotations{
|
||||
buildNginxAnnotationKey(proxySSLSecret): "",
|
||||
|
||||
@@ -17,14 +17,14 @@ package common
|
||||
import (
|
||||
"strings"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cert"
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/annotations"
|
||||
networking "istio.io/api/networking/v1alpha3"
|
||||
"istio.io/istio/pilot/pkg/model"
|
||||
"istio.io/istio/pkg/config"
|
||||
gatewaytool "istio.io/istio/pkg/config/gateway"
|
||||
listerv1 "k8s.io/client-go/listers/core/v1"
|
||||
"k8s.io/client-go/tools/cache"
|
||||
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/annotations"
|
||||
)
|
||||
|
||||
type ServiceKey struct {
|
||||
@@ -121,7 +121,7 @@ type IngressController interface {
|
||||
|
||||
SecretLister() listerv1.SecretLister
|
||||
|
||||
ConvertGateway(convertOptions *ConvertOptions, wrapper *WrapperConfig) error
|
||||
ConvertGateway(convertOptions *ConvertOptions, wrapper *WrapperConfig, httpsCredentialConfig *cert.Config) error
|
||||
|
||||
ConvertHTTPRoute(convertOptions *ConvertOptions, wrapper *WrapperConfig) error
|
||||
|
||||
|
||||
@@ -105,6 +105,8 @@ type Options struct {
|
||||
SystemNamespace string
|
||||
GatewaySelectorKey string
|
||||
GatewaySelectorValue string
|
||||
GatewayHttpPort uint32
|
||||
GatewayHttpsPort uint32
|
||||
}
|
||||
|
||||
type BasicAuthRules struct {
|
||||
|
||||
@@ -36,7 +36,6 @@ func ValidateBackendResource(resource *v1.TypedLocalObjectReference) bool {
|
||||
if resource == nil || resource.APIGroup == nil ||
|
||||
*resource.APIGroup != netv1.SchemeGroupVersion.Group ||
|
||||
resource.Kind != "McpBridge" || resource.Name != "default" {
|
||||
IngressLog.Warnf("invalid mcpbridge resource: %v", resource)
|
||||
return false
|
||||
}
|
||||
return true
|
||||
@@ -49,13 +48,15 @@ func V1Available(client kube.Client) bool {
|
||||
|
||||
serverVersion, err := client.GetKubernetesVersion()
|
||||
if err != nil {
|
||||
return false
|
||||
// Consider the new ingress package is available as default
|
||||
return true
|
||||
}
|
||||
|
||||
runningVersion, err := version.ParseGeneric(serverVersion.String())
|
||||
if err != nil {
|
||||
// Consider the new ingress package is available as default
|
||||
IngressLog.Errorf("unexpected error parsing running Kubernetes version: %v", err)
|
||||
return false
|
||||
return true
|
||||
}
|
||||
|
||||
return runningVersion.AtLeast(version119)
|
||||
|
||||
@@ -37,6 +37,7 @@ type HigressConfig struct {
|
||||
Tracing *Tracing `json:"tracing,omitempty"`
|
||||
Gzip *Gzip `json:"gzip,omitempty"`
|
||||
Downstream *Downstream `json:"downstream,omitempty"`
|
||||
Upstream *Upstream `json:"upstream,omitempty"`
|
||||
DisableXEnvoyHeaders bool `json:"disableXEnvoyHeaders,omitempty"`
|
||||
AddXRealIpHeader bool `json:"addXRealIpHeader,omitempty"`
|
||||
}
|
||||
@@ -47,6 +48,7 @@ func NewDefaultHigressConfig() *HigressConfig {
|
||||
Tracing: NewDefaultTracing(),
|
||||
Gzip: NewDefaultGzip(),
|
||||
Downstream: globalOption.Downstream,
|
||||
Upstream: globalOption.Upstream,
|
||||
DisableXEnvoyHeaders: globalOption.DisableXEnvoyHeaders,
|
||||
AddXRealIpHeader: globalOption.AddXRealIpHeader,
|
||||
}
|
||||
|
||||
@@ -15,7 +15,6 @@
|
||||
package configmap
|
||||
|
||||
import (
|
||||
"encoding/json"
|
||||
"fmt"
|
||||
"reflect"
|
||||
"sync/atomic"
|
||||
@@ -38,19 +37,23 @@ const (
|
||||
minInitialConnectionWindowSize = 65535
|
||||
maxInitialConnectionWindowSize = 2147483647
|
||||
|
||||
defaultIdleTimeout = 180
|
||||
defaultMaxRequestHeadersKb = 60
|
||||
defaultConnectionBufferLimits = 32768
|
||||
defaultMaxConcurrentStreams = 100
|
||||
defaultInitialStreamWindowSize = 65535
|
||||
defaultInitialConnectionWindowSize = 1048576
|
||||
defaultAddXRealIpHeader = false
|
||||
defaultDisableXEnvoyHeaders = false
|
||||
defaultIdleTimeout = 180
|
||||
defaultRouteTimeout = 0
|
||||
defaultUpStreamIdleTimeout = 10
|
||||
defaultUpStreamConnectionBufferLimits = 10485760
|
||||
defaultMaxRequestHeadersKb = 60
|
||||
defaultConnectionBufferLimits = 32768
|
||||
defaultMaxConcurrentStreams = 100
|
||||
defaultInitialStreamWindowSize = 65535
|
||||
defaultInitialConnectionWindowSize = 1048576
|
||||
defaultAddXRealIpHeader = false
|
||||
defaultDisableXEnvoyHeaders = false
|
||||
)
|
||||
|
||||
// Global configures the behavior of the downstream connection, x-real-ip header and x-envoy headers.
