mirror of
https://github.com/alibaba/higress.git
synced 2026-06-09 12:47:28 +08:00
feat: support github provider for oidc wasm plugin (#1639)
This commit is contained in:
@@ -29,6 +29,7 @@ Plugin execution priority: `350`
|
||||
| client_secret | string | The OAuth Client Secret | |
|
||||
| provider | string | OAuth provider | oidc |
|
||||
| pass_authorization_header | bool | Pass OIDC IDToken to upstream via Authorization Bearer header | true |
|
||||
| pass_access_token | bool | pass OIDC Access Token to upstream via X-Forwarded-Access-Token header. | False |
|
||||
| oidc_issuer_url | string | The OpenID Connect issuer URL, e.g. `"https://dev-o43xb1mz7ya7ach4.us.auth0.com"` | |
|
||||
| oidc_verifier_request_timeout | uint32 | OIDC verifier discovery request timeout | 2000(ms) |
|
||||
| scope | string | OAuth scope specification | |
|
||||
@@ -254,6 +255,54 @@ Directly login using a RAM user or click the main account login.
|
||||
#### Successful Login Redirects to Service Page
|
||||
|
||||
|
||||
### Github Configuration Example
|
||||
|
||||
#### Step 1: Configure Github OAuth App
|
||||
|
||||
Create a new OAuth App: https://github.com/settings/developers
|
||||
|
||||
#### Step 2: Higress Configure Service Source
|
||||
|
||||
* Create a DNS service with the source address set to github.com.
|
||||
* Create a DNS service with the source address set to api.github.com (used to validate the access token in the OIDC flow).
|
||||
|
||||

|
||||
|
||||
#### Step 3: OIDC Service HTTPS Protocol
|
||||
Configure Ingress for the two created DNS services by referring to Step 3 of Auth0.
|
||||
|
||||
#### Step 4: Wasm Plugin Configuration
|
||||
|
||||
```yaml
|
||||
redirect_url: 'http://foo.bar.com/oauth2/callback'
|
||||
provider: github
|
||||
oidc_issuer_url: 'https://github.com/'
|
||||
pass_access_token: true
|
||||
client_id: 'XXXXXXXXXXXXXXXX'
|
||||
client_secret: 'XXXXXXXXXXXXXXXX'
|
||||
scope: 'user repo'
|
||||
cookie_secret: 'nqavJrGvRmQxWwGNptLdyUVKcBNZ2b18Guc1n_8DCfY='
|
||||
service_name: 'github.dns'
|
||||
service_port: 443
|
||||
validate_service_name: 'api.dns'
|
||||
validate_service_port: 443
|
||||
match_type: 'whitelist'
|
||||
match_list:
|
||||
- match_rule_domain: '*.bar.com'
|
||||
match_rule_path: '/headers'
|
||||
match_rule_type: 'prefix'
|
||||
```
|
||||
|
||||
#### Access Service Page; Redirect if Not Logged In
|
||||
|
||||

|
||||
|
||||
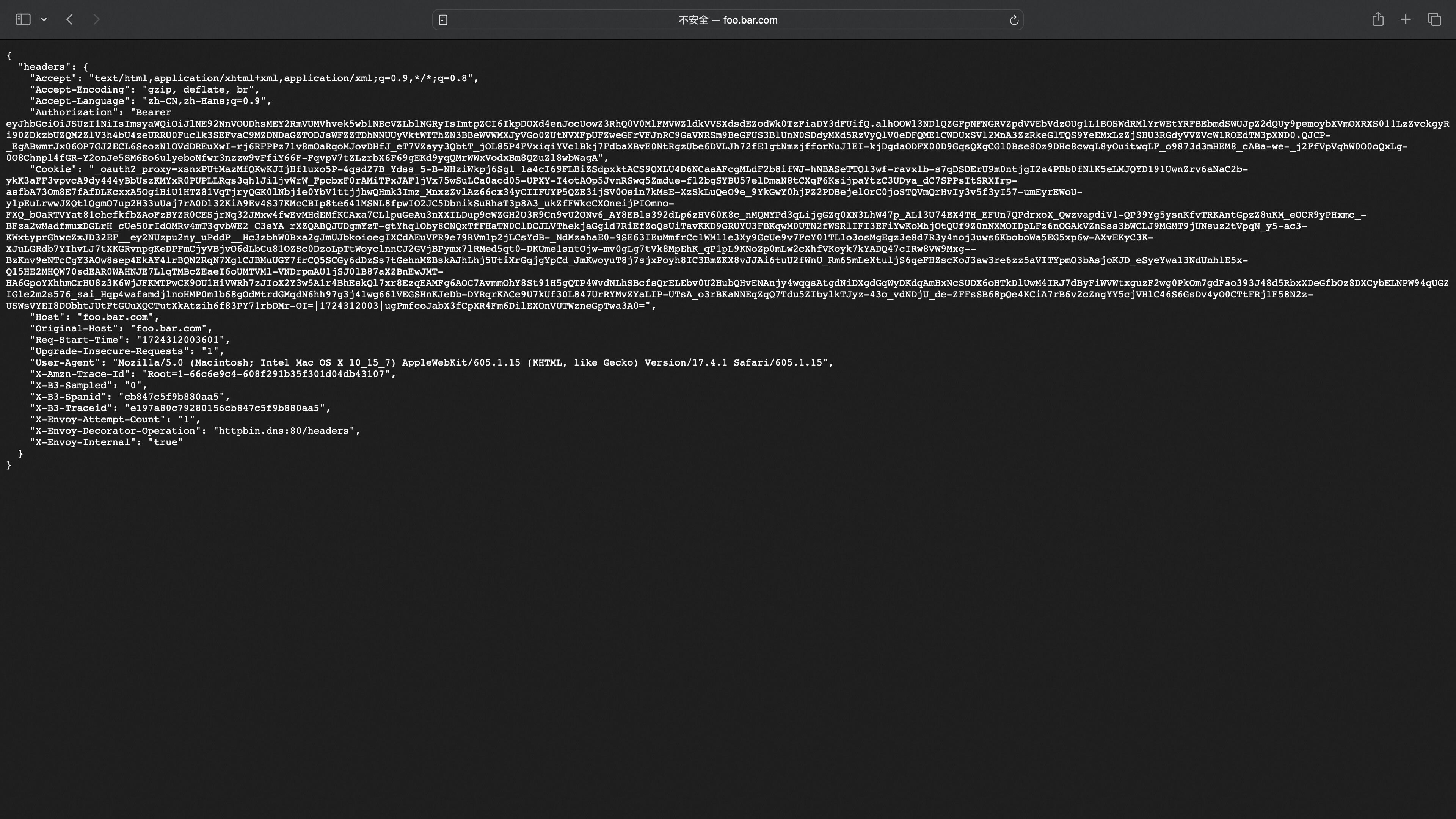
#### Successful Login Redirects to Service Page
|
||||
|
||||
With pass_access_token=true configured, the access_token will be included in the X-Forwarded-Access-Token header.
|
||||
|
||||

|
||||
|
||||
### OIDC Flow Diagram
|
||||
<p align="center">
|
||||
<img src="https://gw.alicdn.com/imgextra/i3/O1CN01TJSh9c1VwR61Q2nek_!!6000000002717-55-tps-1807-2098.svg" alt="oidc_process" width="600" />
|
||||
|
||||
Reference in New Issue
Block a user