|
||||
type Global struct {
|
||||
Downstream *Downstream `json:"downstream,omitempty"`
|
||||
Upstream *Upstream `json:"upstream,omitempty"`
|
||||
AddXRealIpHeader bool `json:"addXRealIpHeader,omitempty"`
|
||||
DisableXEnvoyHeaders bool `json:"disableXEnvoyHeaders,omitempty"`
|
||||
}
|
||||
@@ -58,13 +61,23 @@ type Global struct {
|
||||
// Downstream configures the behavior of the downstream connection.
|
||||
type Downstream struct {
|
||||
// IdleTimeout limits the time that a connection may be idle and stream idle.
|
||||
IdleTimeout uint32 `json:"idleTimeout,omitempty"`
|
||||
IdleTimeout uint32 `json:"idleTimeout"`
|
||||
// MaxRequestHeadersKb limits the size of request headers allowed.
|
||||
MaxRequestHeadersKb uint32 `json:"maxRequestHeadersKb,omitempty"`
|
||||
// ConnectionBufferLimits configures the buffer size limits for connections.
|
||||
ConnectionBufferLimits uint32 `json:"connectionBufferLimits,omitempty"`
|
||||
// Http2 configures HTTP/2 specific options.
|
||||
Http2 *Http2 `json:"http2,omitempty"`
|
||||
//RouteTimeout limits the time that timeout for the route.
|
||||
RouteTimeout uint32 `json:"routeTimeout"`
|
||||
}
|
||||
|
||||
// Upstream configures the behavior of the upstream connection.
|
||||
type Upstream struct {
|
||||
// IdleTimeout limits the time that a connection may be idle on the upstream.
|
||||
IdleTimeout uint32 `json:"idleTimeout"`
|
||||
// ConnectionBufferLimits configures the buffer size limits for connections.
|
||||
ConnectionBufferLimits uint32 `json:"connectionBufferLimits,omitempty"`
|
||||
}
|
||||
|
||||
// Http2 configures HTTP/2 specific options.
|
||||
@@ -125,7 +138,7 @@ func compareGlobal(old *Global, new *Global) (Result, error) {
|
||||
return ResultDelete, nil
|
||||
}
|
||||
|
||||
if new.Downstream == nil && !new.AddXRealIpHeader && !new.DisableXEnvoyHeaders {
|
||||
if new.Downstream == nil && new.Upstream == nil && !new.AddXRealIpHeader && !new.DisableXEnvoyHeaders {
|
||||
return ResultDelete, nil
|
||||
}
|
||||
|
||||
@@ -139,18 +152,31 @@ func compareGlobal(old *Global, new *Global) (Result, error) {
|
||||
// deepCopyGlobal deep copies the global option.
|
||||
func deepCopyGlobal(global *Global) (*Global, error) {
|
||||
newGlobal := NewDefaultGlobalOption()
|
||||
bytes, err := json.Marshal(global)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
if global.Downstream != nil {
|
||||
newGlobal.Downstream.IdleTimeout = global.Downstream.IdleTimeout
|
||||
newGlobal.Downstream.MaxRequestHeadersKb = global.Downstream.MaxRequestHeadersKb
|
||||
newGlobal.Downstream.ConnectionBufferLimits = global.Downstream.ConnectionBufferLimits
|
||||
if global.Downstream.Http2 != nil {
|
||||
newGlobal.Downstream.Http2.MaxConcurrentStreams = global.Downstream.Http2.MaxConcurrentStreams
|
||||
newGlobal.Downstream.Http2.InitialStreamWindowSize = global.Downstream.Http2.InitialStreamWindowSize
|
||||
newGlobal.Downstream.Http2.InitialConnectionWindowSize = global.Downstream.Http2.InitialConnectionWindowSize
|
||||
}
|
||||
newGlobal.Downstream.RouteTimeout = global.Downstream.RouteTimeout
|
||||
}
|
||||
err = json.Unmarshal(bytes, newGlobal)
|
||||
return newGlobal, err
|
||||
if global.Upstream != nil {
|
||||
newGlobal.Upstream.IdleTimeout = global.Upstream.IdleTimeout
|
||||
newGlobal.Upstream.ConnectionBufferLimits = global.Upstream.ConnectionBufferLimits
|
||||
}
|
||||
newGlobal.AddXRealIpHeader = global.AddXRealIpHeader
|
||||
newGlobal.DisableXEnvoyHeaders = global.DisableXEnvoyHeaders
|
||||
return newGlobal, nil
|
||||
}
|
||||
|
||||
// NewDefaultGlobalOption returns a default global config.
|
||||
func NewDefaultGlobalOption() *Global {
|
||||
return &Global{
|
||||
Downstream: NewDefaultDownstream(),
|
||||
Upstream: NewDefaultUpStream(),
|
||||
AddXRealIpHeader: defaultAddXRealIpHeader,
|
||||
DisableXEnvoyHeaders: defaultDisableXEnvoyHeaders,
|
||||
}
|
||||
@@ -163,6 +189,15 @@ func NewDefaultDownstream() *Downstream {
|
||||
MaxRequestHeadersKb: defaultMaxRequestHeadersKb,
|
||||
ConnectionBufferLimits: defaultConnectionBufferLimits,
|
||||
Http2: NewDefaultHttp2(),
|
||||
RouteTimeout: defaultRouteTimeout,
|
||||
}
|
||||
}
|
||||
|
||||
// NewDefaultUpStream returns a default upstream config.
|
||||
func NewDefaultUpStream() *Upstream {
|
||||
return &Upstream{
|
||||
IdleTimeout: defaultUpStreamIdleTimeout,
|
||||
ConnectionBufferLimits: defaultUpStreamConnectionBufferLimits,
|
||||
}
|
||||
}
|
||||
|
||||
@@ -215,12 +250,14 @@ func (g *GlobalOptionController) GetName() string {
|
||||
func (g *GlobalOptionController) AddOrUpdateHigressConfig(name util.ClusterNamespacedName, old *HigressConfig, new *HigressConfig) error {
|
||||
newGlobal := &Global{
|
||||
Downstream: new.Downstream,
|
||||
Upstream: new.Upstream,
|
||||
AddXRealIpHeader: new.AddXRealIpHeader,
|
||||
DisableXEnvoyHeaders: new.DisableXEnvoyHeaders,
|
||||
}
|
||||
|
||||
oldGlobal := &Global{
|
||||
Downstream: old.Downstream,
|
||||
Upstream: old.Upstream,
|
||||
AddXRealIpHeader: old.AddXRealIpHeader,
|
||||
DisableXEnvoyHeaders: old.DisableXEnvoyHeaders,
|
||||
}
|
||||
@@ -264,6 +301,7 @@ func (g *GlobalOptionController) ValidHigressConfig(higressConfig *HigressConfig
|
||||
|
||||
global := &Global{
|
||||
Downstream: higressConfig.Downstream,
|
||||
Upstream: higressConfig.Upstream,
|
||||
AddXRealIpHeader: higressConfig.AddXRealIpHeader,
|
||||
DisableXEnvoyHeaders: higressConfig.DisableXEnvoyHeaders,
|
||||
}
|
||||
@@ -275,8 +313,7 @@ func (g *GlobalOptionController) ConstructEnvoyFilters() ([]*config.Config, erro
|
||||
configPatch := make([]*networking.EnvoyFilter_EnvoyConfigObjectPatch, 0)
|
||||
global := g.GetGlobal()
|
||||
if global == nil {
|
||||
configs := make([]*config.Config, 0)
|
||||
return configs, nil
|
||||
return []*config.Config{}, nil
|
||||
}
|
||||
|
||||
namespace := g.Namespace
|
||||
@@ -293,18 +330,28 @@ func (g *GlobalOptionController) ConstructEnvoyFilters() ([]*config.Config, erro
|
||||
configPatch = append(configPatch, disableXEnvoyHeadersConfig...)
|
||||
}
|
||||
|
||||
if global.Downstream == nil {
|
||||
return generateEnvoyFilter(namespace, configPatch), nil
|
||||
if global.Downstream != nil {
|
||||
downstreamStruct := g.constructDownstream(global.Downstream)
|
||||
bufferLimitStruct := g.constructBufferLimit(global.Downstream)
|
||||
routeTimeoutStruct := g.constructRouteTimeout(global.Downstream)
|
||||
downstreamConfig := g.generateDownstreamEnvoyFilter(downstreamStruct, bufferLimitStruct, routeTimeoutStruct, namespace)
|
||||
if downstreamConfig != nil {
|
||||
configPatch = append(configPatch, downstreamConfig...)
|
||||
}
|
||||
}
|
||||
|
||||
downstreamStruct := g.constructDownstream(global.Downstream)
|
||||
bufferLimitStruct := g.constructBufferLimit(global.Downstream)
|
||||
if len(downstreamStruct) == 0 && len(bufferLimitStruct) == 0 {
|
||||
return generateEnvoyFilter(namespace, configPatch), nil
|
||||
if global.Upstream != nil {
|
||||
upstreamStruct := g.constructUpstream(global.Upstream)
|
||||
bufferLimitStruct := g.constructUpstreamBufferLimit(global.Upstream)
|
||||
upstreamConfig := g.generateUpstreamEnvoyFilter(upstreamStruct, bufferLimitStruct, namespace)
|
||||
if upstreamConfig != nil {
|
||||
configPatch = append(configPatch, upstreamConfig...)
|
||||
}
|
||||
}
|
||||
|
||||
downstreamConfig := g.generateDownstreamEnvoyFilter(downstreamStruct, bufferLimitStruct, namespace)
|
||||
configPatch = append(configPatch, downstreamConfig...)
|
||||
if len(configPatch) == 0 {
|
||||
return []*config.Config{}, nil
|
||||
}
|
||||
|
||||
return generateEnvoyFilter(namespace, configPatch), nil
|
||||
}
|
||||
@@ -330,9 +377,11 @@ func (g *GlobalOptionController) RegisterItemEventHandler(eventHandler ItemEvent
|
||||
}
|
||||
|
||||
// generateDownstreamEnvoyFilter generates the downstream envoy filter.
|
||||
func (g *GlobalOptionController) generateDownstreamEnvoyFilter(downstreamValueStruct string, bufferLimitStruct string, namespace string) []*networking.EnvoyFilter_EnvoyConfigObjectPatch {
|
||||
downstreamConfig := []*networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
{
|
||||
func (g *GlobalOptionController) generateDownstreamEnvoyFilter(downstreamValueStruct string, bufferLimitStruct string, routeTimeoutStruct string, namespace string) []*networking.EnvoyFilter_EnvoyConfigObjectPatch {
|
||||
var downstreamConfig []*networking.EnvoyFilter_EnvoyConfigObjectPatch
|
||||
|
||||
if len(downstreamValueStruct) != 0 {
|
||||
downstreamConfig = append(downstreamConfig, &networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
ApplyTo: networking.EnvoyFilter_NETWORK_FILTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
@@ -350,8 +399,11 @@ func (g *GlobalOptionController) generateDownstreamEnvoyFilter(downstreamValueSt
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: util.BuildPatchStruct(downstreamValueStruct),
|
||||
},
|
||||
},
|
||||
{
|
||||
})
|
||||
}
|
||||
|
||||
if len(bufferLimitStruct) != 0 {
|
||||
downstreamConfig = append(downstreamConfig, &networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
ApplyTo: networking.EnvoyFilter_LISTENER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
@@ -360,11 +412,66 @@ func (g *GlobalOptionController) generateDownstreamEnvoyFilter(downstreamValueSt
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: util.BuildPatchStruct(bufferLimitStruct),
|
||||
},
|
||||
},
|
||||
})
|
||||
}
|
||||
|
||||
if len(routeTimeoutStruct) != 0 {
|
||||
downstreamConfig = append(downstreamConfig, &networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
ApplyTo: networking.EnvoyFilter_HTTP_ROUTE,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
ObjectTypes: &networking.EnvoyFilter_EnvoyConfigObjectMatch_RouteConfiguration{
|
||||
RouteConfiguration: &networking.EnvoyFilter_RouteConfigurationMatch{
|
||||
Vhost: &networking.EnvoyFilter_RouteConfigurationMatch_VirtualHostMatch{
|
||||
Route: &networking.EnvoyFilter_RouteConfigurationMatch_RouteMatch{
|
||||
Action: networking.EnvoyFilter_RouteConfigurationMatch_RouteMatch_ROUTE,
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: util.BuildPatchStruct(routeTimeoutStruct),
|
||||
},
|
||||
})
|
||||
}
|
||||
|
||||
return downstreamConfig
|
||||
}
|
||||
|
||||
func (g *GlobalOptionController) generateUpstreamEnvoyFilter(upstreamValueStruct string, bufferLimit string, namespace string) []*networking.EnvoyFilter_EnvoyConfigObjectPatch {
|
||||
var upstreamConfig []*networking.EnvoyFilter_EnvoyConfigObjectPatch
|
||||
|
||||
if len(upstreamValueStruct) != 0 {
|
||||
upstreamConfig = append(upstreamConfig, &networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
ApplyTo: networking.EnvoyFilter_CLUSTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: util.BuildPatchStruct(upstreamValueStruct),
|
||||
},
|
||||
})
|
||||
}
|
||||
|
||||
if len(bufferLimit) != 0 {
|
||||
upstreamConfig = append(upstreamConfig, &networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
ApplyTo: networking.EnvoyFilter_CLUSTER,
|
||||
Match: &networking.EnvoyFilter_EnvoyConfigObjectMatch{
|
||||
Context: networking.EnvoyFilter_GATEWAY,
|
||||
},
|
||||
Patch: &networking.EnvoyFilter_Patch{
|
||||
Operation: networking.EnvoyFilter_Patch_MERGE,
|
||||
Value: util.BuildPatchStruct(bufferLimit),
|
||||
},
|
||||
})
|
||||
}
|
||||
|
||||
return upstreamConfig
|
||||
}
|
||||
|
||||
// generateAddXRealIpHeaderEnvoyFilter generates the add x-real-ip header envoy filter.
|
||||
func (g *GlobalOptionController) generateAddXRealIpHeaderEnvoyFilter(addXRealIpHeaderStruct string, namespace string) []*networking.EnvoyFilter_EnvoyConfigObjectPatch {
|
||||
addXRealIpHeaderConfig := []*networking.EnvoyFilter_EnvoyConfigObjectPatch{
|
||||
@@ -460,6 +567,32 @@ func (g *GlobalOptionController) constructDownstream(downstream *Downstream) str
|
||||
return downstreamConfig
|
||||
}
|
||||
|
||||
// constructUpstream constructs the upstream config.
|
||||
func (g *GlobalOptionController) constructUpstream(upstream *Upstream) string {
|
||||
upstreamConfig := ""
|
||||
idleTimeout := upstream.IdleTimeout
|
||||
|
||||
upstreamConfig = fmt.Sprintf(`
|
||||
{
|
||||
"common_http_protocol_options": {
|
||||
"idleTimeout": "%ds"
|
||||
}
|
||||
}
|
||||
`, idleTimeout)
|
||||
|
||||
return upstreamConfig
|
||||
}
|
||||
|
||||
// constructUpstreamBufferLimit constructs the upstream buffer limit config.
|
||||
func (g *GlobalOptionController) constructUpstreamBufferLimit(upstream *Upstream) string {
|
||||
upstreamBufferLimitStruct := fmt.Sprintf(`
|
||||
{
|
||||
"per_connection_buffer_limit_bytes": %d
|
||||
}
|
||||
`, upstream.ConnectionBufferLimits)
|
||||
return upstreamBufferLimitStruct
|
||||
}
|
||||
|
||||
// constructAddXRealIpHeader constructs the add x-real-ip header config.
|
||||
func (g *GlobalOptionController) constructAddXRealIpHeader() string {
|
||||
addXRealIpHeaderStruct := fmt.Sprintf(`
|
||||
@@ -500,3 +633,17 @@ func (g *GlobalOptionController) constructBufferLimit(downstream *Downstream) st
|
||||
}
|
||||
`, downstream.ConnectionBufferLimits)
|
||||
}
|
||||
|
||||
// constructRouteTimeout constructs the route timeout config.
|
||||
func (g *GlobalOptionController) constructRouteTimeout(downstream *Downstream) string {
|
||||
if downstream.RouteTimeout == 0 {
|
||||
return ""
|
||||
}
|
||||
return fmt.Sprintf(`
|
||||
{
|
||||
"route": {
|
||||
"timeout": "%ds"
|
||||
}
|
||||
}
|
||||
`, downstream.RouteTimeout)
|
||||
}
|
||||
|
||||
@@ -41,6 +41,7 @@ func Test_validGlobal(t *testing.T) {
|
||||
name: "downstream nil",
|
||||
global: &Global{
|
||||
Downstream: nil,
|
||||
Upstream: NewDefaultUpStream(),
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
},
|
||||
@@ -131,35 +132,27 @@ func Test_deepCopyGlobal(t *testing.T) {
|
||||
name: "deep copy 2",
|
||||
global: &Global{
|
||||
Downstream: &Downstream{
|
||||
IdleTimeout: 1,
|
||||
IdleTimeout: 0,
|
||||
MaxRequestHeadersKb: 9600,
|
||||
ConnectionBufferLimits: 4096,
|
||||
Http2: NewDefaultHttp2(),
|
||||
},
|
||||
Upstream: &Upstream{
|
||||
IdleTimeout: 10,
|
||||
},
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
},
|
||||
want: &Global{
|
||||
Downstream: &Downstream{
|
||||
IdleTimeout: 1,
|
||||
IdleTimeout: 0,
|
||||
MaxRequestHeadersKb: 9600,
|
||||
ConnectionBufferLimits: 4096,
|
||||
Http2: NewDefaultHttp2(),
|
||||
},
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
},
|
||||
wantErr: nil,
|
||||
},
|
||||
{
|
||||
name: "deep copy 3",
|
||||
global: &Global{
|
||||
Downstream: &Downstream{},
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
},
|
||||
want: &Global{
|
||||
Downstream: NewDefaultDownstream(),
|
||||
Upstream: &Upstream{
|
||||
IdleTimeout: 10,
|
||||
},
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
},
|
||||
@@ -203,7 +196,13 @@ func Test_AddOrUpdateHigressConfig(t *testing.T) {
|
||||
old: NewDefaultHigressConfig(),
|
||||
new: &HigressConfig{
|
||||
Downstream: &Downstream{
|
||||
IdleTimeout: 1,
|
||||
IdleTimeout: 1,
|
||||
MaxRequestHeadersKb: defaultMaxRequestHeadersKb,
|
||||
ConnectionBufferLimits: defaultConnectionBufferLimits,
|
||||
Http2: NewDefaultHttp2(),
|
||||
},
|
||||
Upstream: &Upstream{
|
||||
IdleTimeout: 10,
|
||||
},
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
@@ -217,6 +216,9 @@ func Test_AddOrUpdateHigressConfig(t *testing.T) {
|
||||
ConnectionBufferLimits: defaultConnectionBufferLimits,
|
||||
Http2: NewDefaultHttp2(),
|
||||
},
|
||||
Upstream: &Upstream{
|
||||
IdleTimeout: 10,
|
||||
},
|
||||
AddXRealIpHeader: true,
|
||||
DisableXEnvoyHeaders: true,
|
||||
},
|
||||
@@ -225,6 +227,7 @@ func Test_AddOrUpdateHigressConfig(t *testing.T) {
|
||||
name: "delete and push",
|
||||
old: &HigressConfig{
|
||||
Downstream: NewDefaultDownstream(),
|
||||
Upstream: NewDefaultUpStream(),
|
||||
AddXRealIpHeader: defaultAddXRealIpHeader,
|
||||
DisableXEnvoyHeaders: defaultDisableXEnvoyHeaders,
|
||||
},
|
||||
@@ -233,6 +236,7 @@ func Test_AddOrUpdateHigressConfig(t *testing.T) {
|
||||
wantEventPush: "push",
|
||||
wantGlobal: &Global{
|
||||
Downstream: NewDefaultDownstream(),
|
||||
Upstream: NewDefaultUpStream(),
|
||||
AddXRealIpHeader: defaultAddXRealIpHeader,
|
||||
DisableXEnvoyHeaders: defaultDisableXEnvoyHeaders,
|
||||
},
|
||||
|
||||
@@ -24,6 +24,8 @@ import (
|
||||
"sync"
|
||||
"time"
|
||||
|
||||
"github.com/alibaba/higress/pkg/cert"
|
||||
|
||||
"github.com/hashicorp/go-multierror"
|
||||
networking "istio.io/api/networking/v1alpha3"
|
||||
"istio.io/istio/pilot/pkg/model"
|
||||
@@ -53,6 +55,7 @@ import (
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/secret"
|
||||
"github.com/alibaba/higress/pkg/ingress/kube/util"
|
||||
. "github.com/alibaba/higress/pkg/ingress/log"
|
||||
k8serrors "k8s.io/apimachinery/pkg/api/errors"
|
||||
)
|
||||
|
||||
var (
|
||||
@@ -348,7 +351,7 @@ func extractTLSSecretName(host string, tls []ingress.IngressTLS) string {
|
||||
return ""
|
||||
}
|
||||
|
||||
func (c *controller) ConvertGateway(convertOptions *common.ConvertOptions, wrapper *common.WrapperConfig) error {
|
||||
func (c *controller) ConvertGateway(convertOptions *common.ConvertOptions, wrapper *common.WrapperConfig, httpsCredentialConfig *cert.Config) error {
|
||||
if convertOptions == nil {
|
||||
return fmt.Errorf("convertOptions is nil")
|
||||
}
|
||||
@@ -371,7 +374,6 @@ func (c *controller) ConvertGateway(convertOptions *common.ConvertOptions, wrapp
|
||||
common.IncrementInvalidIngress(c.options.ClusterId, common.EmptyRule)
|
||||
return fmt.Errorf("invalid ingress rule %s:%s in cluster %s, either `defaultBackend` or `rules` must be specified", cfg.Namespace, cfg.Name, c.options.ClusterId)
|
||||
}
|
||||
|
||||
for _, rule := range ingressV1Beta.Rules {
|
||||
// Need create builder for every rule.
|
||||
domainBuilder := &common.IngressDomainBuilder{
|
||||
@@ -422,13 +424,32 @@ func (c *controller) ConvertGateway(convertOptions *common.ConvertOptions, wrapp
|
||||
|
||||
// Get tls secret matching the rule host
|
||||
secretName := extractTLSSecretName(rule.Host, ingressV1Beta.TLS)
|
||||
secretNamespace := cfg.Namespace
|
||||
if secretName != "" {
|
||||
if httpsCredentialConfig != nil && httpsCredentialConfig.FallbackForInvalidSecret {
|
||||
_, err := c.secretController.Lister().Secrets(secretNamespace).Get(secretName)
|
||||
if err != nil {
|
||||
if k8serrors.IsNotFound(err) {
|
||||
// If there is no matching secret, try to get it from configmap.
|
||||
secretName = httpsCredentialConfig.MatchSecretNameByDomain(rule.Host)
|
||||
secretNamespace = c.options.SystemNamespace
|
||||
}
|
||||
}
|
||||
}
|
||||
} else {
|
||||
// If there is no matching secret, try to get it from configmap.
|
||||
if httpsCredentialConfig != nil {
|
||||
secretName = httpsCredentialConfig.MatchSecretNameByDomain(rule.Host)
|
||||
secretNamespace = c.options.SystemNamespace
|
||||
}
|
||||
}
|
||||
if secretName == "" {
|
||||
// There no matching secret, so just skip.
|
||||
continue
|
||||
}
|
||||
|
||||
domainBuilder.Protocol = common.HTTPS
|
||||
domainBuilder.SecretName = path.Join(c.options.ClusterId, cfg.Namespace, secretName)
|
||||
domainBuilder.SecretName = path.Join(c.options.ClusterId, secretNamespace, secretName)
|
||||
|
||||
// There is a matching secret and the gateway has already a tls secret.
|
||||
// We should report the duplicated tls secret event.
|
||||
@@ -450,7 +471,7 @@ func (c *controller) ConvertGateway(convertOptions *common.ConvertOptions, wrapp
|
||||
Hosts: []string{rule.Host},
|
||||
Tls: &networking.ServerTLSSettings{
|
||||
Mode: networking.ServerTLSSettings_SIMPLE,
|
||||
CredentialName: credentials.ToKubernetesIngressResource(c.options.RawClusterId, cfg.Namespace, secretName),
|
||||
CredentialName: credentials.ToKubernetesIngressResource(c.options.RawClusterId, secretNamespace, secretName),
|
||||
},
|
||||
})
|
||||
|
||||
@@ -879,15 +900,28 @@ func (c *controller) storeBackendTrafficPolicy(wrapper *common.WrapperConfig, ba
|
||||
}
|
||||
if common.ValidateBackendResource(backend.Resource) && wrapper.AnnotationsConfig.Destination != nil {
|
||||
for _, dest := range wrapper.AnnotationsConfig.Destination.McpDestination {
|
||||
portNumber := dest.Destination.GetPort().GetNumber()
|
||||
serviceKey := common.ServiceKey{
|
||||
Namespace: "mcp",
|
||||
Name: dest.Destination.Host,
|
||||
Port: int32(portNumber),
|
||||
ServiceFQDN: dest.Destination.Host,
|
||||
}
|
||||
if _, exist := store[serviceKey]; !exist {
|
||||
store[serviceKey] = &common.WrapperTrafficPolicy{
|
||||
TrafficPolicy: &networking.TrafficPolicy{},
|
||||
WrapperConfig: wrapper,
|
||||
if serviceKey.Port != 0 {
|
||||
store[serviceKey] = &common.WrapperTrafficPolicy{
|
||||
PortTrafficPolicy: &networking.TrafficPolicy_PortTrafficPolicy{
|
||||
Port: &networking.PortSelector{
|
||||
Number: uint32(serviceKey.Port),
|
||||
},
|
||||
},
|
||||
WrapperConfig: wrapper,
|
||||
}
|
||||
} else {
|
||||
store[serviceKey] = &common.WrapperTrafficPolicy{
|
||||
TrafficPolicy: &networking.TrafficPolicy{},
|
||||
WrapperConfig: wrapper,
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -1279,8 +1313,10 @@ func createRuleKey(annots map[string]string, hostAndPath string) string {
|
||||
if idx := strings.Index(k, annotations.MatchHeader); idx != -1 {
|
||||
key := k[start:idx] + k[idx+len(annotations.MatchHeader)+1:]
|
||||
headers = append(headers, [2]string{key, val})
|
||||
}
|
||||
if idx := strings.Index(k, annotations.MatchQuery); idx != -1 {
|
||||
} else if idx := strings.Index(k, annotations.MatchPseudoHeader); idx != -1 {
|
||||
key := k[start:idx] + ":" + k[idx+len(annotations.MatchPseudoHeader)+1:]
|
||||
headers = append(headers, [2]string{key, val})
|
||||
} else if idx := strings.Index(k, annotations.MatchQuery); idx != -1 {
|
||||
key := k[start:idx] + k[idx+len(annotations.MatchQuery)+1:]
|
||||
params = append(params, [2]string{key, val})
|
||||
}
|
||||
|
||||
@@ -334,7 +334,7 @@ func testConvertGateway(t *testing.T, c common.IngressController) {
|
||||
}
|
||||
|
||||
for _, testcase := range testcases {
|
||||
err := c.ConvertGateway(testcase.input.options, testcase.input.wrapperConfig)
|
||||
err := c.ConvertGateway(testcase.input.options, testcase.input.wrapperConfig, nil)
|
||||
if err != nil {
|
||||
require.Equal(t, testcase.expectNoError, false)
|
||||
} else {
|
||||
@@ -1302,15 +1302,18 @@ func TestCreateRuleKey(t *testing.T) {
|
||||
}
|
||||
|
||||
annots := annotations.Annotations{
|
||||
buildHigressAnnotationKey(annotations.MatchMethod): "GET PUT",
|
||||
buildHigressAnnotationKey("exact-" + annotations.MatchHeader + "-abc"): "123",
|
||||
buildHigressAnnotationKey("prefix-" + annotations.MatchHeader + "-def"): "456",
|
||||
buildHigressAnnotationKey("exact-" + annotations.MatchQuery + "-region"): "beijing",
|
||||
buildHigressAnnotationKey("prefix-" + annotations.MatchQuery + "-user-id"): "user-",
|
||||
buildHigressAnnotationKey(annotations.MatchMethod): "GET PUT",
|
||||
buildHigressAnnotationKey("exact-" + annotations.MatchHeader + "-abc"): "123",
|
||||
buildHigressAnnotationKey("prefix-" + annotations.MatchHeader + "-def"): "456",
|
||||
buildHigressAnnotationKey("exact-" + annotations.MatchPseudoHeader + "-authority"): "foo.bar.com",
|
||||
buildHigressAnnotationKey("prefix-" + annotations.MatchPseudoHeader + "-scheme"): "htt",
|
||||
buildHigressAnnotationKey("exact-" + annotations.MatchQuery + "-region"): "beijing",
|
||||
buildHigressAnnotationKey("prefix-" + annotations.MatchQuery + "-user-id"): "user-",
|
||||
}
|
||||
expect := "higress.com-prefix-/foo" + sep + //host-pathType-path
|
||||
"GET PUT" + sep + // method
|
||||
"exact-abc\t123" + "\n" + "prefix-def\t456" + sep + // header
|
||||
"exact-:authority\tfoo.bar.com" + "\n" + "exact-abc\t123" + "\n" +
|
||||
"prefix-:scheme\thtt" + "\n" + "prefix-def\t456" + sep + // header
|
||||
"exact-region\tbeijing" + "\n" + "prefix-user-id\tuser-" + sep // params
|
||||
|
||||
key := createRuleKey(annots, wrapperHttpRoute.PathFormat())
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user